- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
LATEST NEWS
- 05 / 09 : 5:00 am : Heimdal Welcomes Jesper Frederiksen as Its New Chief Executive Officer – Source: heimdalsecurity.com
- 05 / 09 : 5:00 am : 20+ Xiaomi Vulnerabilities Put Users’ Data and Devices at Risk – Source: heimdalsecurity.com
- 05 / 09 : 4:00 am : Zscaler takes “test environment” offline after rumors of a breach – Source: www.bleepingcomputer.com
- 05 / 09 : 4:00 am : University System of Georgia: 800K exposed in 2023 MOVEit attack – Source: www.bleepingcomputer.com
- 05 / 09 : 4:00 am : Ascension healthcare takes systems offline after cyberattack – Source: www.bleepingcomputer.com
- 05 / 09 : 4:00 am : Stack Overflow suspends user for editing posts in OpenAI protest – Source: www.bleepingcomputer.com
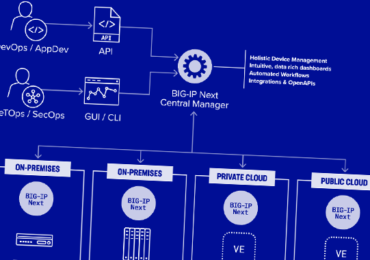
- 05 / 09 : 4:00 am : New BIG-IP Next Central Manager bugs allow device takeover – Source: www.bleepingcomputer.com
- 05 / 09 : 4:00 am : FBI warns of gift card fraud ring targeting retail companies – Source: www.bleepingcomputer.com
- 05 / 09 : 4:00 am : City of Wichita breach claimed by LockBit ransomware gang – Source: www.bleepingcomputer.com
- 05 / 09 : 4:00 am : Microsoft: April Windows Server updates also cause crashes, reboots – Source: www.bleepingcomputer.com
- 05 / 09 : 4:00 am : Massive webshop fraud ring steals credit cards from 850,000 people – Source: www.bleepingcomputer.com
- 05 / 09 : 4:00 am : Critical F5 Central Manager Vulnerabilities Allow Enable Full Device Takeover – Source:thehackernews.com
- 05 / 09 : 1:00 am : LockBit gang claimed responsibility for the attack on City of Wichita – Source: securityaffairs.com
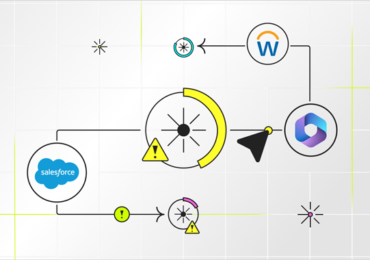
