Source: thehackernews.com – Author: . Dec 28, 2023NewsroomMalware / Cyber Threat A new malware loader is being used by threat actors to deliver a wide range...
Life in the Swimlane with Kevin Mata, Director of Cloud Operations and Automation – Source: securityboulevard.com
Source: securityboulevard.com – Author: Maycie Belmore Welcome to the “Life in the Swimlane” blog series. Here we will feature interviews with Swimlaners to learn more about...
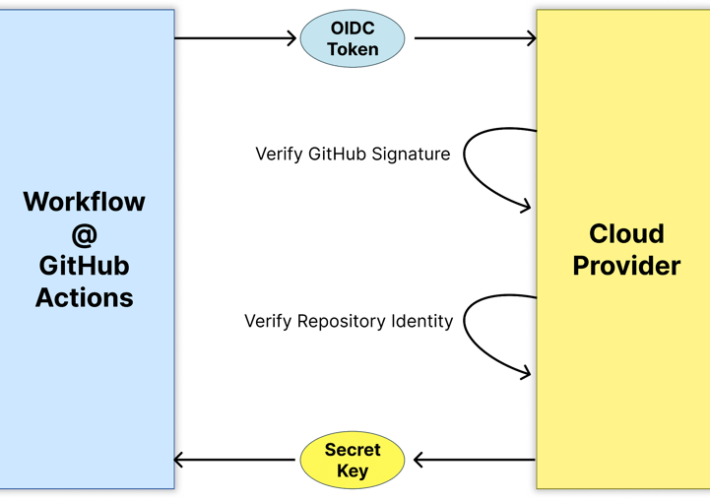
SLSA Provenance Blog Series, Part 3: The Challenges of Adopting SLSA Provenance – Source: securityboulevard.com
Source: securityboulevard.com – Author: Gal Ofri In part 2 of the series, we dived into the internals of the provenance document to understand its content and...
USENIX Security ’23 – Hailun Ding, Juan Zhai, Yuhong Nan, Shiqing Ma – ‘AIRTAG: Towards Automated Attack Investigation By Unsupervised Learning With Log Texts’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman No one specifically Someone on our general security team A dedicated person/team that handles cloud security Cloud architects and developers...
USENIX Security ’23 – Noé Zufferey, Mathias Humbert, Romain Tavenard, Kévin Huguenin ‘Watch Your Watch: Inferring Personality Traits From Wearable Activity Trackers’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman No one specifically Someone on our general security team A dedicated person/team that handles cloud security Cloud architects and developers...
MY TAKE: Rising geopolitical tensions suggest a dire need for tighter cybersecurity in 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido By Byron V. Acohido Russia’s asymmetrical cyber-attacks have been a well-documented, rising global concern for most of the 2000s. I recently...
Data In-Flight: Applying Zero Trust to Airline Travel and Content Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Votiro Team No matter which airport you travel through or how many times you travel through it, one element remains the same...
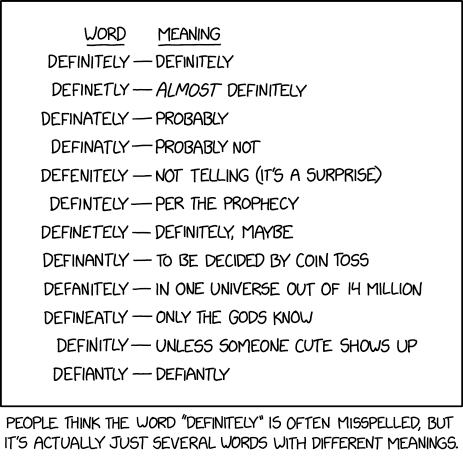
Randall Munroe’s XKCD ‘Definitely’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman No one specifically Someone on our general security team A dedicated person/team that handles cloud security Cloud architects and developers...
The (Face-)Book of Mammon [book review] – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Harley I have, at best, an uneasy relationship with Facebook. To paraphrase something that I’m writing at the moment (more about...
USENIX Security ’23 – ‘Auditory Eyesight: Demystifying μs-Precision Keystroke Tracking Attacks On Unconstrained Keyboard Inputs’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Yazhou Tu, Liqun Shan, Md Imran Hossen, Sara Rampazzi, Kevin Butler, Xiali Hei Many thanks to USENIX for publishing their...
Cyberattack Tempo Ratchets Up in Israel – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Cyber Israel Warns of a Wave of Phishing Attempts Mihir Bagwe (MihirBagwe)...
OnDemand Panel | Securing Operational Excellence: Insights into Fortifying OT Security – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Strengthening OT Security with HCLTech and Microsoft December 27, 2023 In an age reliant on operational technology, ensuring robust...
LIVE Webinar | A Zero Trust Journey for Data Security and Enterprise AI Implementations – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Next-Generation Technologies & Secure Development , Zero Trust Presented by LightBeam.AI 60 minutes ...
