- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
LATEST NEWS
- 05 / 15 : 7:00 pm : How to Set Up & Use a VPN on Android (A Step-by-Step Guide) – Source: www.techrepublic.com
- 05 / 15 : 7:00 pm : What Is the Dark Web? – Source: www.techrepublic.com
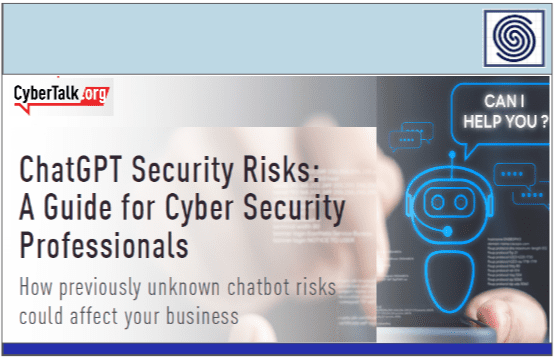
- 05 / 15 : 7:00 pm : Quick Glossary: DevSecOps – Source: www.techrepublic.com
- 05 / 15 : 5:01 pm : Improving cyber defense with open source SIEM and XDR – Source: go.theregister.com
- 05 / 15 : 5:01 pm : Microsoft fixes a bug abused in QakBot attacks plus a second under exploit – Source: go.theregister.com
- 05 / 15 : 5:00 pm : Cyber-Attack Disrupts Christie’s $840M Art Auctions – Source: www.infosecurity-magazine.com
- 05 / 15 : 5:00 pm : PDF Exploitation Targets Foxit Reader Users – Source: www.infosecurity-magazine.com
- 05 / 15 : 5:00 pm : NCSC Expands Election Cybersecurity to Safeguard Candidates and Officials – Source: www.infosecurity-magazine.com
- 05 / 15 : 5:00 pm : Google Expands Synthetic Content Watermarking Tool to AI-Generated Text – Source: www.infosecurity-magazine.com
- 05 / 15 : 5:00 pm : Santander Customer Data Compromised Following Third-Party Breach – Source: www.infosecurity-magazine.com
- 05 / 15 : 5:00 pm : Sophos Firewall v20 MR1 is now available – Source: news.sophos.com
- 05 / 15 : 5:00 pm : Making Waves: LATAM Sales Team Clears Beach Debris in Panama – Source: news.sophos.com
- 05 / 15 : 5:00 pm : No mayday call necessary for the year’s fifth Patch Tuesday – Source: news.sophos.com
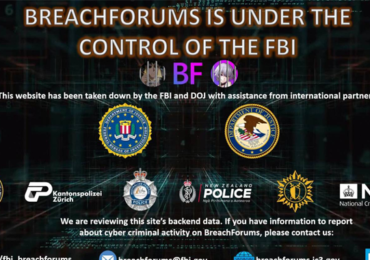
- 05 / 15 : 4:00 pm : FBI Seizes BreachForums Again, Urges Users to Report Criminal Activity – Source:thehackernews.com
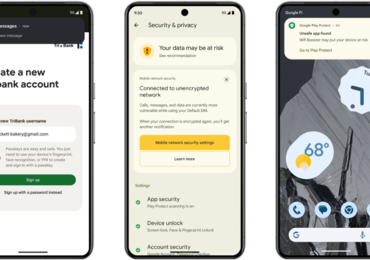
- 05 / 15 : 4:00 pm : Android 15 Rolls Out Advanced Features to Protect Users from Scams and Malicious Apps – Source:thehackernews.com
- 05 / 15 : 4:00 pm : Google Launches AI-Powered Theft and Data Protection Features for Android Devices – Source:thehackernews.com
- 05 / 15 : 4:00 pm : Turla Group Deploys LunarWeb and LunarMail Backdoors in Diplomatic Missions – Source:thehackernews.com
- 05 / 15 : 4:00 pm : (Cyber) Risk = Probability of Occurrence x Damage – Source:thehackernews.com
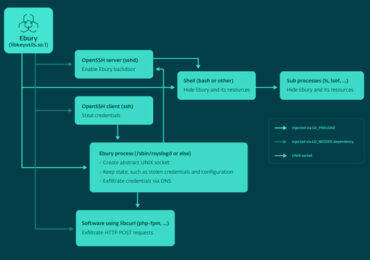
- 05 / 15 : 4:00 pm : Ebury Botnet Malware Compromises 400,000 Linux Servers Over Past 14 Years – Source:thehackernews.com
- 05 / 15 : 4:00 pm : It’s Time to Master the Lift & Shift: Migrating from VMware vSphere to Microsoft Azure – Source:thehackernews.com
