Source: securityboulevard.com – Author: Kaseya Woohoo! What an exciting year 2023 turned out to be. Right from upgrading to VSA 10 to unlocking the efficiencies between...
Guardians of Tomorrow: Arkose Labs Shares the Top 3 Cyber Threats for 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jenn Jeffers If you missed our recent webinar, “Foreseeing the Future Threatscape: 2024’s Bad Actor Forecast,” there’s still time to catch up...
USENIX Security ’23 – ‘Squint Hard Enough: Attacking Perceptual Hashing With Adversarial Machine Learning’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Jonathan Prokos, Neil Fendley, Matthew Green, Roei Schuster, Eran Tromer, Tushar Jois, Yinzhi Cao Many thanks to USENIX for publishing...
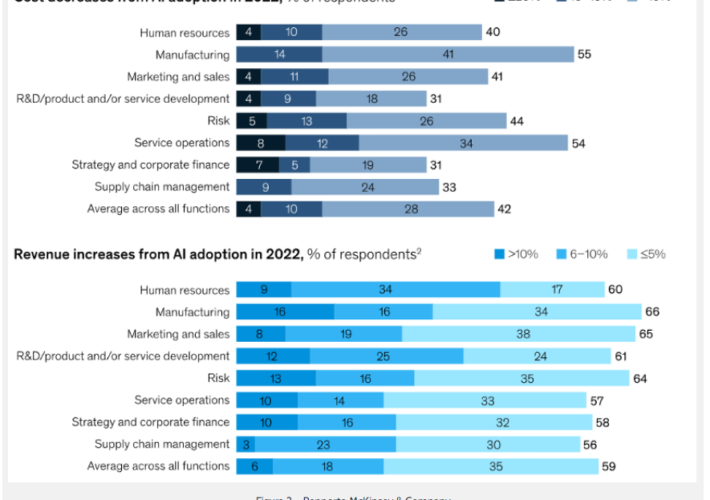
2023: Top 10 Cybersecurity Stats That Make You Go Hmmmmm – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rob Burgundy Rob Burgundy Lead Anchor, WMMX Rob Burgundy, the much better-looking younger brother of Ron Burgundy, is the charismatic lead anchor...
USENIX Security ’23 – Rethinking System Audit Architectures for High Event Coverage and Synchronous Log Availability – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters: Varun Gandhi, Sarbartha Banerjee, Aniket Agrawal, Adil Ahmad, Sangho Lee, Marcus Peinado Many thanks to USENIX for publishing their...
Google to Settle $5B ‘Incognito Mode’ Privacy Issue Lawsuit – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Legislation & Litigation , Privacy Deal Follows Court Ruling That Cleared the 4-Year-Old Class Action Claim...
New Cyberattack Wave Targets Albanian Parliament, Telecom – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Government Mobile Network Provider and National Flag Carrier Also Targeted Mihir...
Webinar | From Zero to Hero: Mastering the Multi-Cloud Landscape with Network Security Intelligence – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Cryptohack Roundup: Thunder Terminal Repels Attack – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cryptocurrency Fraud , Fraud Management & Cybercrime Also: Binance Ex-CEO’s Wealth Up $25B; Coinbase Refutes Senate Claims; $3M Scam Rashmi Ramesh...
Breach Roundup: Real Estate Firm Exposes Celebrity Data – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Breach Notification , Cybercrime , Fraud Management & Cybercrime Also: Yakult Australia Admits to Experiencing ‘Cybersecurity Incident’ Prajeet Nair (@prajeetspeaks) •...
Google Cloud Resolves Privilege Escalation Flaw Impacting Kubernetes Service – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 28, 2023NewsroomCloud Security / Data Protection Google Cloud has addressed a medium-severity security flaw in its platform that could be...
In Cybersecurity and Fashion, What’s Old Is New Again – Source: www.darkreading.com
Source: www.darkreading.com – Author: Chaz Lever Source: NicoElNino via Alamy Stock Photo COMMENTARY While distributed denial-of-service (DDoS) attacks and zero-day threats are nothing new in cybersecurity,...
Blockchain dev’s wallet emptied in “job interview” using npm package – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma A blockchain developer shares his ordeal over the holidays when he was approached on LinkedIn by a “recruiter” for a web development...
Ohio Lottery hit by cyberattack claimed by DragonForce ransomware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The Ohio Lottery was forced to shut down some key systems after a cyberattack affected an undisclosed number of internal...
Lockbit ransomware disrupts emergency care at German hospitals – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas German hospital network Katholische Hospitalvereinigung Ostwestfalen (KHO) has confirmed that recent service disruptions at three hospitals were caused by a...
10 top cybersecurity books that should be on your bookshelf – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: In an age of digital everything, do you even use a bookshelf anymore? Whether you read physical books, live...
Ohio Lottery Hit by Ransomware, Hackers Claim Theft of Employee and Player Data – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The DragonForce ransomware group has taken credit for the Ohio Lottery hack, claiming to have stolen millions of data records....
