- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
LATEST NEWS
- 05 / 03 : 12:01 pm : CEO who sold fake Cisco devices to US military gets 6 years in prison – Source: www.bleepingcomputer.com
- 05 / 03 : 12:01 pm : Bitwarden launches new MFA Authenticator app for iOS, Android – Source: www.bleepingcomputer.com
- 05 / 03 : 12:00 pm : Streamline NIS2 Compliance with Automation – Source: securityboulevard.com
- 05 / 03 : 12:00 pm : A Closer Look at Top 5 Vulnerabilities of April 2024 – Source: securityboulevard.com
- 05 / 03 : 12:00 pm : Insider Risk Digest: April – Source: securityboulevard.com
- 05 / 03 : 12:00 pm : CVE-2024-27322 Should Never Have Been Assigned And R Data Files Are Still Super Risky Even In R 4.4.0 – Source: securityboulevard.com
- 05 / 03 : 12:00 pm : The Persistent Threat of Path Traversal Vulnerabilities in Software Development – Source: securityboulevard.com
- 05 / 03 : 12:00 pm : What is Proxmox VE – and Why You Should Live Patch It – Source: securityboulevard.com
- 05 / 03 : 12:00 pm : GUEST ESSAY: A primer on how, why ‘dynamic baselining’ fosters accurate DDoS protection – Source: securityboulevard.com
- 05 / 03 : 12:00 pm : FIN7 Cybercrime Group Strikes US Auto Sector Using Carbanak – Source: securityboulevard.com
- 05 / 03 : 12:00 pm : RSAC 2024 Innovation Sandbox | Aembit: An IAM Platform for Cloud Workloads – Source: securityboulevard.com
- 05 / 03 : 7:00 am : Proofpoint Announces Availability of its Human-Centric Security Solutions in AWS Marketplace – Source: www.proofpoint.com
- 05 / 03 : 7:00 am : Proofpoint Bolsters Information Protection Offering with Cross-Channel DLP Capabilities that Address the New GenAI Reality for Organizations – Source: www.proofpoint.com
- 05 / 03 : 6:00 am : Billions of Android Devices Open to ‘Dirty Stream’ Attack – Source: www.darkreading.com
- 05 / 03 : 6:00 am : DPRK’s Kimsuky APT Abuses Weak DMARC Policies, Feds Warn – Source: www.darkreading.com
- 05 / 03 : 6:00 am : Software Security: Too Little Vendor Accountability, Experts Say – Source: www.darkreading.com
- 05 / 03 : 6:00 am : Hacker Sentenced After Years of Extorting Psychotherapy Patients – Source: www.darkreading.com
- 05 / 03 : 6:00 am : Dropbox Breach Exposes Customer Credentials, Authentication Data – Source: www.darkreading.com
- 05 / 03 : 6:00 am : Name That Edge Toon: Puppet Master – Source: www.darkreading.com
