- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
LATEST NEWS
- 05 / 03 : 12:00 am : 7 tips for preventing pernicious password-based breaches – Source: www.cybertalk.org
- 05 / 03 : 12:00 am : AI, CVEs and Swiss cheese – Source: www.cybertalk.org
- 05 / 03 : 12:00 am : RSAC Fireside Chat: How the open-source community hustled to identify LLM vulnerabilities – Source: www.lastwatchdog.com
- 05 / 03 : 12:00 am : RSAC Fireside Chat: APIs are wondrous connectors — and the wellspring of multiplying exposures – Source: www.lastwatchdog.com
- 05 / 02 : 7:02 pm : 4 IoT Trends U.K. Businesses Should Watch in 2024 – Source: www.techrepublic.com
- 05 / 02 : 7:02 pm : 5 Best Password Managers Built for Teams in 2024 (Free & Paid) – Source: www.techrepublic.com
- 05 / 02 : 7:01 pm : Florida man gets 6 years behind bars for flogging fake Cisco kit to US military – Source: go.theregister.com
- 05 / 02 : 7:01 pm : Patch up – 4 critical bugs in ArubaOS lead to remote code execution – Source: go.theregister.com
- 05 / 02 : 7:01 pm : Federal frenzy to patch gaping GitLab account takeover hole – Source: go.theregister.com
- 05 / 02 : 7:01 pm : Think tank: China’s tech giants refine and define Beijing’s propaganda push – Source: go.theregister.com
- 05 / 02 : 7:01 pm : REvil ransomware scum sentenced to almost 14 years inside, ordered to pay $16 million – Source: go.theregister.com
- 05 / 02 : 7:01 pm : A million Australian pubgoers wake up to find personal info listed on leak site – Source: go.theregister.com
- 05 / 02 : 7:01 pm : Dropbox dropped the ball on security, haemorrhaging customer and third-party info – Source: go.theregister.com
- 05 / 02 : 7:01 pm : Block accused of mass compliance failures that saw digi-dollars reach terrorists – Source: go.theregister.com
- 05 / 02 : 7:01 pm : Microsoft cannot keep its own security in order, so what hope for its add-ons customers? – Source: go.theregister.com
- 05 / 02 : 7:01 pm : Management company settles for $18.4M after nuclear weapons plant staff fudged their timesheets – Source: go.theregister.com
- 05 / 02 : 7:01 pm : Android Flaw Affected Apps With 4 Billion Installs – Source: www.infosecurity-magazine.com
- 05 / 02 : 7:01 pm : Hackers Target New NATO Member Sweden with Surge of DDoS Attacks – Source: www.infosecurity-magazine.com
- 05 / 02 : 7:01 pm : Three-Quarters of CISOs Admit App Security Incidents – Source: www.infosecurity-magazine.com
