Source: www.bleepingcomputer.com – Author: Bill Toulas The Kansas City Area Transportation Authority (KCATA) announced it was targeted by a ransomware attack on Tuesday, January 23. KCATA...
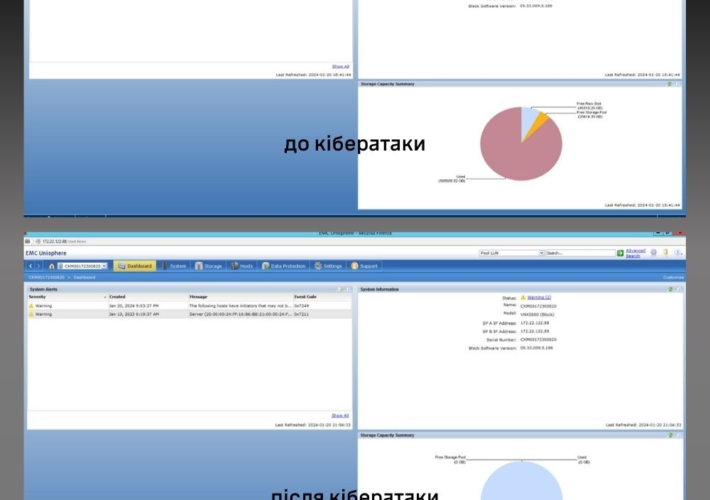
Pro-Ukraine hackers wiped 2 petabytes of data from Russian research center – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Pro-Ukraine hackers wiped 2 petabytes of data from Russian research center The Main Intelligence Directorate of Ukraine’s Ministry of Defense...
Participants earned more than $1.3M at the Pwn2Own Automotive competition – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Participants earned more than $1.3M at the Pwn2Own Automotive competition Bug bounty hunters earned more than $1.3 million for hacking...
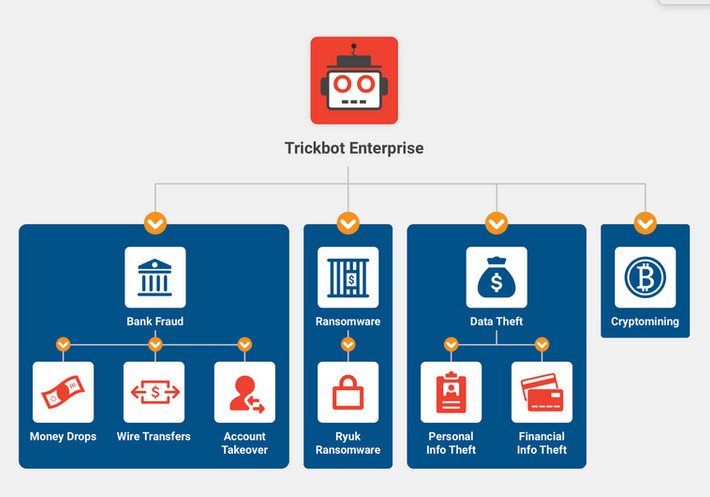
A TrickBot malware developer sentenced to 64 months in prison – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A TrickBot malware developer sentenced to 64 months in prison The Russian national malware developer Vladimir Dunaev was sentenced to...
AllaKore RAT Malware Targeting Mexican Firms with Financial Fraud Tricks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 27, 2024NewsroomMalware / Software Update Mexican financial institutions are under the radar of a new spear-phishing campaign that delivers a...
Malwarebytes vs. Norton (2024): Which Antivirus Solution Is Better? – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Jonathan Kalibbala We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
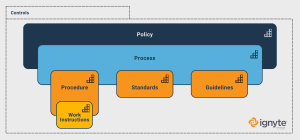
Cybersecurity Standards vs Procedures vs Controls vs Policies – Source: securityboulevard.com
Source: securityboulevard.com – Author: Max Aulakh Cybersecurity is a vast and complex field, and it’s made more complicated as technology – both infrastructure and in terms...
USENIX Security ’23 – Yue Xiao, Zhengyi Li, Yue Qin, Xiaolong Bai, Jiale Guan, Xiaojing Liao, and Luyi Xing – Lalaine: Measuring and Characterizing Non-Compliance of Apple Privacy Labels – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – Yue Xiao, Zhengyi Li, Yue Qin, Xiaolong...
DevSecOps maturity model: A beginner’s guide – Source: securityboulevard.com
Source: securityboulevard.com – Author: Aaron Linskens In recent years, DevSecOps swiftly emerged as a crucial new paradigm in software development, prioritizing the integration of security into...
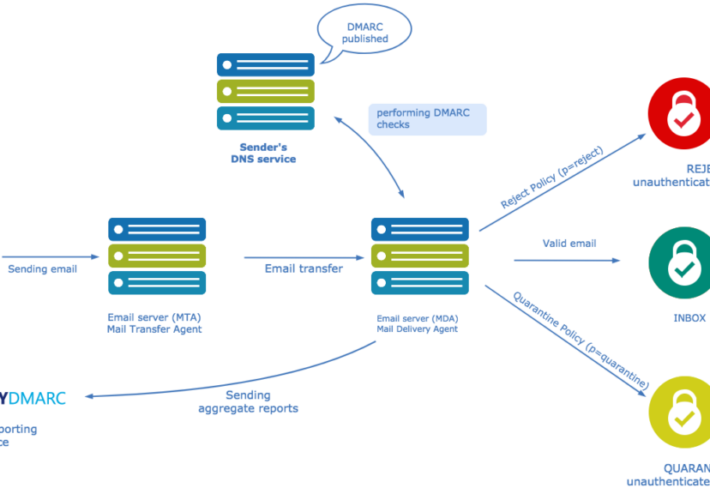
What is DMARC? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ani Avetisyan With the rising volume of fraudulent emails and AI-enhanced phishing scams, industry giants such as Google, Yahoo, and Microsoft have...