- 05 / 03 : 6:00 am : Intel Harnesses Hackathons to Tackle Hardware Vulnerabilities – Source: www.darkreading.com
CISO STRATEGICS
CYBER ARCHITECTURE
SOC CSIRT OPERATIONS
CYBERSECURITY TOOLS
CYBERSECURITY VENDORS
CYBERSECURITY MSSP
CYBER ORGANIZATIONS
CYBER REGULATIONS
EVENTS & CONFERENCES
VULNs & ZERO DAYS
LATEST CYBER NEWS

CISO2CISO Editors' Picks
CISO
STRATEGICS
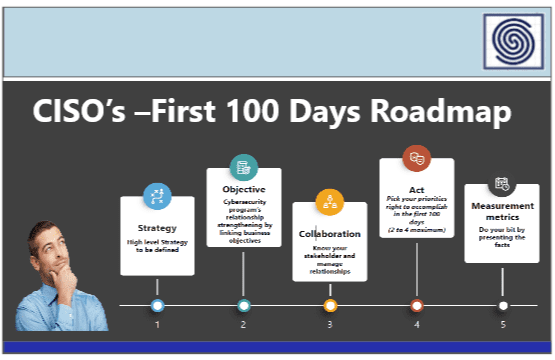
- CISO Strategics
- CISO Learn & Leadership
- Cybersecurity for C-Levels
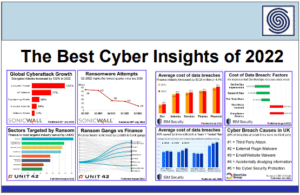
- Cybersecurity Trends & Insights
- Cyberseurity Awareness
- Cybercrimen Ecosystem
- Cybersecurity Measure & Metrics
- Cybersecurity Frameworks
- Cybersecurity Policy & Standars
- Fraud
- Information Security
- Osint - Humint
- Privacy
- Risk & Compliance
- Resilience
- Social Engineering
- Supply Chain Security
CYBER
ARCHITECTURE
- API Security
- Application Security
- Blockchain Security
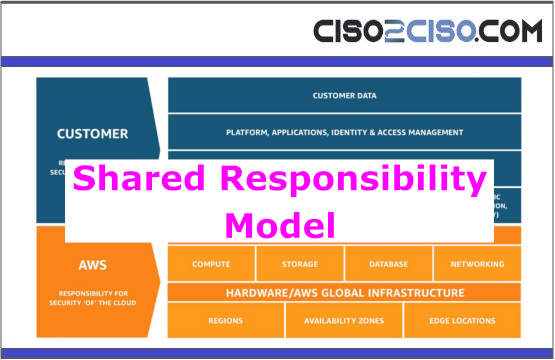
- Cloud Security
- Data Security
- Defense in Depth
- DevSecOps
- Endpoint Security
- IA Security
- IOT Security
- MAC-OS Security
- Metaverse Security
- Micro segmentation
- Mitre Att&ck
- Mobile & 5G Security
- Network Security
- OT Security
- OWASP Security
- Perimeter Security
- SAP Security
- Telco & Carrier Security
- Zero Trust Security
SOC CSIRT
OPERATIONS
- Cyber Incidents & Attacks Notepad
- CSIRT Operations
- Data Leak & Breach Incidents Notepad
- DDOS Attacks
- DFIR - Forensics & Incident Response
- Dark & Deep Web
- SOC Operations
- SIEM Use Cases & Playbooks
- SOAR Authomation & Playbooks
- Malware & Ransomware
- Red - Blue & Purple Teams Operations
- Threat Intelligence
- Threat Hunting
- Vulnerabilities

CYBER
ORGs
- CCN-EU
- CSA
- CIS
- CISA
- DHS-US
- ENISA
- ISACA
- INCIBE-EU
- Mitre Att&ack
- NSA
- NIST Security
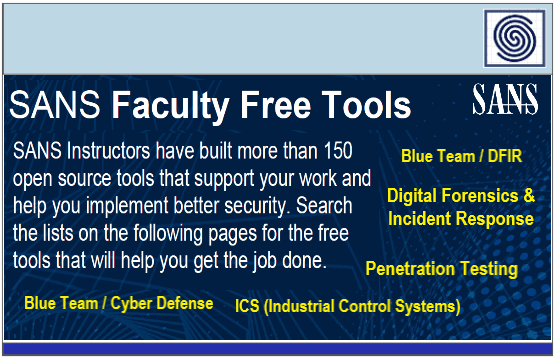
- SANS
- WEF
CYBER
CONFERENCES
Latest Published Posts
CYBERSECURITY
VENDORS
- Akamai
- A10 Networks
- Blackberry Cylance
- Cisco
- Cyberark
- Cloudfare
- Crowdstrike
- Checkpoint
- F5 Networks
- FyreEye
- Fortinet
- Guardicore
- IBM
- Kaspersky
- Mcafee - Trellix
- Mandiant
- Maltego
- Microsoft
- Netscope
- Palo Alto Networks
- RSA Security
- Redhat
- Splunk
- Symantec
- Tenable
- Trendmicro
CYBERSECURITY
MSSP
- Accenture
- Attos
- AT&T Cybersecurity
- BT Security
- BASE 4 - Hispam
- Deloitte
- Entelgy Security
- KPMG
- NTT Security
- Novared - Hispam
- Neosecure - Hispam
- Orange Cyberdefense
- PwC
- Telefonica Tech
- Thales
- Verizon Security