Source: securityboulevard.com – Author: Votiro Team No matter which airport you travel through or how many times you travel through it, one element remains the same...
Author: Votiro Team
The Battle Against Cyber Shadows: Ensuring PCI-DSS Compliance Amidst Hidden Threats – Source: securityboulevard.com
Source: securityboulevard.com – Author: Votiro Team Digital footprints are expanding at an unprecedented rate, with individuals leaving traces of their credit or debit card information every...
An Enterprise Action Plan For CDR – Source: securityboulevard.com
Source: securityboulevard.com – Author: Votiro Team By David NeumanSenior Analyst, TAG Cyber [email protected] Introduction Information is the lifeblood of 21st-century businesses. They depend on the ability to...
The Hidden Dangers of Remote Code Execution (RCE) Exploits in Word Documents – Source: securityboulevard.com
Source: securityboulevard.com – Author: Votiro Team Remote code execution (RCE) attacks within Word documents have long been a part of the attacker’s arsenal. Their prevalence stems...
Averting Catastrophe: How Votiro Cloud Shielded ALYN Hospital from a Potentially Devastating Attack – Source: securityboulevard.com
Source: securityboulevard.com – Author: Votiro Team Every cyberattack is a disaster in its own way, but cyber threats that disrupt the critical services provided by healthcare...
Designed to Be Breached – Automated Document Consumption – Source: securityboulevard.com
Source: securityboulevard.com – Author: Votiro Team By David Neuman, Senior Analyst, TAG Cyber The use of automated document consumption and data extraction processes presents the opportunity...
Geopolitical Warfare in the Digital Age: The NATO Summit Cyber Incursion – Source: securityboulevard.com
Source: securityboulevard.com – Author: Votiro Team Cybercrime, once chiefly associated with shadowy individuals seeking personal gains, has rapidly evolved into a formidable weapon of modern warfare....
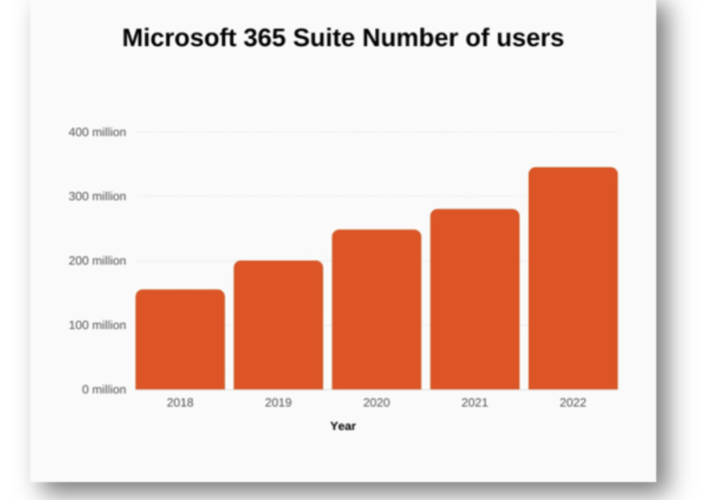
Adding File Security to Your Email Platform – Source: securityboulevard.com
Source: securityboulevard.com – Author: Votiro Team By John Masserini, Senior Research Analyst, TAG Cyber Since 2018, the user base of Microsoft Office 365 has steadily grown...
Outsmarting Advanced Cyber Threats: A Success Story of a Bank’s Defense Mechanism with Votiro Cloud for Email – Source: securityboulevard.com
Source: securityboulevard.com – Author: Votiro Team The banking sector is hyper-aware of the dangers of hackers penetrating their systems and trying to fortify themselves against any...
Redefining Security: Going Beyond Compliance in Financial Organizations (Plus Memes!) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Votiro Team Organizations often confuse the concept of being compliant with being secure. They assume that they must be appropriately protected once...