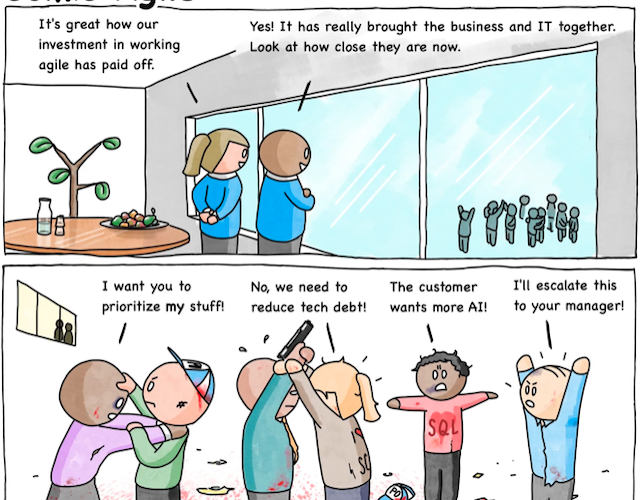
Comic Agilé – Mikkel Noe-Nygaard, Luxshan Ratnaravi – #276 – Bringing Business and IT Together – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Hot Topics Cybersecurity Standards vs Procedures vs Controls vs Policies USENIX Security ’23 – Yue Xiao, Zhengyi Li, Yue Qin,...
Cyber security and AI: Should machines be included in your training program? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Scott Wright The way AI stores data is a huge concern. As security managers, it makes sense that we are hesitant to...
USENIX Security ’23 – POLICYCOMP: Counterpart Comparison of Privacy Policies Uncovers Overbroad Personal Data Collection Practices – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Hot Topics Cybersecurity Standards vs Procedures vs Controls vs Policies USENIX Security ’23 – Yue Xiao, Zhengyi Li, Yue Qin,...
QR Code Scammers are Changing Tactics to Evade Detection – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Check Point researchers last year saw a 587% increase between August and September of phishing attacks enticing unsuspecting targets to...
90 Days of Learning, Good Surprises and Extreme Optimism – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Callahan January is often a time for reflection, and setting goals and aspirations for the months and the year ahead. It’s...
Why We Need to Cultivate a Confidential Computing Ecosystem – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ijlal Loutfi Researchers have been working on solutions for runtime security for years now. Computing data and deriving value from it —...
Developers Hold the New Crown Jewels. Are They Properly Protected? – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Aaron Bray, CEO. Phylum Cybersecurity has changed dramatically in the last four years. During the pandemic, organizations around the...
Civil Society Sounds Alarms on UN Cybercrime Treaty – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Government Final Round of Negotiations Set to Begin on Monday Akshaya Asokan (asokan_akshaya) •...
Therapy Provider Notifying 4 Million Patients of PJ&A Hack – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Breach Notification , Cybercrime Concentra Health Services Joins List of Those Affected in Transcriber’s Data Breach...
ISMG Editors: Emerging AI Tech for Cloud Security in 2024 – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cloud Security , Security Operations , Video Payments Expert Troy Leach Joins the Panel to Cover AI, Zero Trust and IoT...
CISA Aiming to Improve SBOM Implementation With New Guidance – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Government , Industry Specific , Software Bill of Materials (SBOM) US Cyber Agency Issues Step-by-Step Guide to Build Software Bills of...
Wyden Releases Documents Confirming the NSA Buys Americans’ Internet Browsing Records – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Washington, D.C. – U.S. Senator Ron Wyden, D-Ore., released documents confirming the National Security Agency buys Americans’ internet records, which can...
Bastille Raises $44M Series C Investment Led by Goldman Sachs Asset Management – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Santa Cruz, CA – Jan. 25, 2024 – Bastille Networks, Inc., a leading supplier of wireless threat intelligence technology to high-tech,...
Newly ID’ed Chinese APT Hides Backdoor in Software Updates – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Imaginechina Limited via Alamy Stock Photo Since 2018, a previously unknown Chinese threat actor has been using...
Microsoft Shares New Guidance in Wake of ‘Midnight Blizzard’ Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: dennizn via Shutterstock Microsoft has released new guidance for organizations on how to protect against persistent nation-state...
Series of Cyberattacks Hit Ukrainian Critical Infrastructure Organizations – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Andrii Dragan via Alamy Stock Photo Several Ukrainian critical infrastructure entities — including the country’s largest state-owned oil...
Saudi Arabia Boosts Railway Cybersecurity – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Leyden, Contributing Writer Source: CelCinar via Alamy Stock Photo The Saudi Railway Company (SAR) has announced a partnership with “sirar by...
Redefining Cybersecurity for a Comprehensive Security Posture – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ayan Halder Source: Andriy Popov via Alamy Stock Photo Cybersecurity is the practice of securing businesses’ infrastructure and endpoints from unauthorized access....
ICS Ransomware Danger Rages Despite Fewer Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Source: Sergey Ryzhov via Alamy Stock Photo Despite takedowns of top ransomware groups, those remaining threat actors...
Pegasus Spyware Targets Togolese Journalists’ Mobile Devices – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Mario Martija Sevilla via Alamy Stock Photo Cyberattackers have installed the Pegasus spyware on the phones of multiple...