- 05 / 02 : 7:01 pm : Security Breach Exposes Dropbox Sign Users – Source: www.infosecurity-magazine.com
CISO STRATEGICS
CYBER ARCHITECTURE
SOC CSIRT OPERATIONS
CYBERSECURITY TOOLS
CYBERSECURITY VENDORS
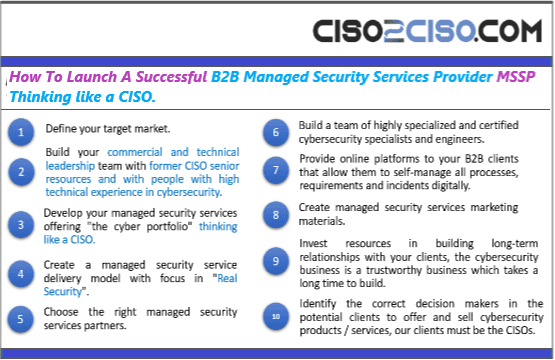
CYBERSECURITY MSSP
CYBER ORGANIZATIONS
CYBER REGULATIONS
EVENTS & CONFERENCES
VULNs & ZERO DAYS
LATEST CYBER NEWS

CISO2CISO Editors' Picks
CISO
STRATEGICS
- CISO Strategics
- CISO Learn & Leadership
- Cybersecurity for C-Levels
- Cybersecurity Trends & Insights
- Cyberseurity Awareness
- Cybercrimen Ecosystem
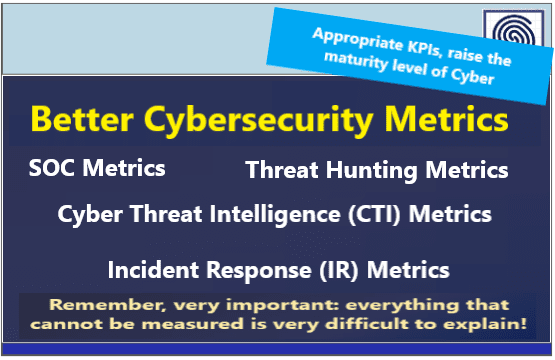
- Cybersecurity Measure & Metrics
- Cybersecurity Frameworks
- Cybersecurity Policy & Standars
- Fraud
- Information Security
- Osint - Humint
- Privacy
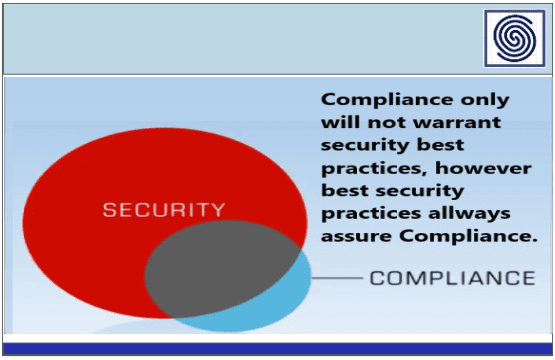
- Risk & Compliance
- Resilience
- Social Engineering
- Supply Chain Security
CYBER
ARCHITECTURE
- API Security
- Application Security
- Blockchain Security
- Cloud Security
- Data Security
- Defense in Depth
- DevSecOps
- Endpoint Security
- IA Security
- IOT Security
- MAC-OS Security
- Metaverse Security
- Micro segmentation
- Mitre Att&ck
- Mobile & 5G Security
- Network Security
- OT Security
- OWASP Security
- Perimeter Security
- SAP Security
- Telco & Carrier Security
- Zero Trust Security
SOC CSIRT
OPERATIONS
- Cyber Incidents & Attacks Notepad
- CSIRT Operations
- Data Leak & Breach Incidents Notepad
- DDOS Attacks
- DFIR - Forensics & Incident Response
- Dark & Deep Web
- SOC Operations
- SIEM Use Cases & Playbooks
- SOAR Authomation & Playbooks
- Malware & Ransomware
- Red - Blue & Purple Teams Operations
- Threat Intelligence
- Threat Hunting
- Vulnerabilities

CYBER
ORGs
- CCN-EU
- CSA
- CIS
- CISA
- DHS-US
- ENISA
- ISACA
- INCIBE-EU
- Mitre Att&ack
- NSA
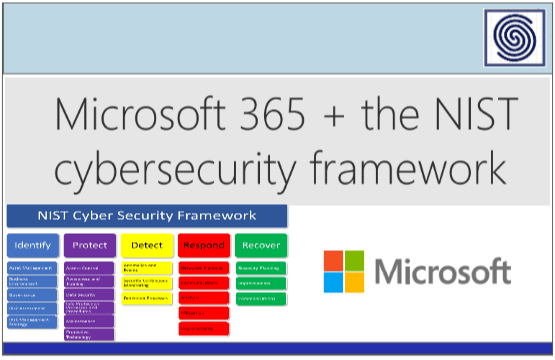
- NIST Security
- SANS
- WEF
CYBER
CONFERENCES
Latest Published Posts
CYBERSECURITY
VENDORS
- Akamai
- A10 Networks
- Blackberry Cylance
- Cisco
- Cyberark
- Cloudfare
- Crowdstrike
- Checkpoint
- F5 Networks
- FyreEye
- Fortinet
- Guardicore
- IBM
- Kaspersky
- Mcafee - Trellix
- Mandiant
- Maltego
- Microsoft
- Netscope
- Palo Alto Networks
- RSA Security
- Redhat
- Splunk
- Symantec
- Tenable
- Trendmicro
CYBERSECURITY
MSSP
- Accenture
- Attos
- AT&T Cybersecurity
- BT Security
- BASE 4 - Hispam
- Deloitte
- Entelgy Security
- KPMG
- NTT Security
- Novared - Hispam
- Neosecure - Hispam
- Orange Cyberdefense
- PwC
- Telefonica Tech
- Thales
- Verizon Security