CISO STRATEGICS
CYBER ARCHITECTURE
SOC CSIRT OPERATIONS
CYBERSECURITY TOOLS
CYBERSECURITY VENDORS
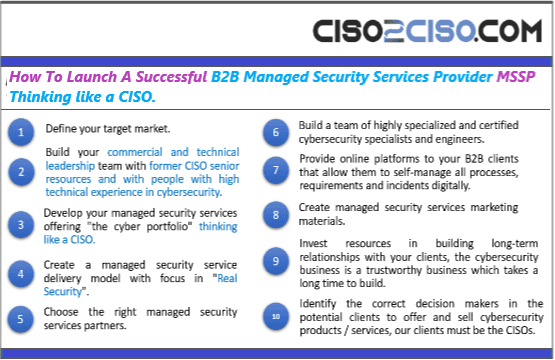
CYBERSECURITY MSSP
CYBER ORGANIZATIONS
CYBER REGULATIONS
EVENTS & CONFERENCES
VULNs & ZERO DAYS
LATEST CYBER NEWS

CISO2CISO Editors' Picks
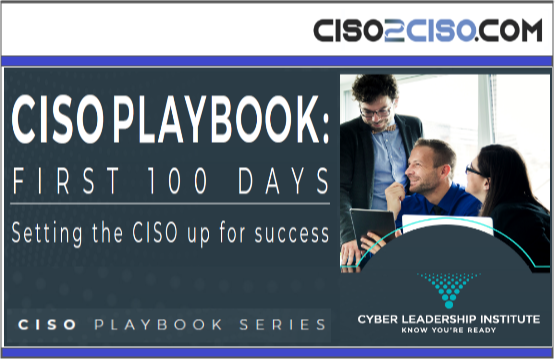
CISO
STRATEGICS
- CISO Strategics
- CISO Learn & Leadership
- Cybersecurity for C-Levels
- Cybersecurity Trends & Insights
- Cyberseurity Awareness
- Cybercrimen Ecosystem
- Cybersecurity Measure & Metrics
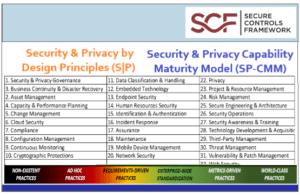
- Cybersecurity Frameworks
- Cybersecurity Policy & Standars
- Fraud
- Information Security
- Osint - Humint
- Privacy
- Risk & Compliance
- Resilience
- Social Engineering
- Supply Chain Security
CYBER
ARCHITECTURE
- API Security
- Application Security
- Blockchain Security
- Cloud Security
- Data Security
- Defense in Depth
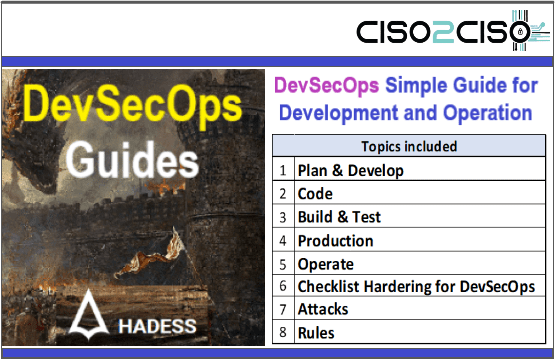
- DevSecOps
- Endpoint Security
- IA Security
- IOT Security
- MAC-OS Security
- Metaverse Security
- Micro segmentation
- Mitre Att&ck
- Mobile & 5G Security
- Network Security
- OT Security
- OWASP Security
- Perimeter Security
- SAP Security
- Telco & Carrier Security
- Zero Trust Security
SOC CSIRT
OPERATIONS
- Cyber Incidents & Attacks Notepad
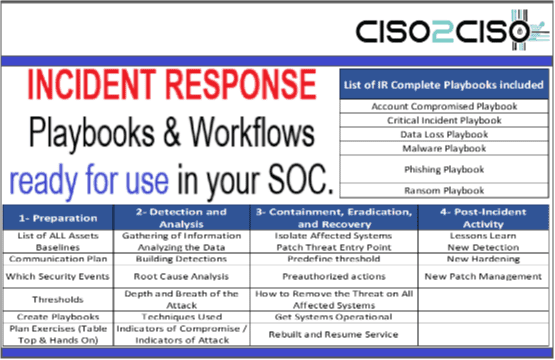
- CSIRT Operations
- Data Leak & Breach Incidents Notepad
- DDOS Attacks
- DFIR - Forensics & Incident Response
- Dark & Deep Web
- SOC Operations
- SIEM Use Cases & Playbooks
- SOAR Authomation & Playbooks
- Malware & Ransomware
- Red - Blue & Purple Teams Operations
- Threat Intelligence
- Threat Hunting
- Vulnerabilities

CYBER
ORGs
- CCN-EU
- CSA
- CIS
- CISA
- DHS-US
- ENISA
- ISACA
- INCIBE-EU
- Mitre Att&ack
- NSA
- NIST Security
- SANS
- WEF
CYBER
CONFERENCES
Latest Published Posts
CYBERSECURITY
VENDORS
- Akamai
- A10 Networks
- Blackberry Cylance
- Cisco
- Cyberark
- Cloudfare
- Crowdstrike
- Checkpoint
- F5 Networks
- FyreEye
- Fortinet
- Guardicore
- IBM
- Kaspersky
- Mcafee - Trellix
- Mandiant
- Maltego
- Microsoft
- Netscope
- Palo Alto Networks
- RSA Security
- Redhat
- Splunk
- Symantec
- Tenable
- Trendmicro
CYBERSECURITY
MSSP
- Accenture
- Attos
- AT&T Cybersecurity
- BT Security
- BASE 4 - Hispam
- Deloitte
- Entelgy Security
- KPMG
- NTT Security
- Novared - Hispam
- Neosecure - Hispam
- Orange Cyberdefense
- PwC
- Telefonica Tech
- Thales
- Verizon Security