- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
LATEST NEWS
- 05 / 08 : 12:00 am : #RSAC: Two-Thirds of Organizations Failing to Address AI Risks, ISACA Finds – Source: www.infosecurity-magazine.com
- 05 / 08 : 12:00 am : RSAC: Decoding US Government Plans to Shift the Software Security Burden – Source: www.infosecurity-magazine.com
- 05 / 08 : 12:00 am : RSAC: Log4J Still Among Top Exploited Vulnerabilities, Cato Finds – Source: www.infosecurity-magazine.com
- 05 / 08 : 12:00 am : Ransomware Strikes Wichita, Services Disrupted – Source: www.infosecurity-magazine.com
- 05 / 08 : 12:00 am : LockBit Leader aka LockBitSupp Identity Revealed – Source: www.infosecurity-magazine.com
- 05 / 08 : 12:00 am : RSAC: Three Battle-Tested Tips for Surviving a Cyber-Attack – Source: www.infosecurity-magazine.com
- 05 / 08 : 12:00 am : Report Shows AI Fraud, Deepfakes Are Top Challenges For Banks – Source: www.infosecurity-magazine.com
- 05 / 08 : 12:00 am : BTC-e $9bn Crypto-Money Launderer Pleads Guilty – Source: www.infosecurity-magazine.com
- 05 / 08 : 12:00 am : China Suspected After Major MoD Payroll Breach – Source: www.infosecurity-magazine.com
- 05 / 08 : 12:00 am : Law enforcement agencies identified LockBit ransomware admin and sanctioned him – Source: securityaffairs.com
- 05 / 08 : 12:00 am : MITRE attributes the recent attack to China-linked UNC5221 – Source: securityaffairs.com
- 05 / 08 : 12:00 am : Alexander Vinnik, the operator of BTC-e exchange, pleaded guilty to money laundering – Source: securityaffairs.com
- 05 / 07 : 7:00 pm : U.S. Charges Russian Man as Boss of LockBit Ransomware Group – Source: krebsonsecurity.com
- 05 / 07 : 6:00 pm : Does CISA’s KEV Catalog Speed Up Remediation? – Source: www.darkreading.com
- 05 / 07 : 6:00 pm : What’s the Future Path for CISOs? – Source: www.darkreading.com
- 05 / 07 : 6:00 pm : City of Wichita Public Services Disrupted After Ransomware Attack – Source: www.darkreading.com
- 05 / 07 : 6:00 pm : Feds: Reducing AI Risks Requires Visibility & Better Planning – Source: www.darkreading.com
- 05 / 07 : 6:00 pm : Spies Among Us: Insider Threats in Open Source Environments – Source: www.darkreading.com
- 05 / 07 : 6:00 pm : Blinken: Digital Solidarity Is ‘North Star’ for US Policy – Source: www.darkreading.com
- 05 / 07 : 6:00 pm : Anetac Targets Service Account Security – Source: www.darkreading.com