- 05 / 09 : 1:00 am : New TunnelVision technique can bypass the VPN encapsulation – Source: securityaffairs.com
- 05 / 09 : 1:00 am : LiteSpeed Cache WordPress plugin actively exploited in the wild – Source: securityaffairs.com
- 05 / 09 : 1:00 am : Most Tinyproxy Instances are potentially vulnerable to flaw CVE-2023-49606 – Source: securityaffairs.com
- 05 / 09 : 1:00 am : UK Ministry of Defense disclosed a third-party data breach exposing military personnel data – Source: securityaffairs.com
- 05 / 09 : 12:00 am : RSAC: Three Strategies to Boost Open-Source Security – Source: www.infosecurity-magazine.com
- 05 / 09 : 12:00 am : RSAC: CISA Launches Vulnrichment Program to Address NVD Challenges – Source: www.infosecurity-magazine.com
- 05 / 09 : 12:00 am : RSAC: Researchers Share Lessons from the World’s First AI Security Incident Response Team – Source: www.infosecurity-magazine.com
CISO STRATEGICS
CYBER ARCHITECTURE
SOC CSIRT OPERATIONS
CYBERSECURITY TOOLS
CYBERSECURITY VENDORS
CYBERSECURITY MSSP
CYBER ORGANIZATIONS
CYBER REGULATIONS
EVENTS & CONFERENCES
VULNs & ZERO DAYS
LATEST CYBER NEWS

CISO2CISO Editors' Picks
CISO
STRATEGICS
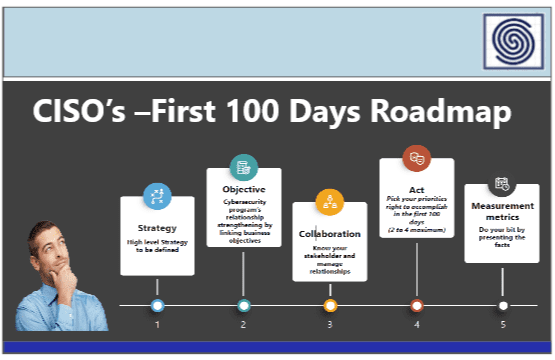
- CISO Strategics
- CISO Learn & Leadership
- Cybersecurity for C-Levels
- Cybersecurity Trends & Insights
- Cyberseurity Awareness
- Cybercrimen Ecosystem
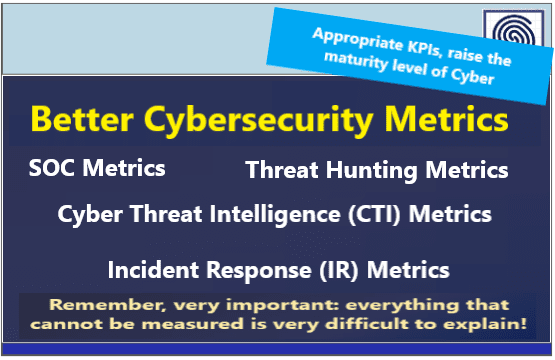
- Cybersecurity Measure & Metrics
- Cybersecurity Frameworks
- Cybersecurity Policy & Standars
- Fraud
- Information Security
- Osint - Humint
- Privacy
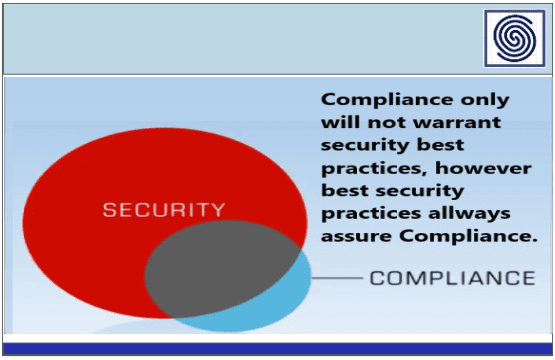
- Risk & Compliance
- Resilience
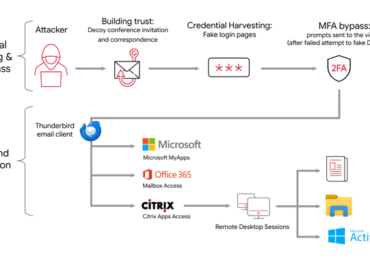
- Social Engineering
- Supply Chain Security
CYBER
ARCHITECTURE
- API Security
- Application Security
