- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
LATEST NEWS
- 05 / 09 : 4:00 pm : New TunnelVision Attack Allows Hijacking of VPN Traffic via DHCP Manipulation – Source:thehackernews.com
- 05 / 09 : 4:00 pm : Kremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign – Source:thehackernews.com
- 05 / 09 : 4:00 pm : New Guide: How to Scale Your vCISO Services Profitably – Source:thehackernews.com
- 05 / 09 : 4:00 pm : Mirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery – Source:thehackernews.com
- 05 / 09 : 12:01 pm : Cancer patients’ sensitive information accessed by “unidentified parties” after being left exposed by screening lab for years – Source: www.bitdefender.com
- 05 / 09 : 12:01 pm : Smashing Security podcast #371: Unmasking LockBitsupp, company extortion, and a Tinder fraudster – Source: grahamcluley.com
- 05 / 09 : 12:00 pm : Silverfort Announces New Integration with Microsoft Entra ID EAM – Source: securityboulevard.com
- 05 / 09 : 12:00 pm : Crypto Mixer Money Laundering: Samourai Founders Arrested – Source: securityboulevard.com
- 05 / 09 : 12:00 pm : AI Regulation in Finance: Steering the Future with Consumer Protection at the Helm – Source: securityboulevard.com
- 05 / 09 : 12:00 pm : How Nudge Security is useful in a merger or acquisition – Source: securityboulevard.com
- 05 / 09 : 12:00 pm : Build Strong Information Security Policy: Template & Examples – Source: securityboulevard.com
- 05 / 09 : 12:00 pm : Ransomware Attacks are Up, but Profits are Down: Chainalysis – Source: securityboulevard.com
- 05 / 09 : 12:00 pm : USENIX Security ’23 – “Security Is Not My Field, I’m A Stats Guy”: A Qualitative Root Cause Analysis of Barriers to Adversarial Machine Learning Defenses in Industry – Source: securityboulevard.com
- 05 / 09 : 12:00 pm : RSAC 2024 Day 2: IoT Security Questions (and Answers) – Source: securityboulevard.com
- 05 / 09 : 12:00 pm : Harnessing Cyber Risk Quantification to Safeguard Healthcare Providers – Source: securityboulevard.com
- 05 / 09 : 12:00 pm : 10 Ways K12 School Districts Can Boost Cybersecurity for the 2024-2025 School Year – Source: securityboulevard.com
- 05 / 09 : 11:00 am : Quishing Campaign Exploits Microsoft Open Redirect Vulnerability – Source: www.cyberdefensemagazine.com
- 05 / 09 : 11:00 am : Overcoming Common Data Security Challenges – Source: www.cyberdefensemagazine.com
- 05 / 09 : 11:00 am : Detect and Destroy Cyber Threats with Red Piranha – Source: www.cyberdefensemagazine.com
