- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
LATEST NEWS
- 06 / 12 : 7:00 am : Ransomware Gang TellYouThePass Exploits PHP Vulnerability – Source: www.databreachtoday.com
- 06 / 12 : 7:00 am : Chinese-Made Biometric Access System Has 24 Vulnerabilities – Source: www.databreachtoday.com
- 06 / 12 : 7:00 am : Cleveland Cyber Incident Prompts Shutdown of City IT Systems – Source: www.databreachtoday.com
- 06 / 12 : 7:00 am : Dutch Agency Renews Warning of Chinese Fortigate Campaign – Source: www.databreachtoday.com
- 06 / 11 : 6:49 am : ChatGPT Integration Fortifies Apple’s Siri and Writing Tools – Source: www.databreachtoday.com
- 06 / 11 : 6:49 am : FCC Advances BGP Security Rules for Broadband Providers – Source: www.databreachtoday.com
- 06 / 11 : 6:49 am : Lawmakers: UHG Violating HIPAA Breach Notification Rule – Source: www.databreachtoday.com
- 06 / 11 : 6:49 am : Psychological Strategies for Bridging the IT-OT Divide – Source: www.databreachtoday.com
- 06 / 11 : 6:49 am : Microsoft Now Promises Extra Security for AI-Driven Recall – Source: www.databreachtoday.com
- 06 / 10 : 9:00 am : Hackers Claim They Breached Telecom Firm in Singapore – Source: www.databreachtoday.com
- 06 / 09 : 9:00 am : Critical PHP Vulnerability Threatens Windows Servers – Source: www.databreachtoday.com
- 06 / 08 : 9:00 am : ISMG Editors: Infosecurity Europe Conference 2024 Wrap-Up – Source: www.databreachtoday.com
- 06 / 08 : 9:00 am : Hypr Secures $30M to Expand Identity Protection Platform – Source: www.databreachtoday.com
- 06 / 08 : 9:00 am : CISA Planning JCDC Overhaul as Experts Criticize Slow Start – Source: www.databreachtoday.com
- 06 / 08 : 9:00 am : Qilin RaaS Group Believed to Be Behind Synnovis, NHS Attack – Source: www.databreachtoday.com
- 06 / 08 : 9:00 am : Collaborative Security: The Team Sport Approach – Source: www.databreachtoday.com
- 06 / 08 : 9:00 am : Technical or Nontechnical? Choosing Your Cybersecurity Path – Source: www.databreachtoday.com
- 06 / 07 : 9:00 am : Meta’s AI Model Training Comes Under European Scrutiny – Source: www.databreachtoday.com
- 06 / 07 : 9:00 am : Renewed Info Stealer Campaign Targets Ukrainian Military – Source: www.databreachtoday.com
- 06 / 07 : 9:00 am : Wiz Counters Orca Security’s Patent Infringement Allegations – Source: www.databreachtoday.com
CISO STRATEGICS
CYBER ARCHITECTURE
SOC CSIRT OPERATIONS
CYBERSECURITY TOOLS
