Source: www.darkreading.com – Author: Peter Klimek, Director of Technology, Office of the CTO, Imperva According to the latest report from the Identity Theft Research Center, there...
Author: admin
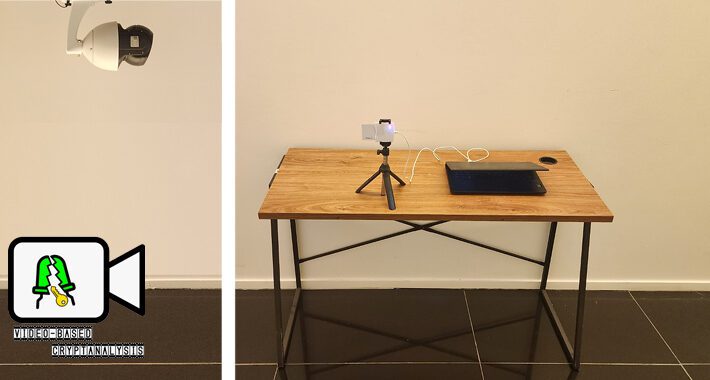
Researchers Find Way to Recover Cryptographic Keys by Analyzing LED Flickers – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 26, 2023Ravie LakshmananCryptography / Cybersecurity In what’s an ingenious side-channel attack, a group of academics has found that it’s possible...
Japanese Cryptocurrency Exchange Falls Victim to JokerSpy macOS Backdoor Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 26, 2023Ravie LakshmananCryptocurrency / Endpoint Security An unknown cryptocurrency exchange located in Japan was the target of a new attack...
Critical flaw in VMware Aria Operations for Networks sees mass exploitation – Source: www.csoonline.com
Source: www.csoonline.com – Author: Akamai reports nearly 700,000 attacks with 27,000 of its customers being scanned for the vulnerability. Researchers warn that a vulnerability patched this...
Latest MOVEit exploit hits thousands of NYC school students and staff – Source: www.csoonline.com
Source: www.csoonline.com – Author: The exploit granted unauthorized access to critical student and staff information, affecting 45,000 students and 19,000 documents. Personal data of over 45,000...
BrandPost: Enhancing cloud infrastructure security via infrastructure as code – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | When you have comprehensive security, the future is yours to build. Learn about the strategies and solutions to secure your...
BrandPost: Cybersecurity recommendations—strengthening the government posture and engagement – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | Synopsys provides integrated solutions that transform the way development teams build and deliver software, accelerating innovation while addressing business risk....
BrandPost: What is the key to optimized DevSecOps? – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | Synopsys provides integrated solutions that transform the way development teams build and deliver software, accelerating innovation while addressing business risk....
BrandPost: The light and dark of artificial intelligence – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | Synopsys provides integrated solutions that transform the way development teams build and deliver software, accelerating innovation while addressing business risk....
Pilot data of American Airlines and Southwest stolen in data breach – Source: www.csoonline.com
Source: www.csoonline.com – Author: Personal information of 5,745 pilots of American Airlines and 3,009 pilots from Southwest Airlines has been leaked due to the incident. SoutherlyCourse...
The CISO’s toolkit must include political capital within the C-suite – Source: www.csoonline.com
Source: www.csoonline.com – Author: Effective CISOs need to clearly articulate risk and mitigation strategies in business. They must be clear, precise, and, above all, speak truth...
BrandPost: Cisco Secure Access: secure connectivity from anything to anywhere from everywhere – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | Security resilience for the unpredictable to connect and protect every part of your business. Withstand the unforeseen and emerge stronger...
How Generative AI Can Dupe SaaS Authentication Protocols — And Effective Ways To Prevent Other Key AI Risks in SaaS – Source:thehackernews.com
Source: thehackernews.com – Author: . Security and IT teams are routinely forced to adopt software before fully understanding the security risks. And AI tools are no...
Microsoft Warns of Widescale Credential Stealing Attacks by Russian Hackers – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 26, 2023Ravie LakshmananCyber Threat / Password Security Microsoft has disclosed that it’s detected a spike in credential-stealing attacks conducted by...
Chinese Hackers Using Never-Before-Seen Tactics for Critical Infrastructure Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 26, 2023Ravie LakshmananCyber Espionage / LotL The newly discovered Chinese nation-state actor known as Volt Typhoon has been observed to...
Malware Analisys 101 – created by ChatGPT in 20 minutes
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Avoid The Hack: 3 Best Privacy Browsers Picks for iOS – Source: securityboulevard.com
Source: securityboulevard.com – Author: Avoid The Hack! This post was originally published on 2 APR 2021; it has since been updated and revised. Unfortunately, it’s difficult...
Avoid The Hack: 3 Best Privacy Browser Picks for Android – Source: securityboulevard.com
Source: securityboulevard.com – Author: Avoid The Hack! This post was originally published on 14 APR 2021; it has since been updated and revised. Most Android phones...
Cloud Cybersecurity Market Analysis by Enisa – European Union Agency for Cybersecurity
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Operations & Incident Management Knowledge Area by Herve Debar – Telecom SudParis
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
U.S. Cybersecurity Agency Adds 6 Flaws to Known Exploited Vulnerabilities Catalog – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 24, 2023Ravie LakshmananThreat Intel / Zero Day The U.S. Cybersecurity and Infrastructure Security Agency has added a batch of six...
Twitter Hacker Sentenced to 5 Years in Prison for $120,000 Crypto Scam – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 24, 2023Ravie LakshmananCyber Crime / Cryptocurrency A U.K. citizen who took part in the massive July 2020 hack of Twitter...
ITDR Combines and Refines Familiar Cybersecurity Approaches – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jonathan Care, Contributing Writer, Dark Reading The advantages of using proactive approaches to identify threats before the attackers can cause too much...
NSA: BlackLotus BootKit Patching Won’t Prevent Compromise – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading The US National Security Agency (NSA) is urging systems administrators to go beyond patching in...
Suspicious Smartwatches Mailed to US Army Personnel – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The US Army’s Criminal Investigation Division (CID) is warning service members to look out for unsolicited smartwatches arriving in...
Microsoft Teams Attack Skips the Phish to Deliver Malware Directly – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A bug in the latest version of Microsoft Teams allows for external sources to send files to...
Why Legacy System Users Prioritize Uptime Over Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Evan Schuman, Contributing Writer, Dark Reading Dirk Hodgson, the director of cybersecurity for NTT Australia, tells a story. He once worked with...
Millions of Repos on GitHub Are Potentially Vulnerable to Hijacking – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Millions of enterprise software repositories on GitHub are vulnerable to repojacking, a relatively simple kind of...
Deception Technologies Have a Maturity Problem – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading INFOSEC23 — London — Deception technologies can offer a better method to detect attackers in your...
Public exploit is now available for Cisco AnyConnect VPN client – Source: www.csoonline.com
Source: www.csoonline.com – Author: Attackers could elevate privileges on systems with the vulnerable, unpatched Cisco clients, possibly taking full control. An easy-to-use exploit was publicly released...