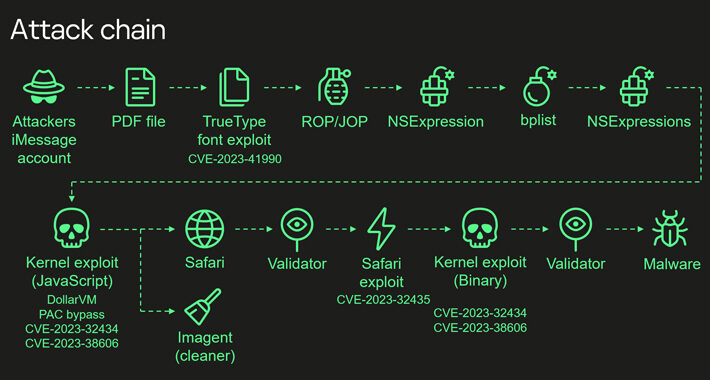
Mysterious Apple SoC Feature Exploited to Hack Kaspersky Employee iPhones – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire iOS zero-click attack targeting Kaspersky iPhones bypassed hardware-based security protections to take over devices. The post Mysterious Apple SoC Feature...
Barracuda Zero-Day Used to Target Government, Tech Organizations in US, APJ – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The new Barracuda ESG zero-day CVE-2023-7102 has been used by Chinese hackers to target organizations in the US and APJ...
Cyberattack Disrupts Operations of First American, Subsidiaries – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs A cyberattack appears to have caused significant disruption to the systems and operations of title insurer First American and its...
Refocusing on Cybersecurity Essentials in 2024: A Critical Review – Source: www.securityweek.com
Source: www.securityweek.com – Author: Torsten George By supplementing traditional perimeter defense mechanisms with principles of data integrity, identity management, and risk-based prioritization, organizations can reduce their...
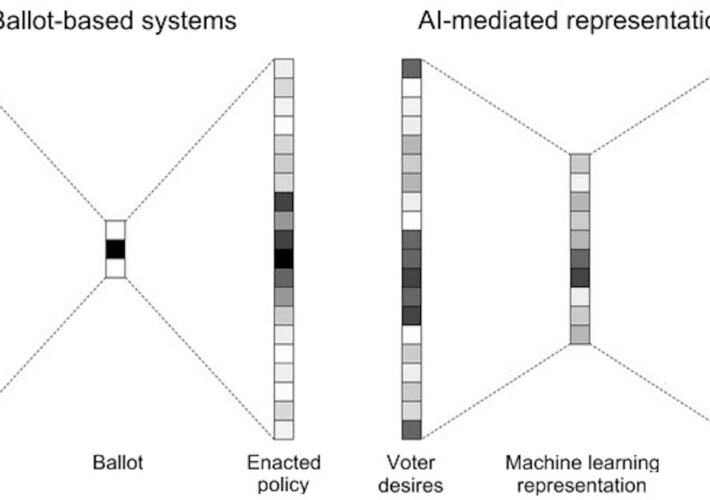
AI and Lossy Bottlenecks – Source: www.schneier.com
Source: www.schneier.com – Author: B. Schneier Artificial intelligence is poised to upend much of society, removing human limitations inherent in many systems. One such limitation is...
New iPhone Security Features to Protect Stolen Devices – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Apple is rolling out a new “Stolen Device Protection” feature that seems well thought out: When Stolen Device Protection is...
Experts warn of critical Zero-Day in Apache OfBiz – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts warn of critical Zero-Day in Apache OfBiz Pierluigi Paganini December 28, 2023 Experts warn of a zero-day flaw that...
Xamalicious Android malware distributed through the Play Store – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Xamalicious Android malware distributed through the Play Store Pierluigi Paganini December 27, 2023 Researchers discovered a new Android malware dubbed...
Barracuda fixed a new ESG zero-day exploited by Chinese group UNC4841 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Barracuda fixed a new ESG zero-day exploited by Chinese group UNC4841 Pierluigi Paganini December 27, 2023 Security firm Barracuda addressed...
Elections 2024, artificial intelligence could upset world balances – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Elections 2024, artificial intelligence could upset world balances Pierluigi Paganini December 27, 2023 Governments should recognize electoral processes as critical...
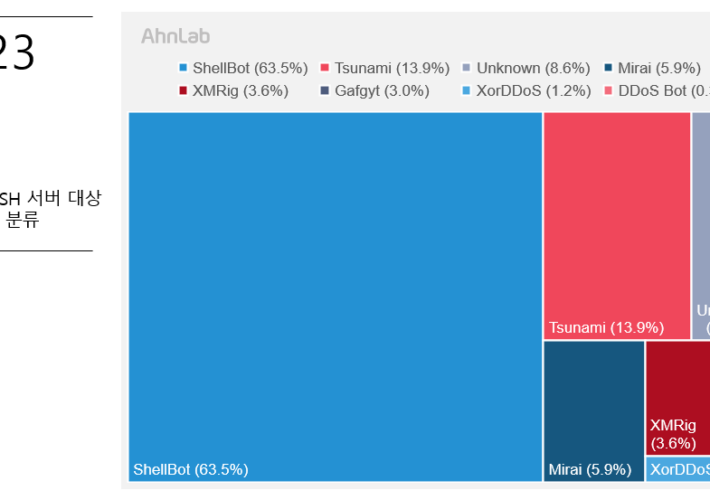
Experts analyzed attacks against poorly managed Linux SSH servers – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts analyzed attacks against poorly managed Linux SSH servers Pierluigi Paganini December 27, 2023 Researchers warn of attacks against poorly...
Most Sophisticated iPhone Hack Ever Exploited Apple’s Hidden Hardware Feature – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 28, 2023NewsroomSpyware / Hardware Security The Operation Triangulation spyware attacks targeting Apple iOS devices leveraged never-before-seen exploits that made it...