- 05 / 09 : 11:00 am : Revolutionizing Cybersecurity Recruitment and Networking: The Cyberr.ai Approach – Source: www.cyberdefensemagazine.com
CISO STRATEGICS
CYBER ARCHITECTURE
SOC CSIRT OPERATIONS
CYBERSECURITY TOOLS
CYBERSECURITY VENDORS
CYBERSECURITY MSSP
CYBER ORGANIZATIONS
CYBER REGULATIONS
EVENTS & CONFERENCES
VULNs & ZERO DAYS
LATEST CYBER NEWS

CISO2CISO Editors' Picks
CISO
STRATEGICS
- CISO Strategics
- CISO Learn & Leadership
- Cybersecurity for C-Levels
- Cybersecurity Trends & Insights
- Cyberseurity Awareness
- Cybercrimen Ecosystem
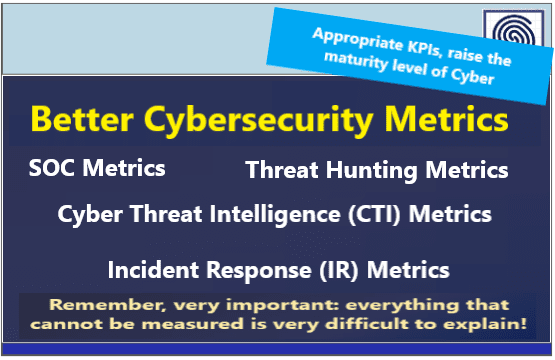
- Cybersecurity Measure & Metrics
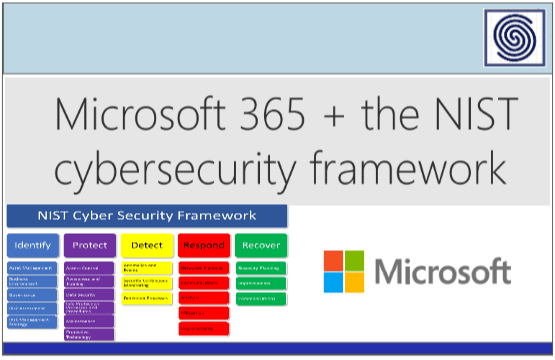
- Cybersecurity Frameworks
- Cybersecurity Policy & Standars
- Fraud
- Information Security
- Osint - Humint
- Privacy
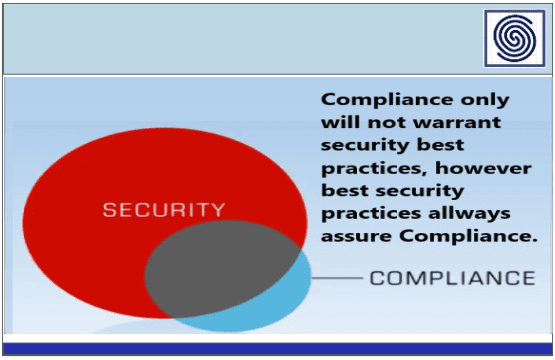
- Risk & Compliance
- Resilience
- Social Engineering
- Supply Chain Security
CYBER
ARCHITECTURE
- API Security
- Application Security
- Blockchain Security
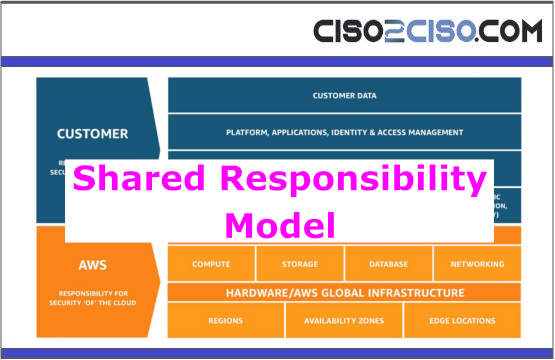
- Cloud Security
- Data Security
- Defense in Depth
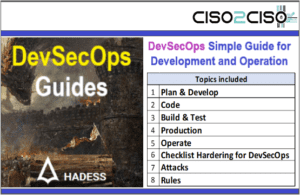
- DevSecOps
- Endpoint Security
- IA Security
- IOT Security
- MAC-OS Security
- Metaverse Security
- Micro segmentation
- Mitre Att&ck
- Mobile & 5G Security
- Network Security
- OT Security
- OWASP Security
- Perimeter Security
- SAP Security
- Telco & Carrier Security
- Zero Trust Security
SOC CSIRT
OPERATIONS
- Cyber Incidents & Attacks Notepad
- CSIRT Operations
- Data Leak & Breach Incidents Notepad
- DDOS Attacks
- DFIR - Forensics & Incident Response
- Dark & Deep Web
- SOC Operations
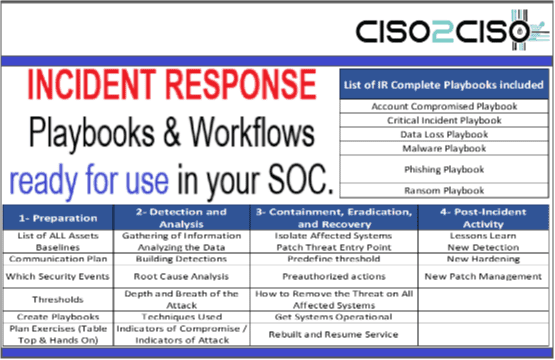
- SIEM Use Cases & Playbooks
- SOAR Authomation & Playbooks
- Malware & Ransomware
- Red - Blue & Purple Teams Operations
- Threat Intelligence
- Threat Hunting
- Vulnerabilities

CYBER
ORGs
- CCN-EU
- CSA
- CIS
- CISA
- DHS-US
- ENISA
- ISACA
- INCIBE-EU
- Mitre Att&ack
- NSA
- NIST Security
- SANS
- WEF
CYBER
CONFERENCES
Latest Published Posts
CYBERSECURITY
VENDORS
- Akamai
- A10 Networks
- Blackberry Cylance
- Cisco
- Cyberark
- Cloudfare
- Crowdstrike
- Checkpoint
- F5 Networks
- FyreEye
- Fortinet
- Guardicore
- IBM
- Kaspersky
- Mcafee - Trellix
- Mandiant
- Maltego
- Microsoft
- Netscope
- Palo Alto Networks
- RSA Security
- Redhat
- Splunk
- Symantec
- Tenable
- Trendmicro
CYBERSECURITY
MSSP
- Accenture
- Attos
- AT&T Cybersecurity
- BT Security
- BASE 4 - Hispam
- Deloitte
- Entelgy Security
- KPMG
- NTT Security
- Novared - Hispam
- Neosecure - Hispam
- Orange Cyberdefense
- PwC
- Telefonica Tech
- Thales
- Verizon Security