Source: www.infosecurity-magazine.com – Author: 1 Teenagers from Western English-speaking countries are increasingly targeted by financial sextortion attacks conducted by Nigeria-based cybercriminals, the Network Contagion Research Institute...
Microsoft Provides Defense Guidance After Nation-State Compromise – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Microsoft has provided new details for responders to the Russian nation-state attack that compromised its systems earlier in January, and issued...
Dark Web Drugs Vendor Forfeits $150m After Guilty Plea – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A prolific dark web drugs vendor has pleaded guilty and agreed to forfeit $150m, the largest single seizure ever taken by...
CI/CD at Risk as Exploits Released For Critical Jenkins Bug – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Software developers have been told to urgently patch their Jenkins servers after exploits were published for a new critical vulnerability in...
Experts detailed Microsoft Outlook flaw that can leak NTLM v2 hashed passwords – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts detailed Microsoft Outlook flaw that can leak NTLM v2 hashed passwords A flaw in Microsoft Outlook can be exploited...
NSA buys internet browsing records from data brokers without a warrant – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini NSA buys internet browsing records from data brokers without a warrant The U.S. National Security Agency (NSA) admitted to buying...
Ukraine’s SBU arrested a member of Pro-Russia hackers group ‘Cyber Army of Russia’ – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Ukraine’s SBU arrested a member of Pro-Russia hackers group ‘Cyber Army of Russia’ Ukraine’s security service, the SBU, announced that it...
Multiple PoC exploits released for Jenkins flaw CVE-2024-23897 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Multiple PoC exploits released for Jenkins flaw CVE-2024-23897 Multiple proof-of-concept (PoC) exploits for recently disclosed critical Jenkins vulnerability CVE-2024-23897 have...
NSA Admits Secretly Buying Your Internet Browsing Data without Warrants – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 29, 2024NewsroomSurveillance / Data Privacy The U.S. National Security Agency (NSA) has admitted to buying internet browsing records from data...
Malicious PyPI Packages Slip WhiteSnake InfoStealer Malware onto Windows Machines – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 29, 2024NewsroomPyPI Repository / Malware Cybersecurity researchers have identified malicious packages on the open-source Python Package Index (PyPI) repository that...
Exploits released for critical Jenkins RCE flaw, patch now – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Multiple proof-of-concept (PoC) exploits for a critical Jenkins vulnerability allowing unauthenticated attackers to read arbitrary files have been made publicly...
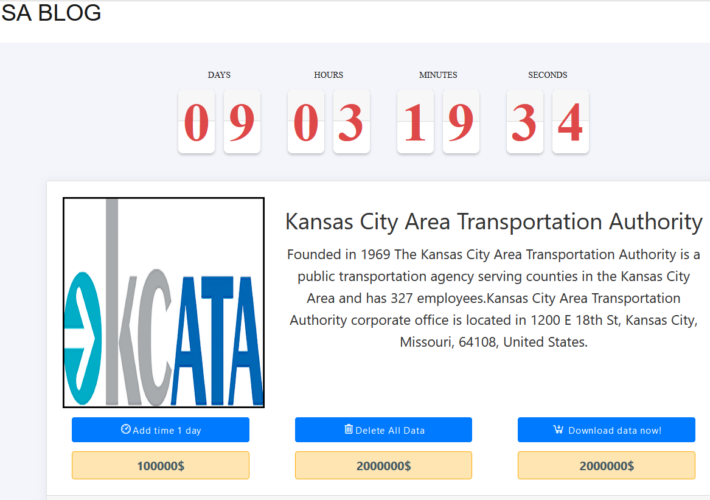
Kansas City public transportation authority hit by ransomware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Kansas City Area Transportation Authority (KCATA) announced it was targeted by a ransomware attack on Tuesday, January 23. KCATA...
NASCIO, PTI on What’s Coming in 2024 for State and Local IT – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lohrmann on Cybersecurity Every January, NASCIO and PTI release their forecasts for the coming year based on what government leaders are saying....
Navigating the Future: DevOps Predictions for 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Esther Han As technology continues to evolve at an unprecedented pace, the field of DevOps is no exception. DevOps, the cultural and...
Doubling Down on Security: The Critical Role of Two-Factor Authentication – Source: securityboulevard.com
Source: securityboulevard.com – Author: Leigh Dow Safeguarding our online accounts has never been more crucial. One of the most effective tools at our disposal is Two-Factor...
