Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Roman Samborskyi via Alamy Stock Photo It’s no secret that burnout is an epidemic among cybersecurity professionals...
Sneaky Shellcode: Windows Fibers Offer EDR-Proof Code Execution – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Robert K. Chin via Alamy Stock Photo Windows fibers, little-known components of Windows OS,...
Nigeria & Romania Ranked Among Top Cybercrime Havens – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Wavebreakmedia Ltd IFE-221116 via Alamy Stock Photo An academic research project to gain insight into which nations...
Open Source Tool Looks for Signals in Noisy AWS Cloud Logs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Pop Tika via Shutterstock When investigating a potential attack on cloud services, Daniel Bohannon frequently has to...
Change Healthcare data for sale on dark web as fallout from ransomware attack spirals out of control – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley February’s crippling ransomware attack against Change Healthcare, which saw prescription orders delayed across the United States, continues to have serious...
3.5 million Omni Hotel guest details held to ransom by Daixin Team – Source: www.exponential-e.com
Source: www.exponential-e.com – Author: Graham Cluley The international hotel chain Omni Hotels & Resorts has confirmed that a cyberattack last month saw it shut down its...
Police smash LabHost international fraud network, 37 arrested – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley Police have successfully infiltrated and disrupted the fraud platform “LabHost”, used by more than 2,000 criminals to defraud victims worldwide....
Smashing Security podcast #368: Gary Barlow, and a scam turns deadly – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Take That’s Gary Barlow chats up a pizza-slinging granny from Essex via Facebook, or does he? And a scam takes...
DarkRace Ransomware
DarkRace ransomware, a variant of Lockbit, utilizes leaked source code for its operations. It employs advanced techniques such as runtime decryption of XML data and encryption...
Cybersecurity and resiliency of Europe’s communications infrastructures and networks
This report presents a high-level risk assessment conducted by the NIS Cooperation Group, in collaboration with the Commission and ENISA, focusing on the vulnerabilities and threats...
The Art of Data Exfiltration
The document discusses various covert data exfiltration techniques used in cybersecurity. It covers methods like using cloakify tools to transform files into different formats for hidden...
DATA PRIVACY
Essential Data Privacy Checklist The document outlines a comprehensive checklist for data privacy compliance, covering various key areas such as Data Subject Rights, Cross-Border Data Transfers,...
DEFENDING APIS
API SECURITY MATURITY MODEL WITH SECURE CODING PRACTICES ACTICES IN.NET, JAVA The document covers the implementation of JWT authentication in Java using Spring Security and discusses...
DuneQuixote campaign targets Middle Eastern entities with “CR4T” malware – Source: securelist.com
Source: securelist.com – Author: GReAT Introduction In February 2024, we discovered a new malware campaign targeting government entities in the Middle East. We dubbed it “DuneQuixote”;...
Building Resilience Through Strategic Risk Management
Building resilience through strategic risk management is essential for organizational success and preparedness for disruptions. It involves fostering a strong risk culture, prioritizing diversity in risk...
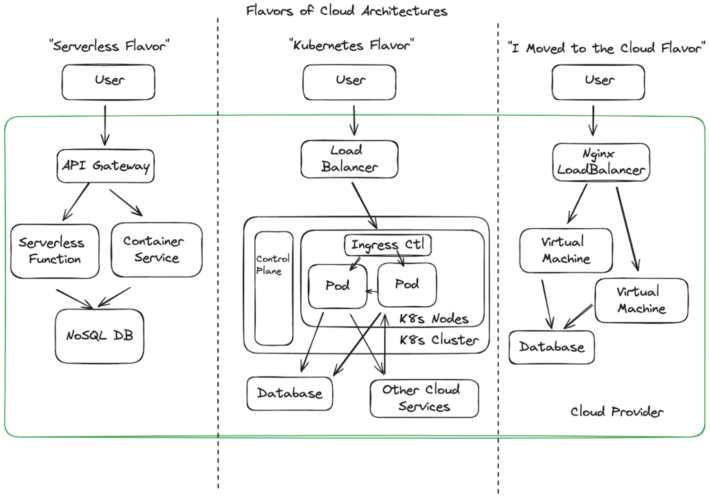
How to Design a Secure Serverless Architecture
Serverless platforms enable developers to develop and deploy faster, allowing an easy way to move to Cloud-native services without managing infrastructures like container clusters or virtual...