- Blockchain Security
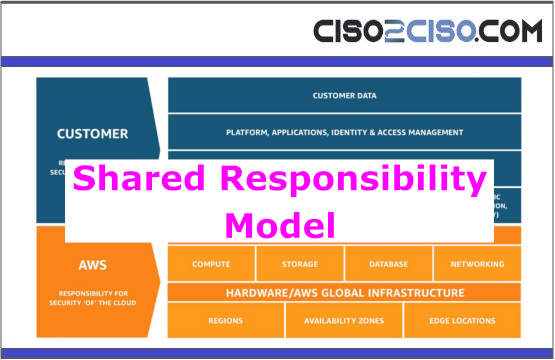
- Cloud Security
- Data Security
- Defense in Depth
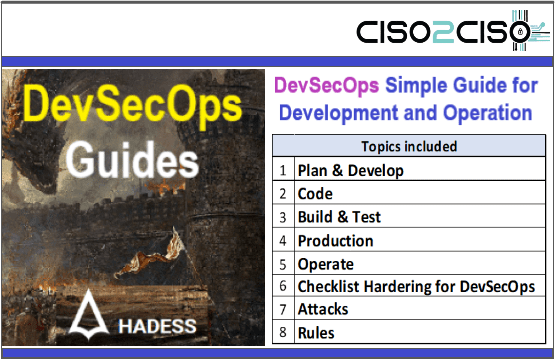
- DevSecOps
- Endpoint Security
- IA Security
- IOT Security
- MAC-OS Security
- Metaverse Security
- Micro segmentation
- Mitre Att&ck
- Mobile & 5G Security
- Network Security
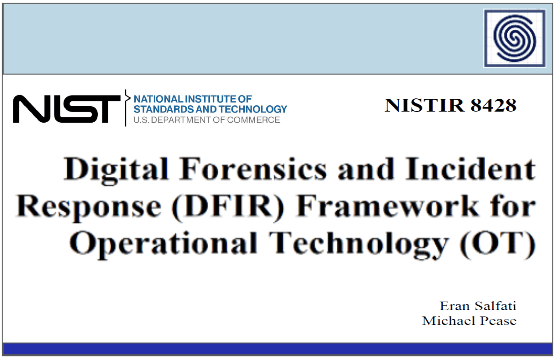
- OT Security
- OWASP Security
- Perimeter Security
- SAP Security
- Telco & Carrier Security
- Zero Trust Security
SOC CSIRT
OPERATIONS
- Cyber Incidents & Attacks Notepad
- CSIRT Operations
- Data Leak & Breach Incidents Notepad
- DDOS Attacks
- DFIR - Forensics & Incident Response
- Dark & Deep Web
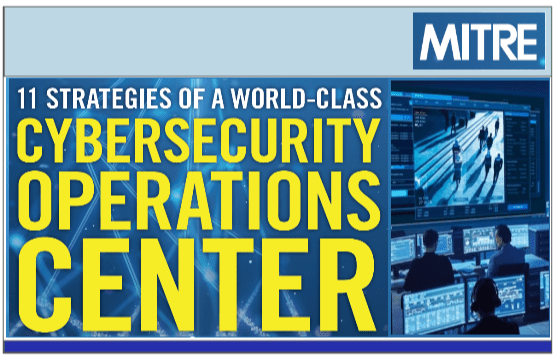
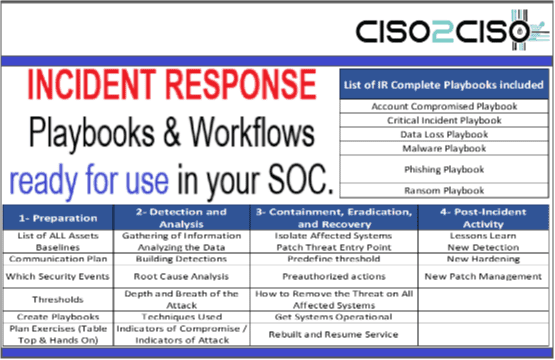
- SOC Operations
- SIEM Use Cases & Playbooks
- SOAR Authomation & Playbooks
- Malware & Ransomware
- Red - Blue & Purple Teams Operations
- Threat Intelligence
- Threat Hunting
- Vulnerabilities

CYBER
ORGs
- CCN-EU
- CSA
- CIS
- CISA
- DHS-US
- ENISA
- ISACA
- INCIBE-EU
- Mitre Att&ack
- NSA
- NIST Security
- SANS
- WEF
CYBER
CONFERENCES
Latest Published Posts
CYBERSECURITY
VENDORS
- Akamai
- A10 Networks
- Blackberry Cylance
- Cisco
- Cyberark
- Cloudfare
- Crowdstrike
- Checkpoint
- F5 Networks
- FyreEye
- Fortinet
- Guardicore
- IBM
- Kaspersky
- Mcafee - Trellix
- Mandiant
- Maltego
- Microsoft
- Netscope
- Palo Alto Networks
- RSA Security
- Redhat
- Splunk
- Symantec
- Tenable
- Trendmicro
CYBERSECURITY
MSSP
- Accenture
- Attos
- AT&T Cybersecurity
- BT Security
- BASE 4 - Hispam
- Deloitte
- Entelgy Security
- KPMG
- NTT Security
- Novared - Hispam
- Neosecure - Hispam
- Orange Cyberdefense
- PwC
- Telefonica Tech
- Thales
- Verizon Security