- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
LATEST NEWS
- 05 / 04 : 12:00 pm : The Real Risk is Not Knowing Your Real Risk: Perspectives from Asia Pacific Tour with EY – Source: securityboulevard.com
- 05 / 04 : 12:00 pm : Airsoft Data Breach Exposes Data of 75,000 Players – Source: securityboulevard.com
- 05 / 04 : 12:00 pm : Get SOAR Savvy Before RSAC 2024: 5 Reads to Level Up Your SOC – Source: securityboulevard.com
- 05 / 04 : 12:00 pm : Cloud Monitor Automation Thwarts Phishing & Malware Emails – Source: securityboulevard.com
- 05 / 04 : 12:00 pm : MY TAKE: Is Satya Nadella’s ‘Secure Future Initiative’ a deja vu of ‘Trustworthy Computing?’ – Source: securityboulevard.com
- 05 / 04 : 12:00 pm : Palo Alto Networks Extends SASE Reach to Unmanaged Devices – Source: securityboulevard.com
- 05 / 04 : 12:00 pm : USENIX Security ’23 – Cryptographic Deniability: A Multi-perspective Study of User Perceptions and Expectations – Source: securityboulevard.com
- 05 / 04 : 12:00 pm : The impact of automating open source dependency management – Source: securityboulevard.com
- 05 / 04 : 12:00 pm : Unlocking SMB Cybersecurity: The Rise of Virtual CISOs in 2024 and Beyond – Source: securityboulevard.com
- 05 / 04 : 12:00 pm : Vulnerability of the Month – Controversy of the JetBrains TeamCity CVE-2024-27198 & CVE-2024-27199 – Source: securityboulevard.com
- 05 / 04 : 8:00 am : Android bug can leak DNS traffic with VPN kill switch enabled – Source: www.bleepingcomputer.com
- 05 / 04 : 8:00 am : NSA warns of North Korean hackers exploiting weak DMARC email policies – Source: www.bleepingcomputer.com
- 05 / 04 : 8:00 am : Google rolls back reCaptcha update to fix Firefox issues – Source: www.bleepingcomputer.com
- 05 / 04 : 8:00 am : NATO and EU condemn Russia’s cyberattacks against Germany, Czechia – Source: www.bleepingcomputer.com
- 05 / 04 : 8:00 am : Microsoft rolls out passkey auth for personal Microsoft accounts – Source: www.bleepingcomputer.com
- 05 / 04 : 6:00 am : How Intel 471’s Buy of Cyborg Is Reshaping Threat Hunting – Source: www.databreachtoday.com
- 05 / 04 : 6:00 am : Code to Cloud Roadshow – Tysons Corner In-Person Event hosted by Palo Alto Networks – Source: www.databreachtoday.com
- 05 / 04 : 6:00 am : Regulating AI: ‘It’s Going to Be a Madhouse’ – Source: www.databreachtoday.com
- 05 / 04 : 6:00 am : Web Trackers Persist in Healthcare Despite Privacy Risks – Source: www.databreachtoday.com