Zero-day Confluence RCE Vulnerability Blocked by Contrast Runtime Security | CVE-2023-22527 | Contrast Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Joseph Beeton, Senior Application Security Researcher, Contrast Security Security Bloggers Network Home » Security Bloggers Network » Zero-day Confluence RCE Vulnerability Blocked...
Medusa ransomware attack hit Kansas City Area Transportation Authority – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Medusa ransomware attack hit Kansas City Area Transportation Authority Medusa ransomware gang claimed responsibility for the attack against the Kansas...
Security Affairs newsletter Round 456 by Pierluigi Paganini – INTERNATIONAL EDITION – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Medusa ransomware attack hit Kansas City Area Transportation Authority | Security Affairs newsletter Round 456 by Pierluigi Paganini – INTERNATIONAL...
Weekly Update 384 – Source: www.troyhunt.com
Source: www.troyhunt.com – Author: Troy Hunt I spent longer than I expected talking about Trello this week, in part because I don’t feel the narrative they...
How Kratikal Helps Businesses Prevent Cyber Attacks? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Riddika Grover The rise in cyber attacks has become a major worry. This issue is for organizations where data storage and technical...
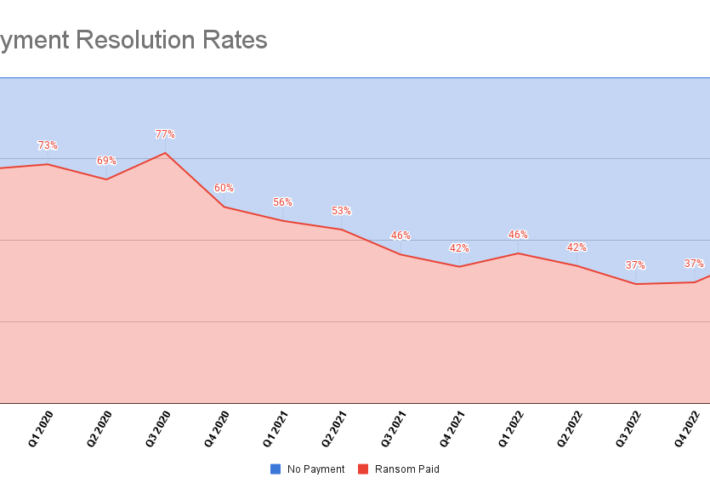
New Ransomware Reporting Requirements Kick in as Victims Increasingly Avoid Paying – Source: securityboulevard.com
Source: securityboulevard.com – Author: Bill Siegel Table of Contents Ransomware Bans Payment Rates Types of Ransomware Attack Vectors & TTPs Industries Impacted As the year turns,...
Novel Threat Tactics, Notable Vulnerabilities, Current Trends, and Data Leaks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Pondurance Every month, the Pondurance team hosts a webinar to keep clients current on the state of cybersecurity. In December, the team...
Friday Squid Blogging: Footage of Black-Eyed Squid Brooding Her Eggs – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Friday Squid Blogging: Footage of Black-Eyed Squid Brooding Her Eggs Amazing footage of a black-eyed squid (Gonatus onyx) carrying...
NRC Issues Recommendations for Better Network, Software Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jeffrey Schwartz, Contributing Writer Source: Olivier Le Moal via Alamy Stock Photo The Network Resilience Coalition issued recommendations intended to improve network security infrastructure...
CISO Corner: Deep Dive Into SecOps, Insurance, & CISOs’ Evolving Role – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Panther Media GmbH via Alamy Stock Photo Welcome to CISO Corner, Dark Reading’s weekly...
Google Kubernetes Clusters Suffer Widespread Exposure to External Attackers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Artemis Diana via Alamy Stock Photo The authentication mechanism within the Google Kubernetes Engine (GKE) has a...
Hackers Blast Violent Gaza Message at a Popular Israeli Movie Theater – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Bildagentur-online/Schoening via Alamy Stock Photo On Jan. 23, Turkish hacktivists projected political messages about the war in...
The CISO Role Undergoes a Major Evolution – Source: www.darkreading.com
Source: www.darkreading.com – Author: Mark Bowling Source: Panther Media GmbH via Alamy Stock Photo COMMENTARY We are in a time of major evolution for the chief...
Hook Younger Users With Cybersecurity Education Designed for Them – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tatiana Walk-Morris Source: Andrey Popov via Adobe Stock Photo Even though baby boomers have garnered a reputation for being less digitally savvy...
The Week in Ransomware – January 26th 2024 – Govts strike back – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Governments struck back this week against members of ransomware operations, imposing sanctions on one threat actor and sentencing another to...