- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
LATEST NEWS
- 05 / 07 : 1:00 am : UK armed forces’ personal data hacked in MoD breach – Source: www.theguardian.com
- 05 / 07 : 1:00 am : New Lawsuit Attempting to Make Adversarial Interoperability Legal – Source: www.schneier.com
- 05 / 07 : 12:00 am : Citrix Addresses High-Severity Flaw in NetScaler ADC and Gateway – Source: www.darkreading.com
- 05 / 07 : 12:00 am : Supply Chain Breaches Up 68% Year Over Year, According to DBIR – Source: www.darkreading.com
- 05 / 07 : 12:00 am : LLMs & Malicious Code Injections: ‘We Have to Assume It’s Coming’ – Source: www.darkreading.com
- 05 / 07 : 12:00 am : AttackIQ Partners With Cyber Poverty Line Institute to Provide Academy Courses to Underserved Communities – Source: www.darkreading.com
- 05 / 07 : 12:00 am : BigID Launches Industry-First Hybrid Scanning for Cloud Native Workloads – Source: www.darkreading.com
- 05 / 07 : 12:00 am : Introducing the NetBeacon Institute: Empowering a Safer Web – Source: www.darkreading.com
- 05 / 07 : 12:00 am : AXA XL Introduces Endorsement to Help Public Companies Address SEC Cyber Reporting Costs – Source: www.darkreading.com
- 05 / 07 : 12:00 am : Microsoft Previews Feature to Block Malicious OAuth Apps – Source: www.darkreading.com
- 05 / 07 : 12:00 am : AT&T Splits Cybersecurity Services Business, Launches LevelBlue – Source: www.darkreading.com
- 05 / 07 : 12:00 am : The Psychological Underpinnings of Modern Hacking Techniques – Source: www.darkreading.com
- 05 / 06 : 11:00 pm : RSAC: Securing Foundational Tech Critical to Upholding Democratic Values, Says Blinken – Source: www.infosecurity-magazine.com
- 05 / 06 : 11:00 pm : RSAC: Threat Actors Weaponize Hacktivism for Financial Gain – Source: www.infosecurity-magazine.com
- 05 / 06 : 11:00 pm : RSAC: Law Enforcement Takedowns Force Ransomware Affiliates to Diversify – Source: www.infosecurity-magazine.com
- 05 / 06 : 11:00 pm : RSAC: 70% of Businesses Prioritize Innovation Over Security in Generative AI Projects – Source: www.infosecurity-magazine.com
- 05 / 06 : 11:00 pm : City of Wichita hit by a ransomware attack – Source: securityaffairs.com
- 05 / 06 : 11:00 pm : El Salvador suffered a massive leak of biometric data – Source: securityaffairs.com
- 05 / 06 : 11:00 pm : Finland authorities warn of Android malware campaign targeting bank users – Source: securityaffairs.com
