- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
LATEST NEWS
- 05 / 14 : 1:01 pm : AFL players call for data protection overhaul as concerns include drug test results – Source: www.theguardian.com
- 05 / 14 : 1:00 pm : DNS Tunneling Abuse Expands to Tracking & Scanning Victims – Source: www.darkreading.com
- 05 / 14 : 1:00 pm : There Is No Cyber Labor Shortage – Source: www.darkreading.com
- 05 / 14 : 1:00 pm : Heartbleed: When Is It Good to Name a Vulnerability? – Source: www.darkreading.com
- 05 / 14 : 12:02 pm : AI is changing the shape of leadership – how can business leaders prepare? – Source: www.cybertalk.org
- 05 / 14 : 12:01 pm : New alert: Logicalis enhances global security services with the launch of Intelligent Security – Source: www.lastwatchdog.com
- 05 / 14 : 12:01 pm : News alert: Criminal IP and Quad9 collaborate to exchange domain and IP threat intelligence – Source: www.lastwatchdog.com
- 05 / 14 : 12:00 pm : ReversingLabs Search Extension for Splunk Enterprise – Source: securityboulevard.com
- 05 / 14 : 12:00 pm : Simplify Certificate Lifecycle Management And Build Security Into OpenShift Kubernetes Engine With AppViewX KUBE+ – Source: securityboulevard.com
- 05 / 14 : 12:00 pm : What you missed at RSA Conference 2024: Key trends and takeaways – Source: securityboulevard.com
- 05 / 14 : 12:00 pm : Sectrio and DigiGlass inaugurate State-of-the-Art OT/ICS SOC with Device Testing Lab in the UAE – Source: securityboulevard.com
- 05 / 14 : 12:00 pm : What are Machine Credentials, And Why Are They Important to Secure in Your Organization? – Source: securityboulevard.com
- 05 / 14 : 12:00 pm : What are Service Accounts, and why are they Important to Secure? – Source: securityboulevard.com
- 05 / 14 : 12:00 pm : Several Vulnerabilities Addressed in Ubuntu 24.04 – Source: securityboulevard.com
- 05 / 14 : 12:00 pm : What are OAuth Tokens, and why are they important to Secure? – Source: securityboulevard.com
- 05 / 14 : 12:00 pm : Protect your Hardware Security Module | Blog | Code Intelligence – Source: securityboulevard.com
- 05 / 14 : 12:00 pm : Dropbox Sign Breach: Threat Actors Access User Information – Source: securityboulevard.com
- 05 / 14 : 9:00 am : Incident response analyst report 2023 – Source: securelist.com
- 05 / 14 : 6:01 am : FCC Names and Shames First Robocall Threat Actor – Source: www.infosecurity-magazine.com
