- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
LATEST NEWS
- 04 / 29 : 10:00 am : Voter Registration System Taken Offline in Coffee County Cyber-Incident – Source: www.infosecurity-magazine.com
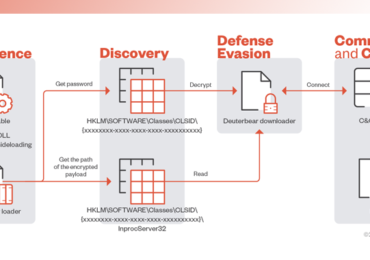
- 04 / 29 : 6:00 am : ToddyCat is making holes in your infrastructure – Source: securelist.com
- 04 / 28 : 10:00 am : Assessing the Y, and How, of the XZ Utils incident – Source: securelist.com
- 04 / 27 : 11:00 pm : Japanese police create fake support scam payment cards to warn victims – Source: www.bleepingcomputer.com
- 04 / 27 : 7:00 pm : Zero Trust strategies for navigating IoT/OT security challenges – Source: www.cybertalk.org
- 04 / 27 : 7:00 pm : GUEST ESSAY: Here’s why securing smart cities’ critical infrastructure has become a top priority – Source: www.lastwatchdog.com
- 04 / 27 : 11:50 am : Breaking Down Cybersecurity: The Real Meaning Behind the Jargon – Source: securityboulevard.com
- 04 / 26 : 3:00 am : North Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures – Source:thehackernews.com
- 04 / 26 : 3:00 am : Network Threats: A Step-by-Step Attack Demonstration – Source:thehackernews.com
- 04 / 26 : 3:00 am : DOJ Arrests Founders of Crypto Mixer Samourai for $2 Billion in Illegal Transactions – Source:thehackernews.com
- 04 / 26 : 3:00 am : Google Postpones Third-Party Cookie Deprecation Amid U.K. Regulatory Scrutiny – Source:thehackernews.com
- 04 / 26 : 3:00 am : State-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage – Source:thehackernews.com
- 04 / 26 : 3:00 am : U.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks – Source:thehackernews.com
- 04 / 26 : 3:00 am : Researchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike – Source:thehackernews.com
- 04 / 25 : 10:00 pm : Russian FSB Counterintelligence Chief Gets 9 Years in Cybercrime Bribery Scheme – Source: krebsonsecurity.com
- 04 / 20 : 6:00 am : Baby ASO: A Minimal Viable Transformation for Your SOC – Source: securityboulevard.com
- 04 / 20 : 6:00 am : LabHost Phishing Platform is Latest Target of International Law Agencies – Source: securityboulevard.com
- 04 / 20 : 6:00 am : Choosing SOC Tools? Read This First [2024 Guide] – Source: securityboulevard.com
- 04 / 20 : 6:00 am : USENIX Security ’23 – GAP: Differentially Private Graph Neural Networks with Aggregation Perturbation – Source: securityboulevard.com
- 04 / 20 : 6:00 am : SafeBreach Coverage for AA24-109A (Akira Ransomware) – Source: securityboulevard.com
CISO STRATEGICS
CYBER ARCHITECTURE
SOC CSIRT OPERATIONS
