The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2022 State of the internet report by cencys
IntroductionThe Internet has revolutionized how we communicate, share information, and conduct business. Remote work arrangements, cloud adoption, and zero trust deployments have increased the Internet exposure...
Control System Defense – Know the Opponent by NSA and NISA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Propuesta de Anteproyecto de Ley de Proteccion de Datos Personales – Ley 25326 – Agencia de Acceso a la Información Publica – Gobierno de Argentina
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Guia Practica para la Gestion de Breachas de Datos Personas by ISMS and DPI
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Hiring a CISO – Super Guide for startups by Erdal Ozkaya
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2023 RISK IN FOCUS – Hot topics for internal auditors by ECIIA – VUCA context of very complex risks is coming to the world of internal audit by European Confederation of Institutes of Internal Auditing
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Five Automation Use Cases for Splunk SOAR by Splunk – Alert Enrichment , Phishing Investigation & Response, Endpoint Malware Triage, Command & Control Investigation & Containment, Threat Intelligence.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2022 Annual Report on Implementation – CSC 2.0 by Jiwon Ma – Mark Montgomery
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
INTRUSION DETECTION GUIDE – The fields leading experts show exactly how to detect, deter, and respond to security threats by PEERLYST
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
THE FUTURE OF CYBER ENABLED FINANCIAL CRIME – New Crimes, New Criminals, and Economic Warfare by ASU THREATCASTING LAB
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Windows 11 Security Book – Powerful security from chip to cloud – Built with zero-trust principles at the core to safeguard data and access anywhere, keeping you protected and productive.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CIS Critical Security Controls Version 8 – Mapping to PCI Data Security Standar (PCI DSS) v4.0 – Excel template tool ready for use – This document contains mappings of the CIS Controls and Safeguards to Payment Card Industry (PCI) Data Security Standard, v4.0.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The State of SaaS Ransomware Attack Preparedness – A survey of cloud data decision makers in large enterprises – Large enterprises are not fully prepared for cloud ransomware attacks – August 2022 by Odaseva
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
National Cyber Power Index 2022 – HARDVARD Kennedy School – BELFER CENTER for Science and International Affairs by Julia Voo, Irfan Hemani, Daniel Cassidy
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
THREAT HUNTING REPORT – Cybersecurity Insiders – DOMAINTOOLS 2021
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2022 Global Digital Trust Insights – The C-suite guide to simplifyng for cyber readiness today and tomorrow by PWC
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Customer Guidance for Reported Zero-day Vulnerabilities in Microsoft Exchange Server
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A Resilient Cybersecurity Professionn Chart the Path Forward – ICS2 CYBERSECURITY WORKFORCE STUDY – A Growing, Engaged Workforce
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SaaS Governance Best Practices Cloud by CSA Cloud Security Alliance
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Turning a Cybersecurity Strategy Into Reality A Holistic Performance Management Framework by BCG & STC
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
GUIDE TO EFFECTIVE RISK MANAGEMENT 3.0 – ALEX SIDORENKO – ELENA DEMIDENKO
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Windows Persistence Techniques by Joas Antonio
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
RDP Penetration Testing by IGNITE Technologies
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Operations Center – A Business Perspective by Aristeidis Michail
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
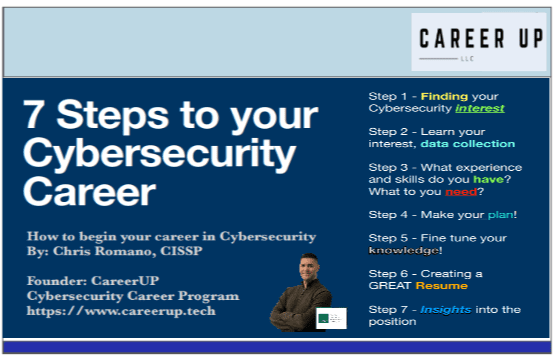
7 Steps to your Cybersecurity Career – How to begin your career in Cibersecurity By Chris Romano, CISSP
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
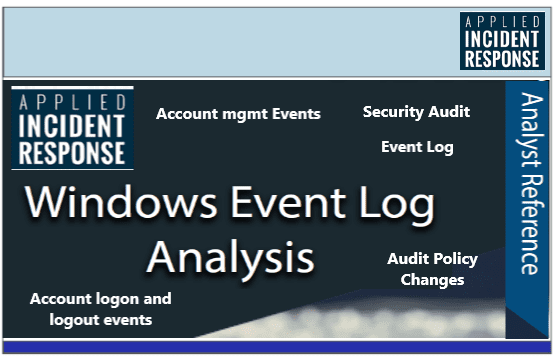
Windows Event Security Log Analysis
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
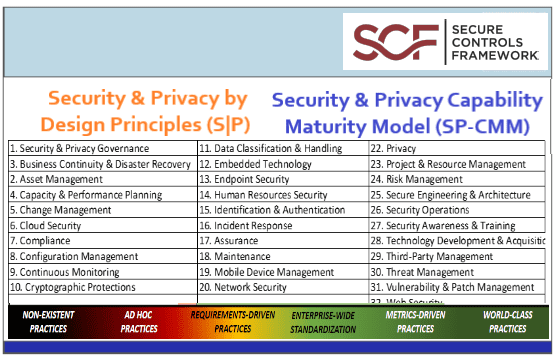
Secure & Privacy by Design Principles Framework & Security & Privacy Capability Maturity Model (SP-CMM) by SCF
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Ransomware as a service (RaaS) – An explainer guide to cybercrime´s newest business model
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A Solution Guide to Operational Technology (OT) Cybersecurity by Fortinet – The “air gap” between OT and IT has evaporated, and cyber threats pose a real challenge to OT organizations
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...