- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
LATEST NEWS
- 05 / 14 : 10:00 pm : Upcoming Speaking Engagements – Source: www.schneier.com
- 05 / 14 : 10:00 pm : Another Chrome Vulnerability – Source: www.schneier.com
- 05 / 14 : 7:03 pm : QakBot attacks with Windows zero-day (CVE-2024-30051) – Source: securelist.com
- 05 / 14 : 7:02 pm : Patch Tuesday, May 2024 Edition – Source: krebsonsecurity.com
- 05 / 14 : 7:00 pm : FCC names and shames Royal Tiger AI robocall crew – Source: go.theregister.com
- 05 / 14 : 7:00 pm : Cybersec chiefs team up with insurers to say ‘no’ to ransomware bullies – Source: go.theregister.com
- 05 / 14 : 7:00 pm : Telegram CEO calls out rival Signal, claiming it has ties to US government – Source: go.theregister.com
- 05 / 14 : 7:00 pm : Google, Apple gear to raise tracking tag stalker alarm – Source: go.theregister.com
- 05 / 14 : 7:00 pm : Visualize your critical cyber risks – Source: go.theregister.com
- 05 / 14 : 7:00 pm : NHS Digital hints at exploit sightings of Arcserve UDP vulnerabilities – Source: go.theregister.com
- 05 / 14 : 6:00 pm : Data Breaches in US Schools Exposed 37.6M Records – Source: www.infosecurity-magazine.com
- 05 / 14 : 6:00 pm : Ebury Botnet Operators Diversify with Financial and Crypto Theft – Source: www.infosecurity-magazine.com
- 05 / 14 : 6:00 pm : CISA and Partners Unveil Cybersecurity Guide For Civil Society Groups – Source: www.infosecurity-magazine.com
- 05 / 14 : 6:00 pm : NIST Confusion Continues as Cyber Pros Complain CVE Uploads Stalled – Source: www.infosecurity-magazine.com
- 05 / 14 : 6:00 pm : China Presents Defining Challenge to Global Cybersecurity, Says GCHQ – Source: www.infosecurity-magazine.com
- 05 / 14 : 6:00 pm : 44% of Cybersecurity Professionals Struggle with Regulatory Compliance – Source: www.infosecurity-magazine.com
- 05 / 14 : 6:00 pm : Russian Actors Weaponize Legitimate Services in Multi-Malware Attack – Source: www.infosecurity-magazine.com
- 05 / 14 : 6:00 pm : UK Insurance and NCSC Join Forces to Fight Ransomware Payments – Source: www.infosecurity-magazine.com
- 05 / 14 : 6:00 pm : Hackers Use DNS Tunneling to Scan and Track Victims – Source: www.infosecurity-magazine.com
- 05 / 14 : 5:01 pm : VMware makes Workstation Pro and Fusion Pro free for personal use – Source: www.bleepingcomputer.com
CISO STRATEGICS
CYBER ARCHITECTURE
SOC CSIRT OPERATIONS
CYBERSECURITY TOOLS
CYBERSECURITY VENDORS
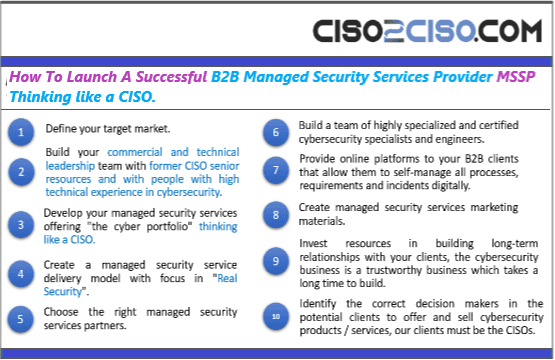
CYBERSECURITY MSSP
CYBER ORGANIZATIONS
CYBER REGULATIONS
EVENTS & CONFERENCES
VULNs & ZERO DAYS
LATEST CYBER NEWS

CISO2CISO Editors' Picks
CISO
STRATEGICS
- CISO Strategics
- CISO Learn & Leadership
- Cybersecurity for C-Levels
- Cybersecurity Trends & Insights
- Cyberseurity Awareness
- Cybercrimen Ecosystem
- Cybersecurity Measure & Metrics
- Cybersecurity Frameworks
- Cybersecurity Policy & Standars
- Fraud
- Information Security
- Osint - Humint
- Privacy
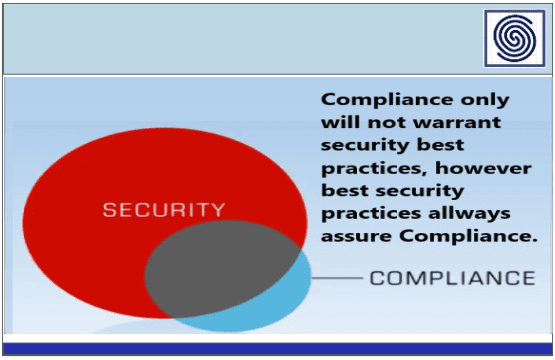
- Risk & Compliance
- Resilience
- Social Engineering
- Supply Chain Security
CYBER
ARCHITECTURE
- API Security
- Application Security
- Blockchain Security
- Cloud Security
- Data Security
- Defense in Depth
- DevSecOps
- Endpoint Security
- IA Security
- IOT Security
- MAC-OS Security
- Metaverse Security
- Micro segmentation
- Mitre Att&ck
- Mobile & 5G Security
- Network Security
- OT Security
- OWASP Security
- Perimeter Security
- SAP Security
- Telco & Carrier Security
- Zero Trust Security
SOC CSIRT
OPERATIONS
- Cyber Incidents & Attacks Notepad
- CSIRT Operations
- Data Leak & Breach Incidents Notepad
- DDOS Attacks
- DFIR - Forensics & Incident Response
- Dark & Deep Web
- SOC Operations
- SIEM Use Cases & Playbooks
- SOAR Authomation & Playbooks
- Malware & Ransomware
- Red - Blue & Purple Teams Operations
- Threat Intelligence
- Threat Hunting
- Vulnerabilities

CYBER
ORGs
- CCN-EU
- CSA
- CIS
- CISA
- DHS-US
- ENISA
- ISACA
- INCIBE-EU
- Mitre Att&ack
- NSA
- NIST Security
- SANS
- WEF
CYBER
CONFERENCES
Latest Published Posts
CYBERSECURITY
VENDORS
- Akamai
- A10 Networks
- Blackberry Cylance
- Cisco
- Cyberark
- Cloudfare
- Crowdstrike
- Checkpoint
- F5 Networks
- FyreEye
- Fortinet
- Guardicore
- IBM
- Kaspersky
- Mcafee - Trellix
- Mandiant
- Maltego
- Microsoft
- Netscope
- Palo Alto Networks
- RSA Security
- Redhat
- Splunk
- Symantec
- Tenable
- Trendmicro
CYBERSECURITY
MSSP
- Accenture
- Attos
- AT&T Cybersecurity
- BT Security
- BASE 4 - Hispam
- Deloitte
- Entelgy Security
- KPMG
- NTT Security
- Novared - Hispam
- Neosecure - Hispam
- Orange Cyberdefense
- PwC
- Telefonica Tech
- Thales
- Verizon Security