CYBERSECURITY TOOLS
CYBERSECURITY VENDORS
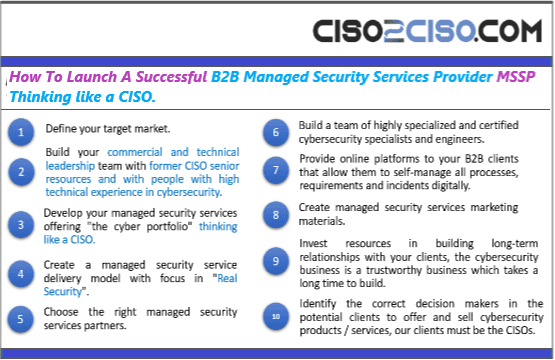
CYBERSECURITY MSSP
CYBER ORGANIZATIONS
CYBER REGULATIONS
EVENTS & CONFERENCES
VULNs & ZERO DAYS
LATEST CYBER NEWS

CISO2CISO Editors' Picks
CISO
STRATEGICS
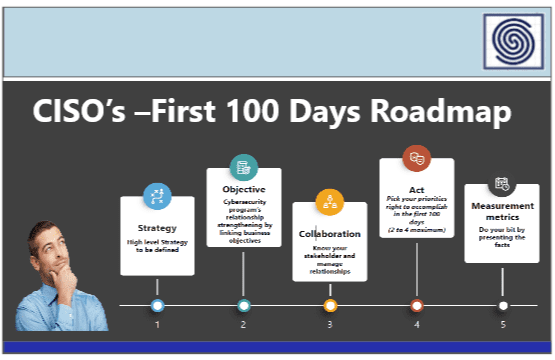
- CISO Strategics
- CISO Learn & Leadership
- Cybersecurity for C-Levels
- Cybersecurity Trends & Insights
- Cyberseurity Awareness
- Cybercrimen Ecosystem
- Cybersecurity Measure & Metrics
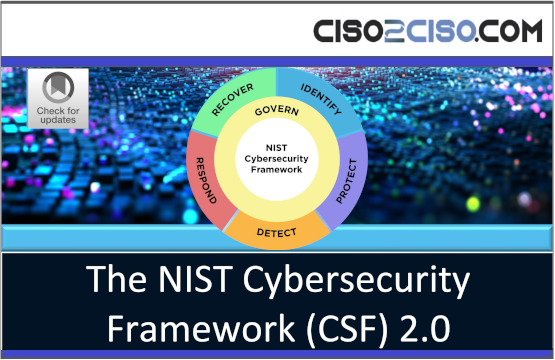
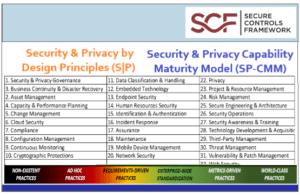
- Cybersecurity Frameworks
- Cybersecurity Policy & Standars
- Fraud
- Information Security
- Osint - Humint
- Privacy
- Risk & Compliance
- Resilience
- Social Engineering
- Supply Chain Security
CYBER
ARCHITECTURE
- API Security
- Application Security
- Blockchain Security
- Cloud Security
- Data Security
- Defense in Depth
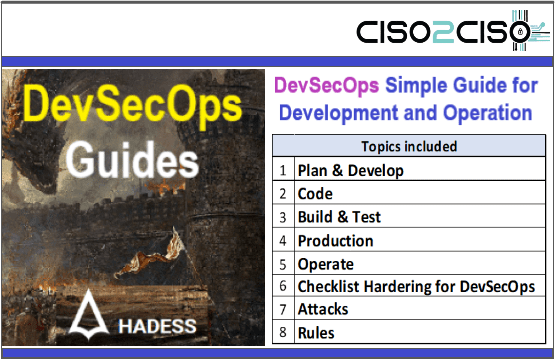
- DevSecOps
- Endpoint Security
- IA Security
- IOT Security
- MAC-OS Security
- Metaverse Security
- Micro segmentation
- Mitre Att&ck
- Mobile & 5G Security
- Network Security
- OT Security
- OWASP Security
- Perimeter Security
- SAP Security
- Telco & Carrier Security
- Zero Trust Security
SOC CSIRT
OPERATIONS
- Cyber Incidents & Attacks Notepad
- CSIRT Operations
- Data Leak & Breach Incidents Notepad
- DDOS Attacks
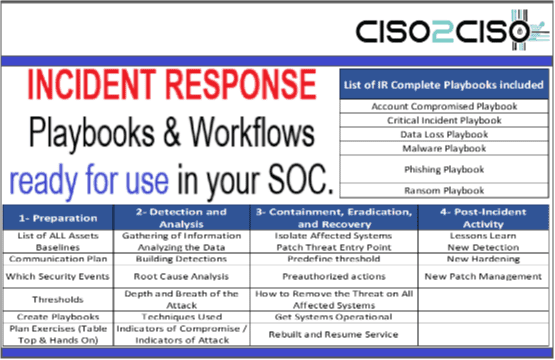
- DFIR - Forensics & Incident Response
- Dark & Deep Web
- SOC Operations
- SIEM Use Cases & Playbooks
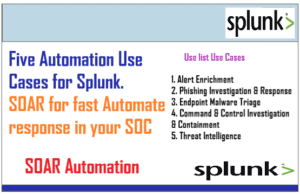
- SOAR Authomation & Playbooks
- Malware & Ransomware
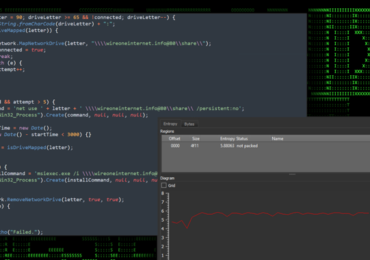
- Red - Blue & Purple Teams Operations
- Threat Intelligence
- Threat Hunting
- Vulnerabilities

CYBER
ORGs
- CCN-EU
- CSA
- CIS
- CISA
- DHS-US
- ENISA
- ISACA
- INCIBE-EU
- Mitre Att&ack
- NSA
- NIST Security
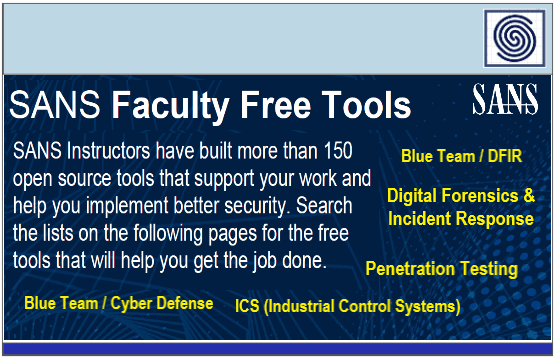
- SANS
- WEF
CYBER
CONFERENCES
Latest Published Posts
CYBERSECURITY
VENDORS
- Akamai
- A10 Networks
- Blackberry Cylance
- Cisco
- Cyberark
- Cloudfare
- Crowdstrike
- Checkpoint
- F5 Networks
- FyreEye
- Fortinet
- Guardicore
- IBM
- Kaspersky
- Mcafee - Trellix
- Mandiant
- Maltego
- Microsoft
- Netscope
- Palo Alto Networks
- RSA Security
- Redhat
- Splunk
- Symantec
- Tenable
- Trendmicro
CYBERSECURITY
MSSP
- Accenture
- Attos
- AT&T Cybersecurity
- BT Security
- BASE 4 - Hispam
- Deloitte
- Entelgy Security
- KPMG
- NTT Security
- Novared - Hispam
- Neosecure - Hispam
- Orange Cyberdefense
- PwC
- Telefonica Tech
- Thales
- Verizon Security