- 05 / 04 : 6:00 am : New Report Exposes Iranian Hacking Group’s Media Masquerade – Source: www.databreachtoday.com
CISO STRATEGICS
CYBER ARCHITECTURE
SOC CSIRT OPERATIONS
CYBERSECURITY TOOLS
CYBERSECURITY VENDORS
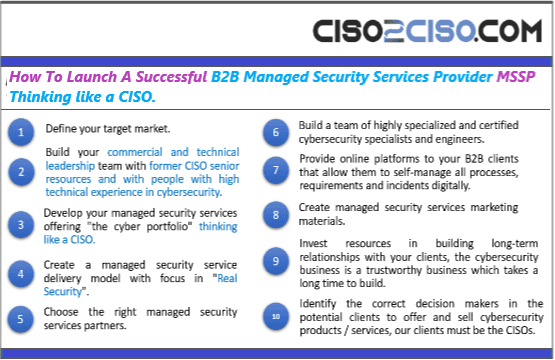
CYBERSECURITY MSSP
CYBER ORGANIZATIONS
CYBER REGULATIONS
EVENTS & CONFERENCES
VULNs & ZERO DAYS
LATEST CYBER NEWS

CISO2CISO Editors' Picks
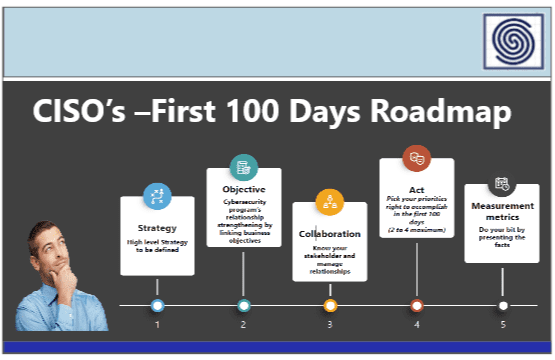
CISO
STRATEGICS
- CISO Strategics
- CISO Learn & Leadership
- Cybersecurity for C-Levels
- Cybersecurity Trends & Insights
- Cyberseurity Awareness
- Cybercrimen Ecosystem
- Cybersecurity Measure & Metrics
- Cybersecurity Frameworks
- Cybersecurity Policy & Standars
- Fraud
- Information Security
- Osint - Humint
- Privacy
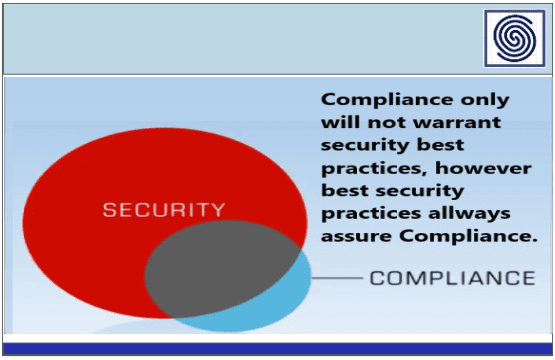
- Risk & Compliance
- Resilience
- Social Engineering
- Supply Chain Security
CYBER
ARCHITECTURE
- API Security
- Application Security
- Blockchain Security
- Cloud Security
- Data Security
- Defense in Depth
- DevSecOps
- Endpoint Security
- IA Security
- IOT Security
- MAC-OS Security
- Metaverse Security
- Micro segmentation
- Mitre Att&ck
- Mobile & 5G Security
- Network Security
- OT Security
- OWASP Security
- Perimeter Security
- SAP Security
- Telco & Carrier Security
- Zero Trust Security
SOC CSIRT
OPERATIONS
- Cyber Incidents & Attacks Notepad
- CSIRT Operations
- Data Leak & Breach Incidents Notepad
- DDOS Attacks
- DFIR - Forensics & Incident Response
- Dark & Deep Web
- SOC Operations
- SIEM Use Cases & Playbooks
- SOAR Authomation & Playbooks
- Malware & Ransomware
- Red - Blue & Purple Teams Operations
- Threat Intelligence
- Threat Hunting
- Vulnerabilities

CYBER
ORGs
- CCN-EU
- CSA
- CIS
- CISA
- DHS-US
- ENISA
- ISACA
- INCIBE-EU
- Mitre Att&ack
- NSA
- NIST Security
- SANS
- WEF
CYBER
CONFERENCES
Latest Published Posts
CYBERSECURITY
VENDORS
- Akamai
- A10 Networks
- Blackberry Cylance
- Cisco
- Cyberark
- Cloudfare
- Crowdstrike
- Checkpoint
- F5 Networks
- FyreEye
- Fortinet
- Guardicore
- IBM
- Kaspersky
- Mcafee - Trellix
- Mandiant
- Maltego
- Microsoft
- Netscope
- Palo Alto Networks
- RSA Security
- Redhat
- Splunk
- Symantec
- Tenable
- Trendmicro
CYBERSECURITY
MSSP
- Accenture
- Attos
- AT&T Cybersecurity
- BT Security
- BASE 4 - Hispam
- Deloitte
- Entelgy Security
- KPMG
- NTT Security
- Novared - Hispam
- Neosecure - Hispam
- Orange Cyberdefense
- PwC
- Telefonica Tech
- Thales
- Verizon Security