CISO STRATEGICS
CYBER ARCHITECTURE
SOC CSIRT OPERATIONS
CYBERSECURITY TOOLS
CYBERSECURITY VENDORS
CYBERSECURITY MSSP
CYBER ORGANIZATIONS
CYBER REGULATIONS
EVENTS & CONFERENCES
VULNs & ZERO DAYS
LATEST CYBER NEWS

CISO2CISO Editors' Picks
CISO
STRATEGICS
- CISO Strategics
- CISO Learn & Leadership
- Cybersecurity for C-Levels
- Cybersecurity Trends & Insights
- Cyberseurity Awareness
- Cybercrimen Ecosystem
- Cybersecurity Measure & Metrics
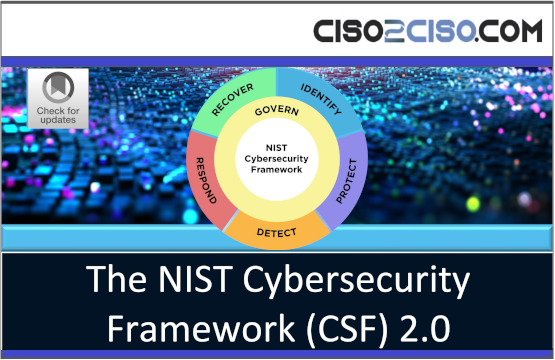
- Cybersecurity Frameworks
- Cybersecurity Policy & Standars
- Fraud
- Information Security
- Osint - Humint
- Privacy
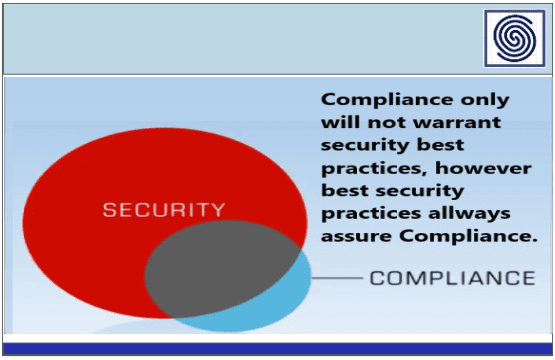
- Risk & Compliance
- Resilience
- Social Engineering
- Supply Chain Security
CYBER
ARCHITECTURE
- API Security
- Application Security
- Blockchain Security
- Cloud Security
- Data Security
- Defense in Depth
- DevSecOps
- Endpoint Security
- IA Security
- IOT Security
- MAC-OS Security
- Metaverse Security
- Micro segmentation
- Mitre Att&ck
- Mobile & 5G Security
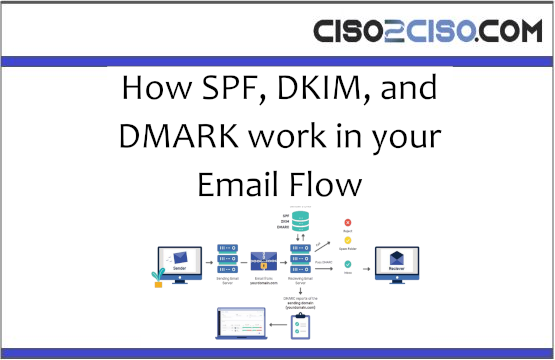
- Network Security
- OT Security
- OWASP Security
- Perimeter Security
- SAP Security
- Telco & Carrier Security
- Zero Trust Security
SOC CSIRT
OPERATIONS
- Cyber Incidents & Attacks Notepad
- CSIRT Operations
- Data Leak & Breach Incidents Notepad
- DDOS Attacks
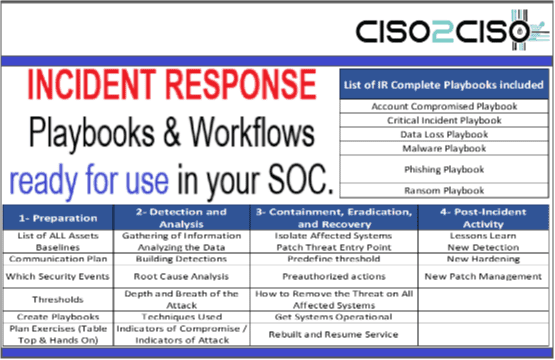
- DFIR - Forensics & Incident Response
- Dark & Deep Web
- SOC Operations
- SIEM Use Cases & Playbooks
- SOAR Authomation & Playbooks
- Malware & Ransomware
- Red - Blue & Purple Teams Operations
- Threat Intelligence
- Threat Hunting
- Vulnerabilities

CYBER
ORGs
- CCN-EU
- CSA
- CIS
- CISA
- DHS-US
- ENISA
- ISACA
- INCIBE-EU
- Mitre Att&ack
- NSA
- NIST Security
- SANS
- WEF
CYBER
CONFERENCES
Latest Published Posts
CYBERSECURITY
VENDORS
- Akamai
- A10 Networks
- Blackberry Cylance
- Cisco
- Cyberark
- Cloudfare
- Crowdstrike
- Checkpoint
- F5 Networks
- FyreEye
- Fortinet
- Guardicore
- IBM
- Kaspersky
- Mcafee - Trellix
- Mandiant
- Maltego
- Microsoft
- Netscope
- Palo Alto Networks
- RSA Security
- Redhat
- Splunk
- Symantec
- Tenable
- Trendmicro
CYBERSECURITY
MSSP
- Accenture
- Attos
- AT&T Cybersecurity
- BT Security
- BASE 4 - Hispam
- Deloitte
- Entelgy Security
- KPMG
- NTT Security
- Novared - Hispam
- Neosecure - Hispam
- Orange Cyberdefense
- PwC
- Telefonica Tech
- Thales
- Verizon Security