Source: www.databreachtoday.com – Author: 1 Training & Security Leadership A Guide to Seizing Opportunities and Pursuing Growth Steve King • April 17, 2024 Image:...
Possible Chinese Hackers Use OpenMetadata to Cryptomine – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cloud Security , Cryptocurrency Fraud , Fraud Management & Cybercrime Hackers Target OpenMetadata Platforms Running on Cloud Kubernetes Environments Prajeet Nair...
Hack on Clinic Serving Homeless Is Latest Hit to Underserved – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific Centers for Underserved Patients, Resource-Poor Communities Fight for Cyber Funds Marianne Kolbasuk...
Armis Buys Cyber Remediation Startup Silk Security for $150M – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Combination of Armis and Silk Will Create Leader in Asset...
Redgate Launches Enterprise Edition of Redgate Monitor – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE CAMBRIDGE, April 17, 2024 – Redgate, the end-to-end Database DevOps provider, has launched an enterprise version of its popular database...
Dangerous ICS Malware Targets Orgs in Russia and Ukraine – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Andrew Angelov via Shutterstock Two dangerous malware tools targeted at industrial control systems (ICS) and operating technology...
Active Kubernetes RCE Attack Relies on Known OpenMetadata Vulns – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading 1 Min Read Source: Sergey Novikov via Alamy Stock Photo Known vulnerabilities in OpenMetadata’s open source...
Ivanti Releases Fixes for More Than 2 Dozen Vulnerabilities – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Alexander Tolstykh via Shutterstock Ivanti has released 27 fixes for various reported vulnerabilities in its...
Various Botnets Pummel Year-Old TP-Link Flaw in IoT Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Stuart Miles via Alamy Stock Photo A number of botnets are pummeling a nearly year-old command-injection vulnerability...
Preparing for Cyber Warfare: 6 Key Lessons From Ukraine – Source: www.darkreading.com
Source: www.darkreading.com – Author: Hadi Shavarini 3 Min Read Source: Aleksei Gorodenkov via Alamy Stock Photo COMMENTARY As the conflict in Ukraine enters its third year,...
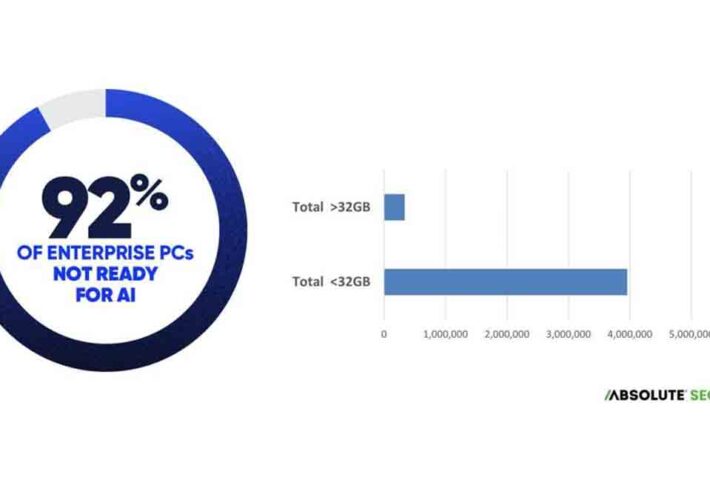
Enterprise Endpoints Aren’t Ready for AI – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 2 Min Read Source: Absolute Security Cyber Resilience Risk Index 2024 Enterprises assessing their readiness for artificial intelligence (AI)...
3 Steps Executives and Boards Should Take to Ensure Cyber Readiness – Source: www.darkreading.com
Source: www.darkreading.com – Author: Chris Crummey Chris Crummey, Director, Executive & Board Cyber Services, Sygnia April 16, 2024 5 Min Read Source: Yee Xin Tan via...
LockBit 3.0 Variant Generates Custom, Self-Propagating Malware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jeffrey Schwartz, Contributing Writer Source: Zoonar Gmbh via Alamy Stock Photo The LockBit ransomware-as-a-service (RaaS) group has struck another victim, this time...
FBI: Smishing Campaign Lures Victims With Unpaid-Toll Notices – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Mira via Alamy Stock Photo The FBI is warning people about widespread SMS phishing (smishing) campaign spreading...
Is a VPN Really Worth It in 2024? – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares Yes, virtual private networks are worth it. In today’s digital age, it’s become increasingly important to protect online data. In...
Conversational Server Access Security
The document titled “Conversational Server Access Security” by Derek A. Smith addresses the evolving landscape of cybersecurity threats, particularly focusing on protecting server access in on-premises...
Using AI-Generated Legislative Amendments as a Delaying Technique – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments echo • April 17, 2024 8:22 AM Ruth Ben-Ghiat has written in her books on fascism that the...
SoumniBot: the new Android banker’s unique techniques – Source: securelist.com
Source: securelist.com – Author: Dmitry Kalinin The creators of widespread malware programs often employ various tools that hinder code detection and analysis, and Android malware is...
CSI Cloud Top10 Key Management
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Defining the Zero TrustProtect Surface
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CONTAINER SECURITY INTERVIEW QUESTIONS ANSWERS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
PRACTICE GUIDE GDPR – SECURITY OF PERSONAL DATA Version 2024
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cloud Security Engineer Roadmap
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CYBER SECURITY REPORT – 2024
The Security Report 2024 by Check Point Software provides a comprehensive analysis of global cyber security trends and threats. It emphasizes the importance of learning from...
Cloud Computing Tutorial Simply Easy Learning
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CYBERSECURITY GUIDE FOR BOARDROOM MEMBERS
The Cybersecurity Guide for Boardroom Members emphasizes the importance of cybersecurity in organizations. It highlights the roles of the Data Protection Officer (DPO) in ensuring GDPR...
Why a Native-First Approach Is Key to Cloud Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security 3 Min Read Source: Rasi Bhadramani via Alamy Stock Photo As companies increasingly migrate to public cloud platforms like Microsoft...
‘Sandworm’ Group Is Russia’s Primary Cyberattack Unit in Ukraine – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Militarist via Shutterstock The formidable Sandworm hacker group has played a central role supporting Russian military objectives...
Israeli Defense Forces Hold Hybrid Cyber & Military Readiness Drills – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Ruma Aktar via Alamy Stock Photo Adding fuel to speculation that Israel may wage strategic...
Delinea Fixes Flaw, but Only After Analyst Goes Public With Disclosure First – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading Source: Phichak via Alamy Stock Photo A critical flaw in Delinea’s Secret Server SOAP API disclosed...