The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
5 Targets Hackers Look for When Attacking an OT Network by Cynalytica
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
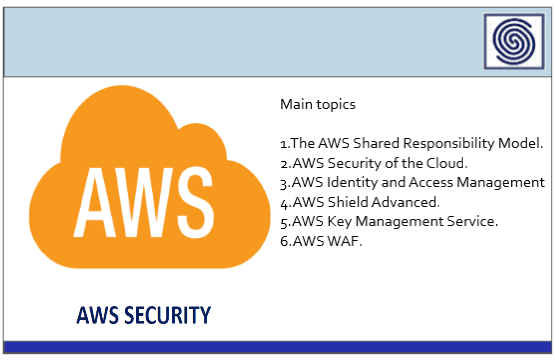
AWS Cloud Security – The AWS Shared Responsibility Model by Salman Abdulkarim
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
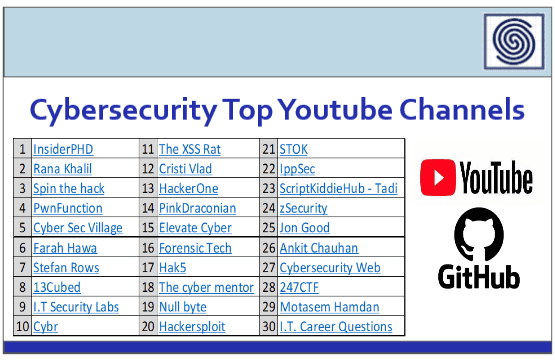
Cybersecurity 85 Top Youtube Channels on Github.com
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
KEEPING YOUR EMAIL SECURE – WHO DOES IT BEST ? A Especial analysis by Checkpoint.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Estate of Pentesting 2022 by Cobalt
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
TALE OF PHIHING – Some Phishing Techniques & Awareness by HADESS.IO
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ADVANCED SOCIAL ENGINEERING ATTACKS DECONSTRUCTED BY CFYRMA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Libro Ciberseguridad – Una estrategia Informatica-Militar by Alejandro Corletti Estrada – darfE.es
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
LAZARUS AND BYOVD – EVIL TO THE WINDOWS CORE By Peter Kalnai – Matej Havranek – ESET – virusbulletin.com
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity Best Practices for the Safety of Modern Vehicles – Updatd 2022 by NHTSA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
KERNEL MODE THREATS AND PRACTICAL DEFENSES BY Joe Desimone and Ganriel Landau – ENDGAME
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Building a Holistic Insider Risk Management Program – 5 elements that help companies have stronger data protection and security while protecting user trust by Microsoft Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Microsoft Implements Brute Force Attack Protection for All Windows Versions – As of October 11th, All Versions of Windows Can Automatically Block Admin Brute Force Attacks.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Detecting the Unknown – A Guide to Threat Hunting by UK Government
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2022 PRIVACY TECH VENDOR REPORT by IAPP
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CYBERSECURITY – BLUE TEAM TOOLKIT – A practical cybersecurity handbook for both tech and non-tech professionals by Nadean Tanner
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Pentesting Active Directory Environments by VARONIS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Definitive Guide to SOC as a Service – The Essential Elements of Advanced Threat Detection and Response by Crystal Bedell and Mark Bouchard – ARCTIC WOLF
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
OPEN SOURCE SOC TOOLS BY BONI YEAMIN
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ILLUMINATING DARKSIDE – TTPs, Tools, and the Trend Towards Defense Evasion by PICUS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Organising a Cyber Crisis Management Exercise – Positioning Cyber Resilience at the Highest Level by French National Cyber Security Agency (ANSSI) – CCA France
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
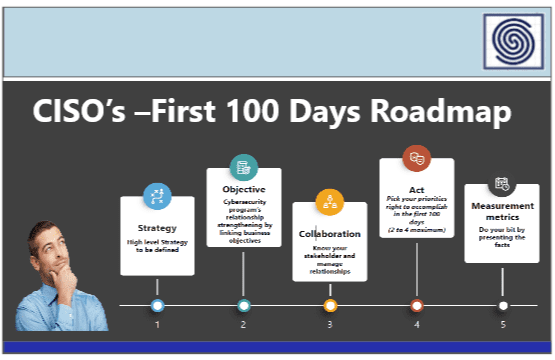
CISO’s – First 100 Days Roadmap – Your success as a security leader is determined largely by your first 100 days in the role.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
13 Questions for boards to ask about cyber security by Australian Cyber Security Centre – ACSC
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cyber Arms Watch An Analysis of Stated & Perceived Offensive Cyber Capabilities by The Hague Centre for Strategic Studies
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
DISTRIBUTED DENIAL OF SERVICE (DDOS) ATTACKS – Classification, Attacks, Challenges and Countermeasures – CRC Press Book
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
BASELINE CYBER SECURITY CONTROLS FOR SMALL AND MEDIUM ORGANIZATIONS V1.2 by Canadian Centre for CYBERSECURITY
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CISO2CISO Toolbox Series – Cyber Security Blogs / Cyber Security RSS Feeds List –
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
#EKOPARTY2022 – Ekoparty is a technical security conference born in 2001. +3000 guests, single track, workshops, trainings + ❤ – World-class experts, new breakthroughs, and professional training taught by the most recognized infosec professionals.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Protocols – SSL vs TLS – ALL YOU NEED TO KNOW.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...