Source: www.darkreading.com - Author: Rob Wright CERT-FR's advisory follows last month's disclosure of a zero-day flaw...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Dark Reading Security
Source: www.darkreading.com - Author: Riaz Lakhani Together, we can foster a culture of collaboration and vigilance,...
Source: www.darkreading.com - Author: Robert Lemos, Contributing Writer Source: Michael Vi via ShutterstockThe latest supply chain...
Source: www.darkreading.com - Author: Kristina Beek The data leak underscores the larger issue of proprietary or...
Source: www.darkreading.com - Author: Rob Wright By weaponizing the ThrottleStop.sys driver, attackers are disrupting antivirus and...
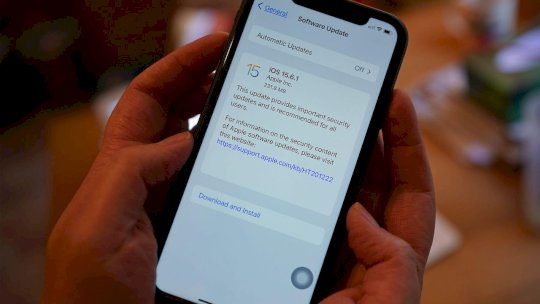
Source: www.darkreading.com - Author: Nate Nelson, Contributing Writer Even when a vulnerability is serious and a...
Source: www.darkreading.com - Author: Kristina Beek F5 plans to use CalypsoAI's platform to provide real-time threat...
Source: www.darkreading.com - Author: Jai Vijayan, Contributing Writer Source: Lightspring via ShutterstockA threat actor is using...
Source: www.darkreading.com - Author: Nate Nelson, Contributing Writer Researchers thought a Russian APT used a compromised...
Source: www.darkreading.com - Author: Alexander Culafi The pervasive Vidar infostealer has evolved with a suite of...
Source: www.darkreading.com - Author: Nate Nelson, Contributing Writer Researchers discovered that measures designed to make AI...
Source: www.darkreading.com - Author: Nate Nelson, Contributing Writer Researchers say a likely Russian APT used a...
Source: www.darkreading.com - Author: Arielle Waldman The threats may not be malicious, but they are more...
Source: www.darkreading.com - Author: Alexander Culafi Chinese state-backed threat actors are suspected of posing as Michigan...
Source: www.darkreading.com - Author: Nigel Douglas As Kubernetes becomes the foundation of enterprise infrastructure, the underlying...
Source: www.darkreading.com - Author: Elizabeth Montalbano, Contributing Writer With multiple persistence mechanisms, the modular malware can...
Source: www.darkreading.com - Author: Jai Vijayan, Contributing Writer Nearly half the CVEs Microsoft disclosed in its...
Source: www.darkreading.com - Author: Robert Lemos, Contributing Writer Firms cooperating with cybercrime syndicates in Burma and...
Source: www.darkreading.com - Author: Jai Vijayan, Contributing Writer Nearly half the CVEs Microsoft disclosed in its...
Source: www.darkreading.com - Author: Arielle Waldman While the jury is still out, it's clear that use...
Source: www.darkreading.com - Author: Kristina Beek The data breach, which occurred earlier this year, saw threat...
Source: www.darkreading.com - Author: Alexander Culafi Threat actors phished Qix's NPM account, then used their access...
Source: www.darkreading.com - Author: Elizabeth Montalbano, Contributing Writer Cybercriminal operations use the same strategy and planning...
Source: www.darkreading.com - Author: Kristina Beek The combined company will help customers separate data ingestion from...
Source: www.darkreading.com - Author: Jai Vijayan, Contributing Writer A threat actor is using a sophisticated EDR-killing...
Source: www.darkreading.com - Author: Rob Wright The breach kickstarted a massive supply chain attack that led...
Source: www.darkreading.com - Author: Amar Ramakrishnan Source: designer491 via Alamy Stock PhotoCOMMENTARYBusiness has slowed considerably in...
Source: www.darkreading.com - Author: Elizabeth Montalbano, Contributing Writer The China-backed threat actors have used the previously...
Source: www.darkreading.com - Author: Arielle Waldman Source: Nils Ackermann via Alamy Stock Photo Internet of Things...
Source: www.darkreading.com - Author: Rob Wright Exploitation of CVE-2025-42957 requires "minimal effort" and can result in...