LIVE Webinar | From Access to Awareness: Unveiling the Zero Trust Data Landscape – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Priyadarshi Prasad Co-Founder and Chief Product Officer, LightBeam.ai Priyadarshi (PD) Prasad is the co-founder and chief product officer at LightBeam.ai. An...
New CMMC Rule Offers Tiered Security Levels for Contractors – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Government , Industry Specific Defense Department Proposes New Security Requirements for Defense Industrial Base Chris Riotta...
Lawmakers Push NIST for Transparency in AI Research Funding – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development NIST Fails to Provide Information on Award Process for AI...
Why CISOs Need to Make Cyber Insurers Their Partners – Source: www.darkreading.com
Source: www.darkreading.com – Author: Rob Jenks Source: Olekcii Mach via Alamy Stock Photo In the current threat landscape, the relationship between cyber-insurance providers and potential (or...
How Cybercriminals Will Sway 2024 US Elections, Or Try To – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Casimiro PT via Shutterstock Foreign interference actors, mostly operating out of Russia, Iran, and China, are ramping...
AI, Supply Chain Are Fertile Areas for Cybersecurity Investment – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jonathan Care, Contributing Writer Source: THANANIT SUNTIVIRIYANON via Alamy Stock Photo The past year has been a busy one for startups, with...
How to Prepare for DDoS Attacks During Peak Business Times – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security Source: Aleksey Funtap via Alamy Stock Photo Threat groups are constantly getting more sophisticated in their attempts to evade detection...
Critical Zero-Day in Apache OfBiz ERP System Exposes Businesses to Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 27, 2023NewsroomZero-Day / Vulnerability A new zero-day security flaw has been discovered in the Apache OfBiz, an open-source Enterprise Resource...
Chinese Hackers Exploited New Zero-Day in Barracuda’s ESG Appliances – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 27, 2023NewsroomZero-Day / Email Security Barracuda has revealed that Chinese threat actors exploited a new zero-day in its Email Security...
Mortgage firm LoanCare warns 1.3 million people of data breach – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Mortgage servicing company LoanCare is warning 1,316,938 borrowers across the U.S. that their sensitive information was exposed in a data...
Panasonic discloses data breach after December 2022 cyberattack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Panasonic Avionics Corporation, a leading supplier of in-flight communications and entertainment systems, disclosed a data breach affecting an undisclosed number...
New Xamalicious Android malware installed 330k times on Google Play – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A previously unknown Android backdoor named ‘Xamalicious’ has infected approximately 338,300 devices via malicious apps on Google Play, Android’s official...
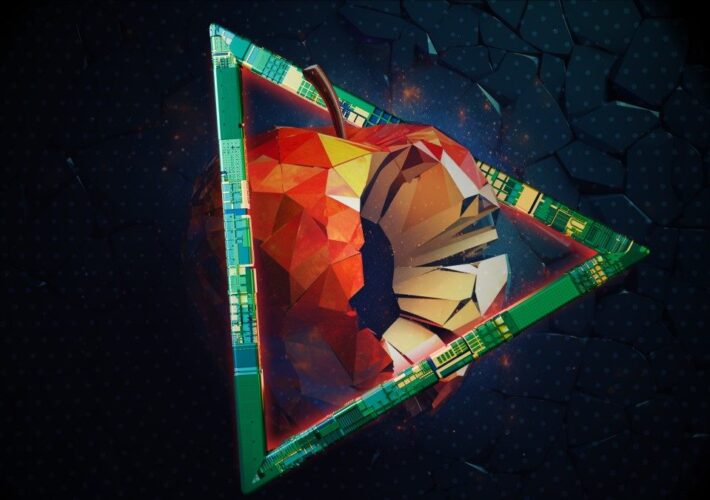
iPhone Triangulation attack abused undocumented hardware feature – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Operation Triangulation spyware attacks targeting iPhone devices since 2019 leveraged undocumented features in Apple chips to bypass hardware-based security protections....
Barracuda fixes new ESG zero-day exploited by Chinese hackers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Network and email security firm Barracuda says it remotely patched all active Email Security Gateway (ESG) appliances on December 21...
Yakult Australia confirms ‘cyber incident’ after 95 GB data leak – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma Yakult Australia, manufacturer of a probiotic milk drink, has confirmed experiencing a “cyber incident” in a statement to BleepingComputer. Both...
Operation Triangulation: The last (hardware) mystery – Source: securelist.com
Source: securelist.com – Author: Boris Larin Research Research 27 Dec 2023 minute read Today, on December 27, 2023, we (Boris Larin, Leonid Bezvershenko, and Georgy Kucherin)...
Police Warn Hundreds of Online Merchants of Skimmer Infections – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Law enforcement authorities in 17 countries discovered more than 400 online merchants infected with skimmers. The post Police Warn Hundreds...






![the-(face-)book-of-mammon-[book-review]-–-source:-securityboulevard.com](https://ciso2ciso.com/wp-content/uploads/2023/12/109252/the-face-book-of-mammon-book-review-source-securityboulevard-com.jpg)