- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
LATEST NEWS
- 05 / 11 : 12:00 pm : How to Get PCI Compliance Certification? Steps to Obtain it – Source: securityboulevard.com
- 05 / 11 : 12:00 pm : What is Wireless Network Penetration Testing? [Explained] – Source: securityboulevard.com
- 05 / 11 : 12:00 pm : Cloud Monitor Scans For Risky Video Files in Google Drive/OneDrive – Source: securityboulevard.com
- 05 / 11 : 12:00 pm : Dell Hell: 49 Million Customers’ Information Leaked – Source: securityboulevard.com
- 05 / 11 : 12:00 pm : Emerald Divide Uses GenAI to Exploit Social, Political Divisions in Israel Using Disinformation – Source: securityboulevard.com
- 05 / 11 : 12:00 pm : Healthcare Software Company Gains Comprehensive Visibility with LogRhythm Axon – Source: securityboulevard.com
- 05 / 11 : 12:00 pm : USENIX Security ’23 – Authenticated Private Information Retrieval – Source: securityboulevard.com
- 05 / 11 : 12:00 pm : Dell Data Breach Could Affect 49 Million Customers – Source: securityboulevard.com
- 05 / 11 : 12:00 pm : Cybersecurity Salary: How Much Can You Earn? – Source: securityboulevard.com
- 05 / 11 : 12:00 pm : Daniel Stori’s ‘tar.gz’ – Source: securityboulevard.com
- 05 / 11 : 9:00 am : 10 ways generative AI drives stronger security outcomes – Source: www.cybertalk.org
- 05 / 11 : 6:00 am : ISMG Editors: RSA Conference 2024 Wrap-Up – Source: www.databreachtoday.com
- 05 / 11 : 6:00 am : Hackers Steal Credit Card Data of Deal-Seeking Shoppers – Source: www.databreachtoday.com
- 05 / 11 : 6:00 am : Live Webinar | Correcting your Cyber Security Posture with the Board: Data, Metrics and Lessons from 2023 – Source: www.databreachtoday.com
- 05 / 11 : 6:00 am : Solving the Fractured Data Problem in Exposure Management – Source: www.databreachtoday.com
- 05 / 11 : 6:00 am : Ascension Diverts Emergency Patients, Postpones Care – Source: www.databreachtoday.com
- 05 / 11 : 5:00 am : MoD contractor hacked by China failed to report breach for months – Source: www.theguardian.com
- 05 / 11 : 5:00 am : Red Sea Crisis and the Risk of Cyber Fallout – Source: www.cyberdefensemagazine.com
- 05 / 11 : 3:02 am : How Can Businesses Defend Themselves Against Common Cyberthreats? – Source: www.techrepublic.com
- 05 / 11 : 3:01 am : Iran most likely to launch destructive cyber-attack against US – ex-Air Force intel analyst – Source: go.theregister.com
