- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
LATEST NEWS
- 05 / 06 : 6:00 am : Amnesty International Cites Indonesia as a Spyware Hub – Source: www.darkreading.com
- 05 / 05 : 11:00 pm : Celebrating our 12th Anniversary at RSA conference 2024 – Source: www.cyberdefensemagazine.com
- 05 / 05 : 11:00 pm : Offensive Awakening: The 2024 Shift from Defensive to Proactive Security – Source: www.cyberdefensemagazine.com
- 05 / 05 : 11:00 pm : Navigating the Digital Age: AI’s Crucial Role in Cybersecurity Reinforcement – Source: www.cyberdefensemagazine.com
- 05 / 05 : 10:01 pm : Finland warns of Android malware attacks breaching bank accounts – Source: www.bleepingcomputer.com
- 05 / 05 : 10:00 pm : Ransomware drama: Law enforcement seized Lockbit group’s website again – Source: securityaffairs.com
- 05 / 05 : 10:00 pm : NATO and the EU formally condemned Russia-linked APT28 cyber espionage – Source: securityaffairs.com
- 05 / 05 : 10:00 pm : Security Affairs newsletter Round 470 by Pierluigi Paganini – INTERNATIONAL EDITION – Source: securityaffairs.com
- 05 / 05 : 2:00 pm : End-to-end encryption may be the bane of cops, but they can’t close that Pandora’s Box – Source: go.theregister.com
- 05 / 05 : 12:00 pm : GenAI Continues to Dominate CIO and CISO Conversations – Source: securityboulevard.com
- 05 / 05 : 12:00 pm : RSAC 2024 Innovation Sandbox | Reality Defender: Deepfake Detection Platform – Source: securityboulevard.com
- 05 / 05 : 12:00 pm : USENIX Security ’23 – Silent Bugs Matter: A Study of Compiler-Introduced Security Bugs – Source: securityboulevard.com
- 05 / 05 : 12:00 pm : RSAC 2024 Innovation Sandbox | Dropzone AI: Automated Investigation and Security Operations – Source: securityboulevard.com
- 05 / 05 : 12:00 pm : DD2345 Military Critical Technical Data Agreement and CMMC – Source: securityboulevard.com
- 05 / 05 : 3:00 am : Iranian hackers pose as journalists to push backdoor malware – Source: www.bleepingcomputer.com
- 05 / 05 : 3:00 am : Android bug leaks DNS queries even when VPN kill switch is enabled – Source: www.bleepingcomputer.com
- 05 / 05 : 2:00 am : Navigating the API Security Landscape: A CEO’s Perspective on Embedding Zero Trust Principles – Source: www.cyberdefensemagazine.com
- 05 / 04 : 9:00 pm : Blackbasta gang claimed responsibility for Synlab Italia attack – Source: securityaffairs.com
- 05 / 04 : 7:00 pm : Friday Squid Blogging: Squid Purses – Source: www.schneier.com