- 05 / 06 : 8:00 pm : Strengthening Cyber Defense with Threat Intelligence Operations – Source: www.cyberdefensemagazine.com
CISO STRATEGICS
CYBER ARCHITECTURE
SOC CSIRT OPERATIONS
CYBERSECURITY TOOLS
CYBERSECURITY VENDORS
CYBERSECURITY MSSP
CYBER ORGANIZATIONS
CYBER REGULATIONS
EVENTS & CONFERENCES
VULNs & ZERO DAYS
LATEST CYBER NEWS

CISO2CISO Editors' Picks
CISO
STRATEGICS
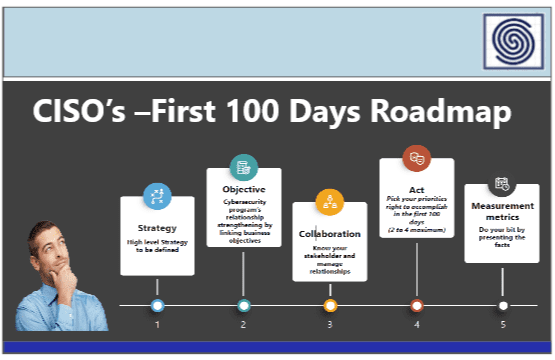
- CISO Strategics
- CISO Learn & Leadership
- Cybersecurity for C-Levels
- Cybersecurity Trends & Insights
- Cyberseurity Awareness
- Cybercrimen Ecosystem
- Cybersecurity Measure & Metrics
- Cybersecurity Frameworks
- Cybersecurity Policy & Standars
- Fraud
- Information Security
- Osint - Humint
- Privacy
- Risk & Compliance
- Resilience
- Social Engineering
- Supply Chain Security
CYBER
ARCHITECTURE
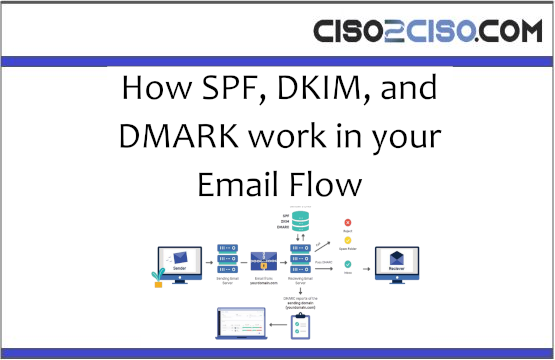
- API Security
- Application Security
- Blockchain Security
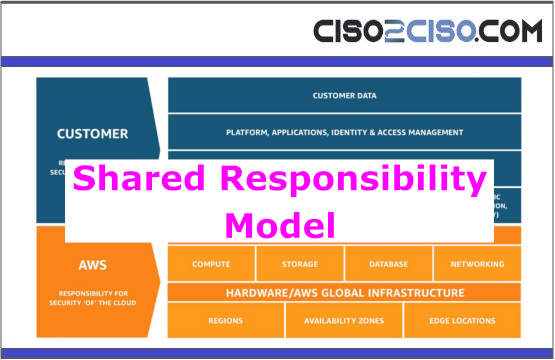
- Cloud Security
- Data Security
- Defense in Depth
- DevSecOps
- Endpoint Security
- IA Security
- IOT Security
- MAC-OS Security
- Metaverse Security
- Micro segmentation
- Mitre Att&ck
- Mobile & 5G Security
- Network Security
- OT Security
- OWASP Security
- Perimeter Security
- SAP Security
- Telco & Carrier Security
- Zero Trust Security
SOC CSIRT
OPERATIONS
- Cyber Incidents & Attacks Notepad
- CSIRT Operations
- Data Leak & Breach Incidents Notepad
- DDOS Attacks
- DFIR - Forensics & Incident Response
- Dark & Deep Web
- SOC Operations
- SIEM Use Cases & Playbooks
- SOAR Authomation & Playbooks
- Malware & Ransomware
- Red - Blue & Purple Teams Operations
- Threat Intelligence
- Threat Hunting
- Vulnerabilities

CYBER
ORGs
- CCN-EU
- CSA
- CIS
- CISA
- DHS-US
- ENISA
- ISACA
- INCIBE-EU
- Mitre Att&ack
- NSA
- NIST Security
- SANS
- WEF
CYBER
CONFERENCES
Latest Published Posts
CYBERSECURITY
VENDORS
- Akamai
- A10 Networks
- Blackberry Cylance
- Cisco
- Cyberark
- Cloudfare
- Crowdstrike
- Checkpoint
- F5 Networks
- FyreEye
- Fortinet
- Guardicore
- IBM
- Kaspersky
- Mcafee - Trellix
- Mandiant
- Maltego
- Microsoft
- Netscope
- Palo Alto Networks
- RSA Security
- Redhat
- Splunk
- Symantec
- Tenable
- Trendmicro
CYBERSECURITY
MSSP
- Accenture
- Attos
- AT&T Cybersecurity
- BT Security
- BASE 4 - Hispam
- Deloitte
- Entelgy Security
- KPMG
- NTT Security
- Novared - Hispam
- Neosecure - Hispam
- Orange Cyberdefense
- PwC
- Telefonica Tech
- Thales
- Verizon Security