The Internet Organised Crime Threat Assessment (IOCTA) is a strategic report that provides a law enforcement-centric...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Europol
Online fraud schemes (OFSs) comprise a wide range of criminal activities that are exclusively or primarily...
The impact of quantum computing and quantum technologies on law enforcement Quantum computing and quantum technologies...
The release and widespread use of ChatGPT – a large language model (LLM) developed by OpenAI...
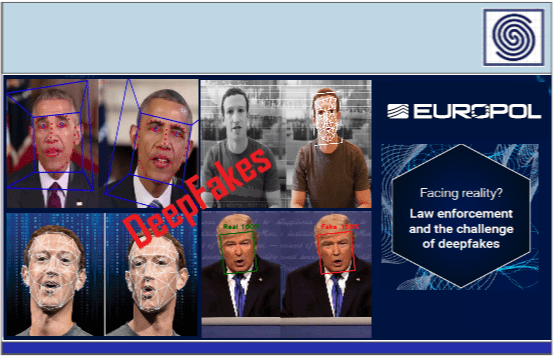
An Observatory Report from the Europol Innovation Lab Today, threat actors are using disinformation campaigns and...
INTRODUCTIONThe release and widespread use of ChatGPT – a large language model (LLM) developed by OpenAI...