CYBERSECURITY VENDORS
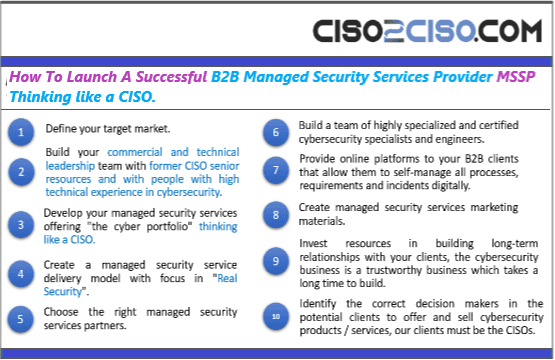
CYBERSECURITY MSSP
CYBER ORGANIZATIONS
CYBER REGULATIONS
EVENTS & CONFERENCES
VULNs & ZERO DAYS
LATEST CYBER NEWS

CISO2CISO Editors' Picks
CISO
STRATEGICS
- CISO Strategics
- CISO Learn & Leadership
- Cybersecurity for C-Levels
- Cybersecurity Trends & Insights
- Cyberseurity Awareness
- Cybercrimen Ecosystem
- Cybersecurity Measure & Metrics
- Cybersecurity Frameworks
- Cybersecurity Policy & Standars
- Fraud
- Information Security
- Osint - Humint
- Privacy
- Risk & Compliance
- Resilience
- Social Engineering
- Supply Chain Security
CYBER
ARCHITECTURE
- API Security
- Application Security
- Blockchain Security
- Cloud Security
- Data Security
- Defense in Depth
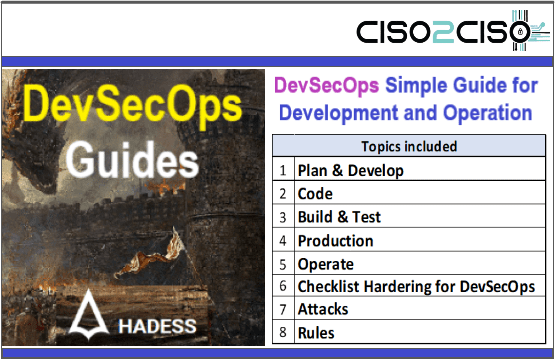
- DevSecOps
- Endpoint Security
- IA Security
- IOT Security
- MAC-OS Security
- Metaverse Security
- Micro segmentation
- Mitre Att&ck
- Mobile & 5G Security
- Network Security
- OT Security
- OWASP Security
- Perimeter Security
- SAP Security
- Telco & Carrier Security
- Zero Trust Security
SOC CSIRT
OPERATIONS
- Cyber Incidents & Attacks Notepad
- CSIRT Operations
- Data Leak & Breach Incidents Notepad
- DDOS Attacks
- DFIR - Forensics & Incident Response
- Dark & Deep Web
- SOC Operations
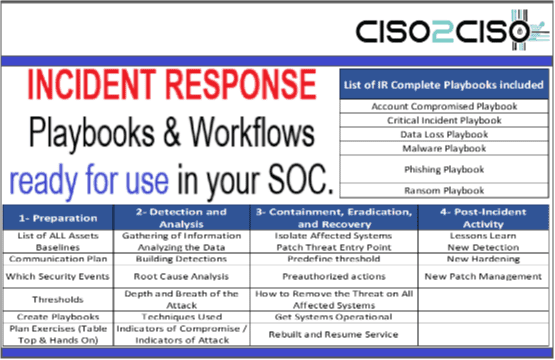
- SIEM Use Cases & Playbooks
- SOAR Authomation & Playbooks
- Malware & Ransomware
- Red - Blue & Purple Teams Operations
- Threat Intelligence
- Threat Hunting
- Vulnerabilities

CYBER
ORGs
- CCN-EU
- CSA
- CIS
- CISA
- DHS-US
- ENISA
- ISACA
- INCIBE-EU
- Mitre Att&ack
- NSA
- NIST Security
- SANS
- WEF
CYBER
CONFERENCES
Latest Published Posts
CYBERSECURITY
VENDORS
- Akamai
- A10 Networks
- Blackberry Cylance
- Cisco
- Cyberark
- Cloudfare
- Crowdstrike
- Checkpoint
- F5 Networks
- FyreEye
- Fortinet
- Guardicore
- IBM
- Kaspersky
- Mcafee - Trellix
- Mandiant
- Maltego
- Microsoft
- Netscope
- Palo Alto Networks
- RSA Security
- Redhat
- Splunk
- Symantec
- Tenable
- Trendmicro
CYBERSECURITY
MSSP
- Accenture
- Attos
- AT&T Cybersecurity
- BT Security
- BASE 4 - Hispam
- Deloitte
- Entelgy Security
- KPMG
- NTT Security
- Novared - Hispam
- Neosecure - Hispam
- Orange Cyberdefense
- PwC
- Telefonica Tech
- Thales
- Verizon Security
CISO2CISO Editors' Picks
LATEST CYBER NEWS
Latest Published Posts
CISO2CISO Editors' Picks
Latest Published Posts
Users Most Viewed Posts
TOP Featured POSTS
Views: 643