Source: www.securityweek.com – Author: Eduard Kovacs The Akira ransomware group has taken credit for the recent attack that impacted Nissan Australia and New Zealand. The post...
CBS Parent National Amusements Discloses Year-Old Data Breach – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire CBS parent company National Amusements is informing 80,000 individuals of a December 2022 data breach. The post CBS Parent National...
Integris Health Data Breach Could Impact Millions – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Integris Health has started informing patients of a data breach impacting their personal information. The post Integris Health Data Breach...
Chinese Hackers Deliver Malware to Barracuda Email Security Appliances via New Zero-Day – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Chinese hackers exploited a zero-day tracked as CVE-2023-7102 to deliver malware to Barracuda Email Security Gateway (ESG) appliances. The post...
CISO Jim Rutt on the transition from marketing to cyber leader – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Jim Rutt is the CISO/CIO of The Dana Foundation, a private philanthropy group that explores the connections between neuroscience,...
A year in review – the most influential cyber stories of 2023 – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Twenty twenty-three breezed by in the blink of an eye, but before it eclipses us in entirety, let’s revisit...
Second Half of 2023 Threat Landscape Dominated by AI and Android Spyware – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The threat landscape has been bustling in the second half of 2023, according to cybersecurity provider ESET. In its Threat Report:...
New Sneaky Xamalicious Android Malware Hits Over 327,000 Devices – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 27, 2023NewsroomPrivacy / App Security A new Android backdoor has been discovered with potent capabilities to carry out a range...
Warning: Poorly Secured Linux SSH Servers Under Attack for Cryptocurrency Mining – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 27, 2023NewsroomMalware / Server Security Poorly secured Linux SSH servers are being targeted by bad actors to install port scanners...
A cyberattack hit Australian healthcare provider St Vincent’s Health Australia – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A cyberattack hit Australian healthcare provider St Vincent’s Health Australia Pierluigi Paganini December 27, 2023 St Vincent’s Health Australia, the...
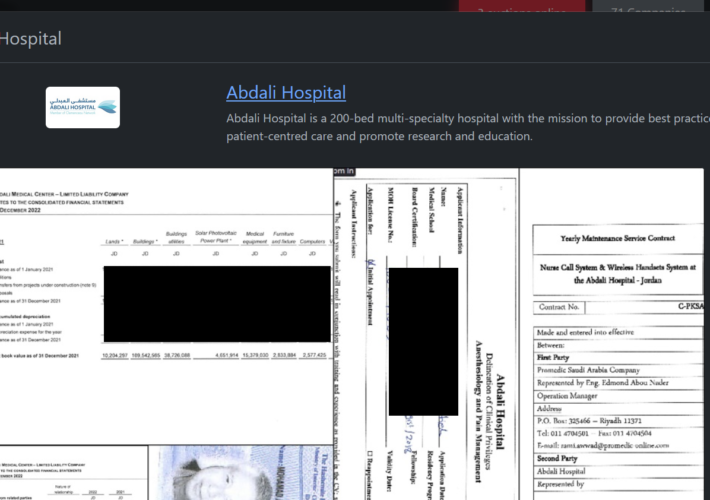
Rhysida ransomware group hacked Abdali Hospital in Jordan – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Rhysida ransomware group hacked Abdali Hospital in Jordan Pierluigi Paganini December 26, 2023 The Rhysida ransomware group claimed to have...
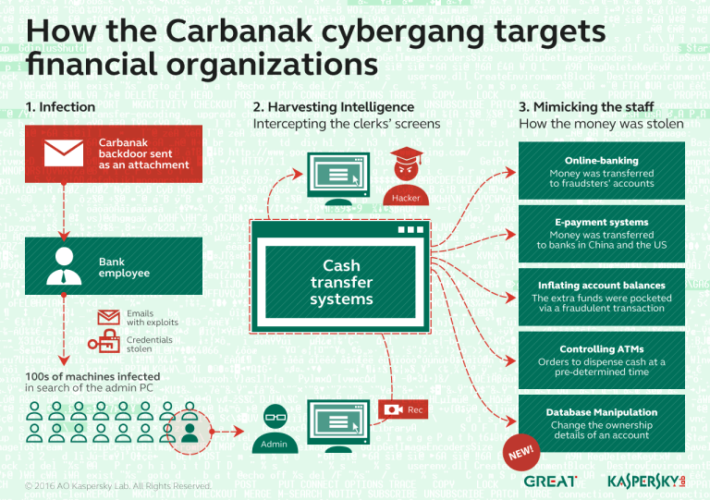
Carbanak malware returned in ransomware attacks – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Carbanak malware returned in ransomware attacks Pierluigi Paganini December 26, 2023 Researchers at NCC Group reported that in November they...
Resecurity Released a 2024 Cyber Threat Landscape Forecast – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Resecurity Released a 2024 Cyber Threat Landscape Forecast Pierluigi Paganini December 26, 2023 Cybersecurity company Resecurity has published the 2024...
Google Stops Collecting Location Data from Maps – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments JonKnowsNothing • December 26, 2023 8:14 AM @All re: Google Stops Collecting Location Data from Maps The small...
Europe Sees More Hacktivism, GDPR Echoes, and New Security Laws Ahead for 2024 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: SOPA Images Limited via Alamy Stock Photo An evolving geopolitical landscape has impacted cybersecurity in Europe this...
