Source: www.cyberdefensemagazine.com – Author: News team Software supply chain attacks have emerged as a serious threat in the rapidly evolving field of cybersecurity, especially in medical...
Author: CISO2CISO Editor 2
Ransomware Tactics Are Shifting. Here’s How to Keep Up – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team It’s common knowledge in the cybersecurity industry that ransomware is on the rise, with median demands rising 20% year-over-year across...
French Advisory Sheds Light on Apple Spyware Activity – Source: www.darkreading.com
Source: www.darkreading.com – Author: Rob Wright CERT-FR’s advisory follows last month’s disclosure of a zero-day flaw Apple said was used in “sophisticated” attacks against targeted individuals....
Without Federal Help, Cyber Defense Is Up to the Rest of Us – Source: www.darkreading.com
Source: www.darkreading.com – Author: Riaz Lakhani Together, we can foster a culture of collaboration and vigilance, ensuring that we are not just waiting for a hero...
Safer Conversational AI for Cybersecurity: The BIX Approach – Source: securityboulevard.com
Source: securityboulevard.com – Author: Gaurav Banga Here’s a scenario security teams increasingly face. A user—or an attacker pretending to be one—types something like: This is how...
Operation Eastwood: Measuring the Real Impact on NoName057(16) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Sofia Naer Introduction On July 16, 2025, Europol revealed the details of Operation Eastwood, a coordinated international strike against one of the...
CISA Lays Out Roadmap for CVE Program’s ‘Quality Era’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Five months after the future of the CVE program was thrown in doubt, CISA this week released a roadmap that...
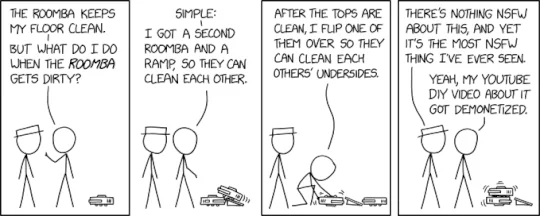
Randall Munroe’s XKCD ‘Dual Roomba’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic artistry and dry wit of Randall Munroe, creator of XKCD Permalink The post Randall Munroe’s XKCD ‘Dual...
In Other News: $900k for XSS Bugs, HybridPetya Malware, Burger King Censors Research – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News SecurityWeek’s cybersecurity news roundup provides a concise compilation of noteworthy stories that might have slipped under the radar. We provide...
VoidProxy phishing-as-a-service operation steals Microsoft, Google login credentials – Source: www.csoonline.com
Source: www.csoonline.com – Author: Service can get around cloud single-sign-on providers, warns Okta. Identity and access management provider Okta has discovered what it says is a...
VMScape Spectre BTI attack breaks VM isolation on AMD and Intel CPUs – Source: www.csoonline.com
Source: www.csoonline.com – Author: The Spectre-like CPU branch target injection (BTI) breaks the guest-host layer in virtualized environments, introducing a new threat to data centers and...
How Wesco cut through the noise and reimagined risk management – Source: www.csoonline.com
Source: www.csoonline.com – Author: by Shane O’Neill for CSO Events Feature Sep 12, 20256 mins The supply chain solutions provider used data consolidation and AI to...
2025 CSO Hall of Fame: Laura Deaner on AI, quantum threats, and cyber leadership – Source: www.csoonline.com
Source: www.csoonline.com – Author: Today’s security leaders should focus on continuous learning and strengthening defenses against evolving cyber threats. Laura Deaner, recently appointed chief information security...
Stealthy AsyncRAT flees the disk for a fileless infection – Source: www.csoonline.com
Source: www.csoonline.com – Author: Attackers are abusing legitimate remote access tools and lightweight scripts to deliver AsyncRAT entirely in memory, bypassing file-based detection. Security researchers have...
Why domain-based attacks will continue to wreak havoc – Source: www.csoonline.com
Source: www.csoonline.com – Author: Hackers are using AI to supercharge domain-based attacks, and most companies aren’t nearly ready to keep up. Among the numerous cyber threats...
12 digital forensics certifications to accelerate your cyber career – Source: www.csoonline.com
Source: www.csoonline.com – Author: As cyberattacks grow more complex, digital forensics certs can equip professionals with the skills and credibility to investigate breaches and prevent them...
Fünf KI-Use-Cases für CISOs – Source: www.csoonline.com
Source: www.csoonline.com – Author: Künstliche Intelligenz kommt auch in den IT-Sicherheitsteams an. Diese Anwendungsfälle werden gerade erprobt. Rob Hyrons / Shutterstock Security-Verantwortliche haben zwei Hauptaufgaben, wenn...
So rechtfertigen Sie Ihre Security-Investitionen – Source: www.csoonline.com
Source: www.csoonline.com – Author: Budget-Diskussionen sind lästig, denn Cyberrisiken und Ausgaben steigen gleichermaßen. CISOs sollten daher ihre Argumentation auf Unternehmensziele ausrichten. Lesen Sie, welche Aspekte entscheidend...
Ransomware gang going after improperly patched SonicWall firewalls – Source: www.csoonline.com
Source: www.csoonline.com – Author: Changing admin password after installing 2024 patch is vital, experts warn. Vulnerable SonicWall firewalls that should have been patched a year ago...
Attackers Adopting Novel LOTL Techniques to Evade Detection – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: Threat actors are using novel living-off-the-land (LOTL) tactics to better evade detection, according to HP Wolf’s Q2 2025 Threat Insights Report. These...
Microsoft’s Patch Tuesday: About 80 Vulnerabilities Patched – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse Image: Envato/seventyfourimages Microsoft released its latest monthly security patch on Sept. 9, addressing approximately 80 CVEs. September was a relatively...
British rail passengers urged to stay on guard after hack signals failure – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley Passengers of the UK’s state-owned London North Eastern Railway (LNER) have been warned to be vigilant after cybercriminals accessed traveller’s...
Smashing Security podcast #434: Whopper Hackers, and AI Whoppers – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Skip to content Ever wondered what would happen if Burger King left the keys to the kingdom lying around for...
Undocumented Radios Found in Solar-Powered Devices – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Michael Vi via Shutterstock The latest supply chain cyber threat could be sitting on the side of...
Vyro AI Leak Reveals Poor Cyber Hygiene – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek The data leak underscores the larger issue of proprietary or sensitive data being shared with GenAI by users who should...
‘Gentlemen’ Ransomware Abuses Vulnerable Driver to Kill Security Gear – Source: www.darkreading.com
Source: www.darkreading.com – Author: Rob Wright By weaponizing the ThrottleStop.sys driver, attackers are disrupting antivirus and endpoint detection and response (EDR) systems. Original Post URL: https://www.darkreading.com/vulnerabilities-threats/gentlemen-ransomware-vulnerable-driver-security-gear...
Apple CarPlay RCE Exploit Left Unaddressed in Most Cars – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Even when a vulnerability is serious and a fix is available, actually securing cars is more difficult than...
F5 to Acquire CalypsoAI for Advanced AI Security Capabilities – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek F5 plans to use CalypsoAI’s platform to provide real-time threat defense against attacks and help enterprises safeguard themselves as they...
AI-Enhanced Malware Sports Super-Stealthy Tactics – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Lightspring via Shutterstock A threat actor is using legit-looking AI tools and software to sneak malware for...
Cyberattack on Kazakhstan’s Largest Oil Company Was ‘Simulation’ – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Researchers thought a Russian APT used a compromised employee email to attack Kazakhstan’s biggest oil company. The company...