- 05 / 04 : 6:00 pm : Mimic Launches With New Ransomware Defense Platform – Source: www.darkreading.com
CISO STRATEGICS
CYBER ARCHITECTURE
SOC CSIRT OPERATIONS
CYBERSECURITY TOOLS
CYBERSECURITY VENDORS
CYBERSECURITY MSSP
CYBER ORGANIZATIONS
CYBER REGULATIONS
EVENTS & CONFERENCES
VULNs & ZERO DAYS
LATEST CYBER NEWS

CISO2CISO Editors' Picks
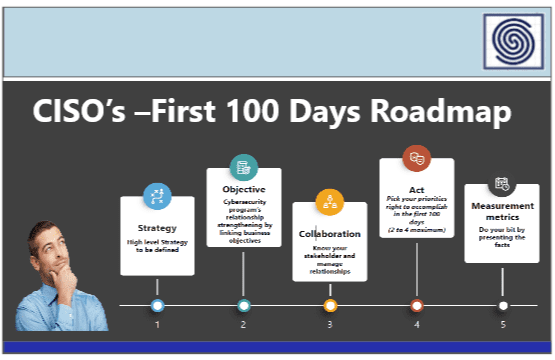
CISO
STRATEGICS
- CISO Strategics
- CISO Learn & Leadership
- Cybersecurity for C-Levels
- Cybersecurity Trends & Insights
- Cyberseurity Awareness
- Cybercrimen Ecosystem
- Cybersecurity Measure & Metrics
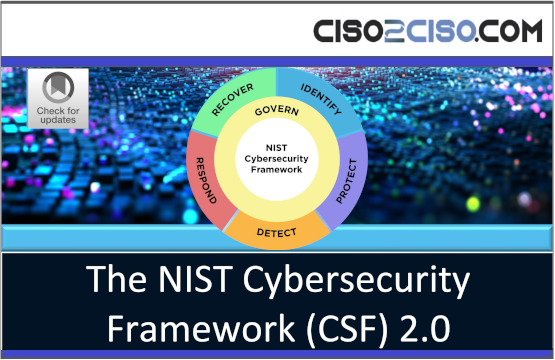
- Cybersecurity Frameworks
- Cybersecurity Policy & Standars
- Fraud
- Information Security
- Osint - Humint
- Privacy
- Risk & Compliance
- Resilience
- Social Engineering
- Supply Chain Security
CYBER
ARCHITECTURE
- API Security
- Application Security
- Blockchain Security
- Cloud Security
- Data Security
- Defense in Depth
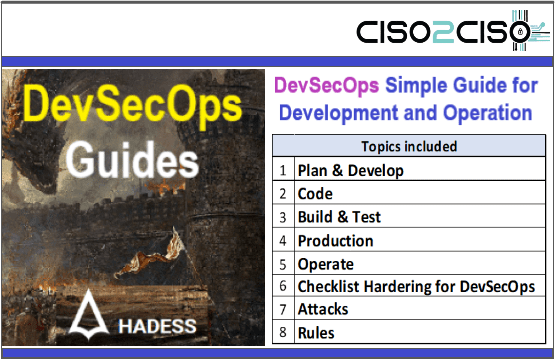
- DevSecOps
- Endpoint Security
- IA Security
- IOT Security
- MAC-OS Security
- Metaverse Security
- Micro segmentation
- Mitre Att&ck
- Mobile & 5G Security
- Network Security
- OT Security
- OWASP Security
- Perimeter Security
- SAP Security
- Telco & Carrier Security
- Zero Trust Security
SOC CSIRT
OPERATIONS
- Cyber Incidents & Attacks Notepad
- CSIRT Operations
- Data Leak & Breach Incidents Notepad
- DDOS Attacks
- DFIR - Forensics & Incident Response
- Dark & Deep Web
- SOC Operations
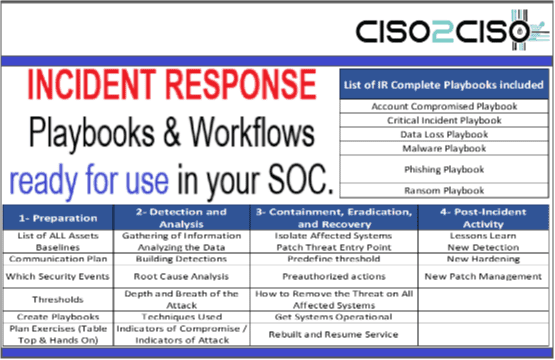
- SIEM Use Cases & Playbooks
- SOAR Authomation & Playbooks
- Malware & Ransomware
- Red - Blue & Purple Teams Operations
- Threat Intelligence
- Threat Hunting
- Vulnerabilities

CYBER
ORGs
- CCN-EU
- CSA
- CIS
- CISA
- DHS-US
- ENISA
- ISACA
- INCIBE-EU
- Mitre Att&ack
- NSA
- NIST Security
- SANS
- WEF
CYBER
CONFERENCES
Latest Published Posts
CYBERSECURITY
VENDORS
- Akamai
- A10 Networks
- Blackberry Cylance
- Cisco
- Cyberark
- Cloudfare
- Crowdstrike
- Checkpoint
- F5 Networks
- FyreEye
- Fortinet
- Guardicore
- IBM
- Kaspersky
- Mcafee - Trellix
- Mandiant
- Maltego
- Microsoft
- Netscope
- Palo Alto Networks
- RSA Security
- Redhat
- Splunk
- Symantec
- Tenable
- Trendmicro
CYBERSECURITY
MSSP
- Accenture
- Attos
- AT&T Cybersecurity
- BT Security
- BASE 4 - Hispam
- Deloitte
- Entelgy Security
- KPMG
- NTT Security
- Novared - Hispam
- Neosecure - Hispam
- Orange Cyberdefense
- PwC
- Telefonica Tech
- Thales
- Verizon Security