CISO STRATEGICS
CYBER ARCHITECTURE
SOC CSIRT OPERATIONS
CYBERSECURITY TOOLS
CYBERSECURITY VENDORS
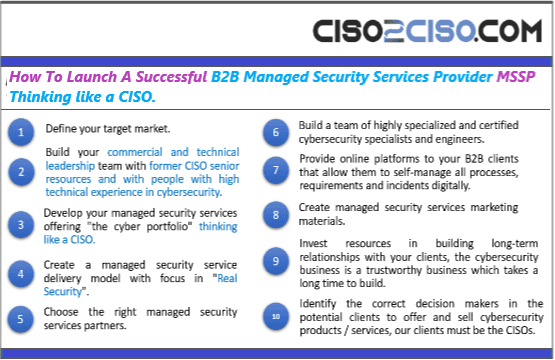
CYBERSECURITY MSSP
CYBER ORGANIZATIONS
CYBER REGULATIONS
EVENTS & CONFERENCES
VULNs & ZERO DAYS
LATEST CYBER NEWS

CISO2CISO Editors' Picks
CISO
STRATEGICS
- CISO Strategics
- CISO Learn & Leadership
- Cybersecurity for C-Levels
- Cybersecurity Trends & Insights
- Cyberseurity Awareness
- Cybercrimen Ecosystem
- Cybersecurity Measure & Metrics
- Cybersecurity Frameworks
- Cybersecurity Policy & Standars
- Fraud
- Information Security
- Osint - Humint
- Privacy
- Risk & Compliance
- Resilience
- Social Engineering
- Supply Chain Security
CYBER
ARCHITECTURE
- API Security
- Application Security
- Blockchain Security
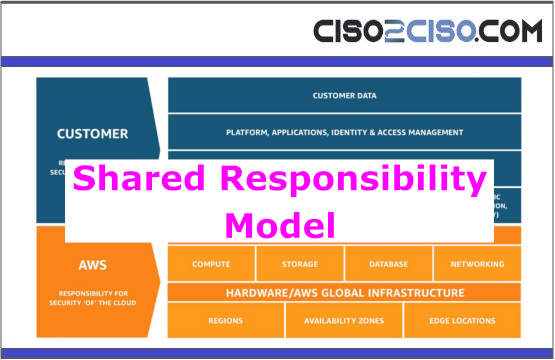
- Cloud Security
- Data Security
- Defense in Depth
- DevSecOps
- Endpoint Security
- IA Security
- IOT Security
- MAC-OS Security
- Metaverse Security
- Micro segmentation
- Mitre Att&ck
- Mobile & 5G Security
- Network Security
- OT Security
- OWASP Security
- Perimeter Security
- SAP Security
- Telco & Carrier Security
- Zero Trust Security
SOC CSIRT
OPERATIONS
- Cyber Incidents & Attacks Notepad
- CSIRT Operations
- Data Leak & Breach Incidents Notepad
- DDOS Attacks
- DFIR - Forensics & Incident Response
- Dark & Deep Web
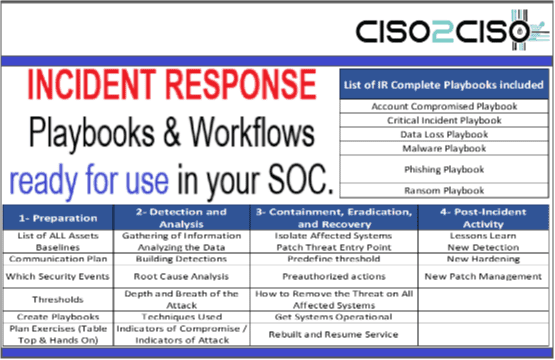
- SOC Operations
- SIEM Use Cases & Playbooks
- SOAR Authomation & Playbooks
- Malware & Ransomware
- Red - Blue & Purple Teams Operations
- Threat Intelligence
- Threat Hunting
- Vulnerabilities

CYBER
ORGs
- CCN-EU
- CSA
- CIS
- CISA
- DHS-US
- ENISA
- ISACA
- INCIBE-EU
- Mitre Att&ack
- NSA
- NIST Security
- SANS
- WEF
CYBER
CONFERENCES
Latest Published Posts
CYBERSECURITY
VENDORS
- Akamai
- A10 Networks
- Blackberry Cylance
- Cisco
- Cyberark
- Cloudfare
- Crowdstrike
- Checkpoint
- F5 Networks
- FyreEye
- Fortinet
- Guardicore
- IBM
- Kaspersky
- Mcafee - Trellix
- Mandiant
- Maltego
- Microsoft
- Netscope
- Palo Alto Networks
- RSA Security
- Redhat
- Splunk
- Symantec
- Tenable
- Trendmicro
CYBERSECURITY
MSSP
- Accenture
- Attos
- AT&T Cybersecurity
- BT Security
- BASE 4 - Hispam
- Deloitte
- Entelgy Security
- KPMG
- NTT Security
- Novared - Hispam
- Neosecure - Hispam
- Orange Cyberdefense
- PwC
- Telefonica Tech
- Thales
- Verizon Security