Cyber Employment 2024: Sky-High Expectations Fail Businesses & Job Seekers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Puhhha via Shutterstock Well-publicized estimates of a massive shortfall in cybersecurity workers have resulted in high expectations...
African Organizations Aim to Fix Cybersecurity in 2024 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Peter Kovac via Alamy Stock Photo Faced with numerous cybersecurity threats and challenges, but lacking adequate cyber...
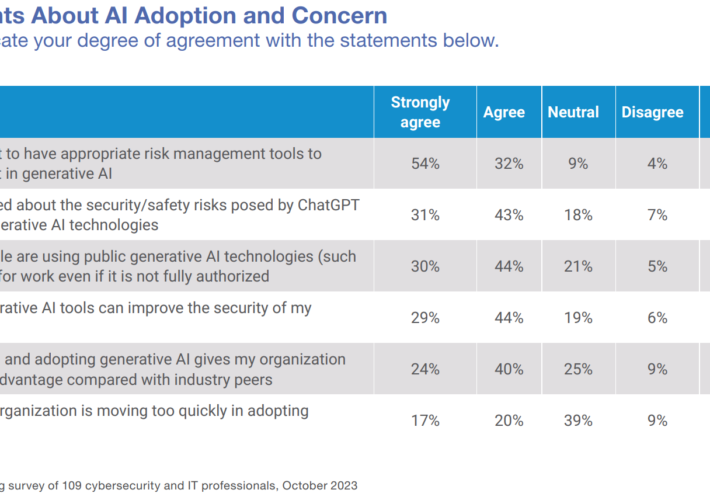
GenAI Tools Will Permeate All Areas of the Enterprise – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: The State of Generative AI in the Enterprise, Dark Reading Research, 2023 There is significant interest among organizations...
Security Pros Grapple With Ways to Manage GenAI Risk – Source: www.darkreading.com
Source: www.darkreading.com – Author: Edge Editors Source: The State of Generative AI in the Enterprise, Dark Reading, 2023 While security professionals are generally enthusiastic about the...
USENIX Security ’23 – Carter Slocum, Yicheng Zhang, Nael Abu-Ghazaleh, Jiasi Chen ‘Going Through The Motions: AR/VR Keylogging From User Head Motions’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman No one specifically Someone on our general security team A dedicated person/team that handles cloud security Cloud architects and developers...
Comic Agilé – Mikkel Noe-Nygaard, Luxshan Ratnaravi – #272 — Product Ops – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman No one specifically Someone on our general security team A dedicated person/team that handles cloud security Cloud architects and developers...
Wrapping up Q4 2023 : new detectors, your favorite features, and what’s coming next in GitGuardian – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ziad Ghalleb GitGuardian Secrets Detection More detectors = more secrets caught This quarter, our dedicated security research team has unveiled 14 new...
USENIX Security ’23 – Zhuolin Yang, Yuxin Chen, Zain Sarwar, Hadleigh Schwartz, Ben Y. Zhao, Haitao Zheng ‘Towards A General Video-Based Keystroke Inference Attack’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman No one specifically Someone on our general security team A dedicated person/team that handles cloud security Cloud architects and developers...
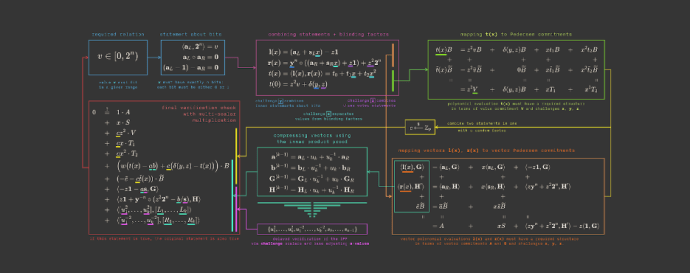
We’ve added more content to ZKDocs – Source: securityboulevard.com
Source: securityboulevard.com – Author: Trail of Bits By Jim Miller We’ve updated ZKDocs with four new sections and additions to existing content. ZKDocs provides explanations, guidance,...
Twas the day after Christmas, and this family was smart… – Source: securityboulevard.com
Source: securityboulevard.com – Author: Avast Blog No one specifically Someone on our general security team A dedicated person/team that handles cloud security Cloud architects and developers...
Best of 2023: Detecting CVE-2023-23397: How to Identify Exploitation of the Latest Microsoft Outlook Vulnerability – Source: securityboulevard.com
Source: securityboulevard.com – Author: Cyborg Security As we close out 2023, we at Security Boulevard wanted to highlight the most popular articles of the year. Following...
How to Unsend an Email and Save Yourself from Oops Moments? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ahona Rudra You drafted an email, hit the ‘send’ button, but forgot to attach the file, or got the recipient’s name wrong-...
SLAM Attack: New Vulnerability Targets Intel, AMD, Arm CPUs – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rohan Timalsina In a groundbreaking revelation, researchers from Vrije Universiteit Amsterdam have uncovered a formidable side-channel attack known as SLAM, posing a...
UEFI Failing: What to Know About LogoFAIL Attacks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Joao Correia Multiple UEFI vulnerabilities can lead to Linux, Windows, and Mac exploits LogoFAIL persists across operating system reinstallations It also extends...
The CyberSherpas guide on Generative Al Security It’s a Generative Al World
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...