- 05 / 14 : 6:00 am : Phorpiex botnet sent millions of phishing emails to deliver LockBit Black ransomware – Source: securityaffairs.com
CISO STRATEGICS
CYBER ARCHITECTURE
SOC CSIRT OPERATIONS
CYBERSECURITY TOOLS
CYBERSECURITY VENDORS
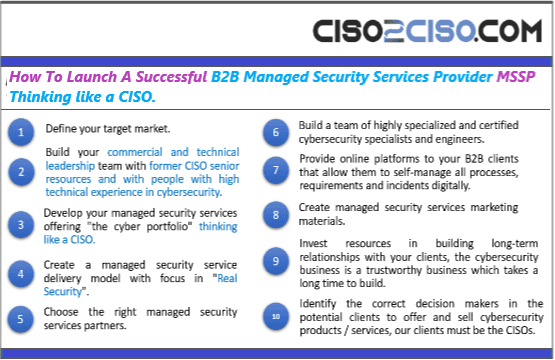
CYBERSECURITY MSSP
CYBER ORGANIZATIONS
CYBER REGULATIONS
EVENTS & CONFERENCES
VULNs & ZERO DAYS
LATEST CYBER NEWS

CISO2CISO Editors' Picks
CISO
STRATEGICS
- CISO Strategics
- CISO Learn & Leadership
- Cybersecurity for C-Levels
- Cybersecurity Trends & Insights
- Cyberseurity Awareness
- Cybercrimen Ecosystem
- Cybersecurity Measure & Metrics
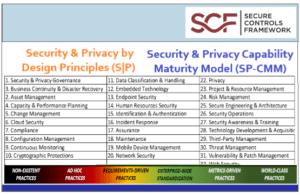
- Cybersecurity Frameworks
- Cybersecurity Policy & Standars
- Fraud
- Information Security
- Osint - Humint
- Privacy
- Risk & Compliance
- Resilience
- Social Engineering
- Supply Chain Security
CYBER
ARCHITECTURE
- API Security
- Application Security
- Blockchain Security
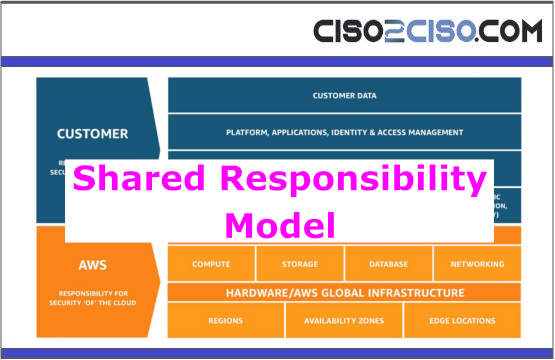
- Cloud Security
- Data Security
- Defense in Depth
- DevSecOps
- Endpoint Security
- IA Security
- IOT Security
- MAC-OS Security
- Metaverse Security
- Micro segmentation
- Mitre Att&ck
- Mobile & 5G Security
- Network Security
- OT Security
- OWASP Security
- Perimeter Security
- SAP Security
- Telco & Carrier Security
- Zero Trust Security
SOC CSIRT
OPERATIONS
- Cyber Incidents & Attacks Notepad
- CSIRT Operations
- Data Leak & Breach Incidents Notepad
- DDOS Attacks
- DFIR - Forensics & Incident Response
- Dark & Deep Web
- SOC Operations
- SIEM Use Cases & Playbooks
- SOAR Authomation & Playbooks
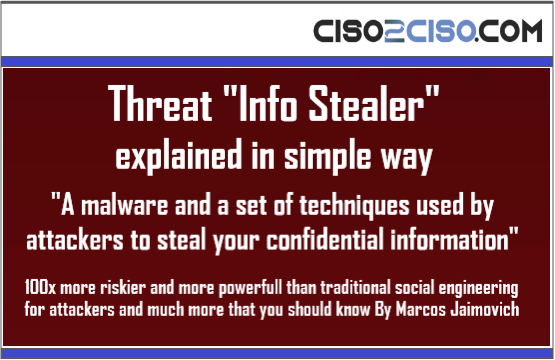
- Malware & Ransomware
- Red - Blue & Purple Teams Operations
- Threat Intelligence
- Threat Hunting
- Vulnerabilities

CYBER
ORGs
- CCN-EU
- CSA
- CIS
- CISA
- DHS-US
- ENISA
- ISACA
- INCIBE-EU
- Mitre Att&ack
- NSA
- NIST Security
- SANS
- WEF
CYBER
CONFERENCES
Latest Published Posts
CYBERSECURITY
VENDORS
- Akamai
- A10 Networks
- Blackberry Cylance
- Cisco
- Cyberark
- Cloudfare
- Crowdstrike
- Checkpoint
- F5 Networks
- FyreEye
- Fortinet
- Guardicore
- IBM
- Kaspersky
- Mcafee - Trellix
- Mandiant
- Maltego
- Microsoft
- Netscope
- Palo Alto Networks
- RSA Security
- Redhat
- Splunk
- Symantec
- Tenable
- Trendmicro
CYBERSECURITY
MSSP
- Accenture
- Attos
- AT&T Cybersecurity
- BT Security
- BASE 4 - Hispam
- Deloitte
- Entelgy Security
- KPMG
- NTT Security
- Novared - Hispam
- Neosecure - Hispam
- Orange Cyberdefense
- PwC
- Telefonica Tech
- Thales
- Verizon Security