Detecting Brute Force Attacks
The document discusses detecting brute force attacks, highlighting methods like dictionary attacks, offline brute force attacks, and rainbow table attacks. It emphasizes the importance of strong...
10 must-know benefits of cyber security managed services (MSSPs) – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Three quarters of CEOs (74%) are concerned about their business’s ability to avert or limit damage from a cyber...
Phishing Email Analysis
The document delves into the intricacies of email phishing analysis, emphasizing the importance of scrutinizing email headers to detect potential phishing attempts. It highlights key elements...
Cisco Taps AI and eBPF to Automate Security Operations – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard Cisco today launched a framework that leverages artificial intelligence (AI) to test a software patch in a digital twin running...
Palo Alto Networks PAN-OS Command Injection Vulnerability (CVE-2024-3400) – Source: securityboulevard.com
Source: securityboulevard.com – Author: NSFOCUS Overview Recently, NSFOCUS CERT detected that Palo Alto Networks issued a security announcement and fixed the command injection vulnerability (CVE-2024-3400) in...
Q&A With Axiad’s New Chief Product Officer: Alex Au Yeung – Source: securityboulevard.com
Source: securityboulevard.com – Author: Axiad Earlier this week we made an important announcement highlighting the appointment of two new executives at Axiad: Alex Au Yeung as...
CSOs and CFOs; The World’s Next Greatest Dynamic Duo – Source: securityboulevard.com
Source: securityboulevard.com – Author: Scott Kannry One could argue that the World’s greatest conquests, competitions, and challenges are better off when in the hands of a...
XZ Utils-Like Takeover Attempt Targets the OpenJS Foundation – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The OpenJS Foundation, which oversees multiple JavaScript projects, thwarted a takeover attempt of at least one project that has echoes...
USENIX Security ’23 – The Maginot Line: Attacking The Boundary Of DNS Caching Protection – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters: *Xiang Li, Chaoyi Lu, Baojun Liu, Qifan Zhang, Zhou Li, Haixin Duan, Qi Li* Many thanks to USENIX for...
What it takes to do Cloud Detection & Response – Source: securityboulevard.com
Source: securityboulevard.com – Author: James Berthoty A guest post by James Berthoty the founder of Latio Tech. The shift to cloud has meant an explosion in...
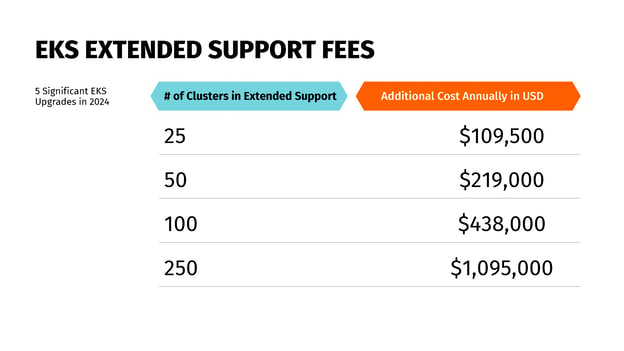
Understanding AWS End of Service Life Is a Key FinOps Responsibility – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mary Henry Amazon Web Services (AWS) announced extended support prices for Amazon Elastic Kubernetes Service (EKS), prompting some businesses to reevaluate how...
Glitter and… Firewalls? How to stay safe this festival season – Source: securityboulevard.com
Source: securityboulevard.com – Author: Avast Blog The air is electric, the skies are clear, and the lineups are out – festival season is upon us! From...
The Unseen Powerhouse: Demystifying Authentication Infrastructure for Tech Leaders – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author In today’s hyper-connected world, authentication is the digital gatekeeper that protects our identities, data, and...
EU Data Regulator Threatens Meta’s ‘Pay or Okay’ Model – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 General Data Protection Regulation (GDPR) , Governance & Risk Management , Privacy The European Data Protection Board Says the Company Inhibits...