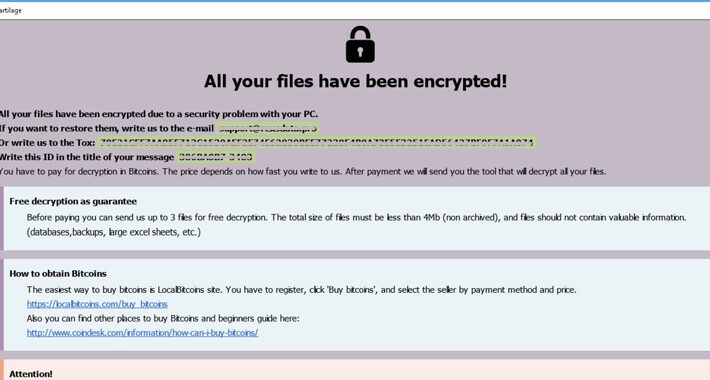
Source: thehackernews.com – Author: . Jun 28, 2023Ravie LakshmananRansomware / Cyber Threat A ransomware threat called 8Base that has been operating under the radar for over...
Author: admin
Critical SQL Injection Flaws Expose Gentoo Soko to Remote Code Execution – Source:thehackernews.com
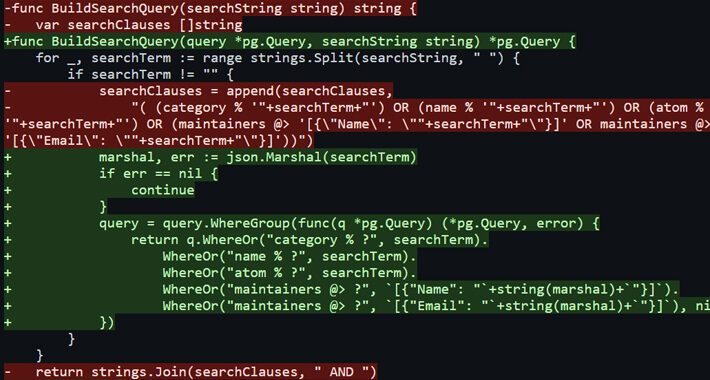
Source: thehackernews.com – Author: . Jun 28, 2023Ravie LakshmananEndpoint Security / RCE Multiple SQL injection vulnerabilities have been disclosed in Gentoo Soko that could lead to...
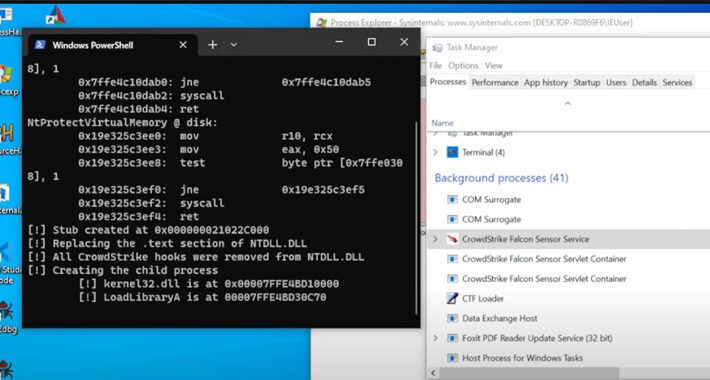
New Mockingjay Process Injection Technique Could Let Malware Evade Detection – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 27, 2023Ravie LakshmananMalware / Cyber Threat A new process injection technique dubbed Mockingjay could be exploited by threat actors to...
New Ongoing Campaign Targets npm Ecosystem with Unique Execution Chain – Source:thehackernews.com
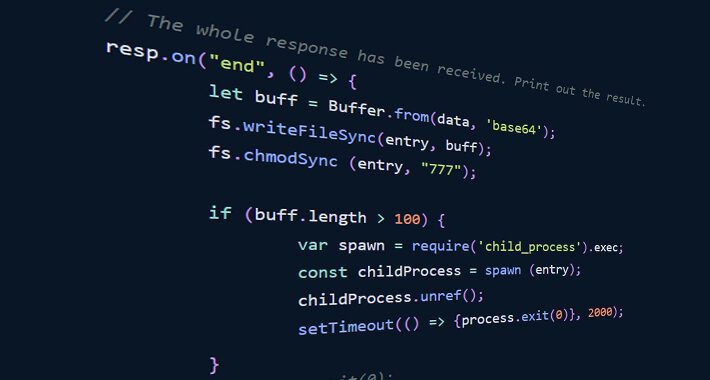
Source: thehackernews.com – Author: . Jun 27, 2023Ravie LakshmananSupply Chain / Software Security Cybersecurity researchers have discovered a new ongoing campaign aimed at the npm ecosystem...
UCLA, Siemens Among Latest Victims of Relentless MOVEit Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Schneider Electric; Siemens Energy; the University of California, Los Angeles (UCLA); Werum, a pharmaceutical technology provider; and...
Mockingjay Slips By EDR Tools With Process Injection Technique – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Endpoint detection and response (EDR) systems have become increasingly efficient at detecting typical process injection attempts...
Trans-Rights Hacktivists Steal City of Ft. Worth’s Data – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading In a security breach first discovered on June 23, Fort Worth, a north Texas city that has more...
Pilot Applicant Information for American, Southwest Hacked – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Hackers breached a database maintained by Pilot Credentials, a recruiting company based in Austin, Texas, resulting...
Most Enterprise SIEMs Blind to MITRE ATT&CK Tactics – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Despite enterprises’ best efforts to shore up their security information and event management (SIEM) postures, most platform...
Why Cyber Funding Flows for Rural Water Systems – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading A recent bill that proposes $7.5 million in annual cybersecurity funding for the next five years...
SEC notice to SolarWinds CISO and CFO roils cybersecurity industry – Source: www.csoonline.com
Source: www.csoonline.com – Author: US SEC staff have recommended legal action against individual SolarWinds employees, in an unusual move that is causing a stir among cybersecurity...
Fortanix adds confidential data search for encrypted enterprise data – Source: www.csoonline.com
Source: www.csoonline.com – Author: Fortanix Confidential Data Search supports scalable searches in encrypted databases with sensitive data, without compromising data security or privacy regulations. Cloud data...
Bionic integrations offer context-based vulnerability management – Source: www.csoonline.com
Source: www.csoonline.com – Author: Bionic Signals and Bionic Business Risk Scores are being added to Bionic’s Application security posture management platform for context-based risk prioritization. Application...
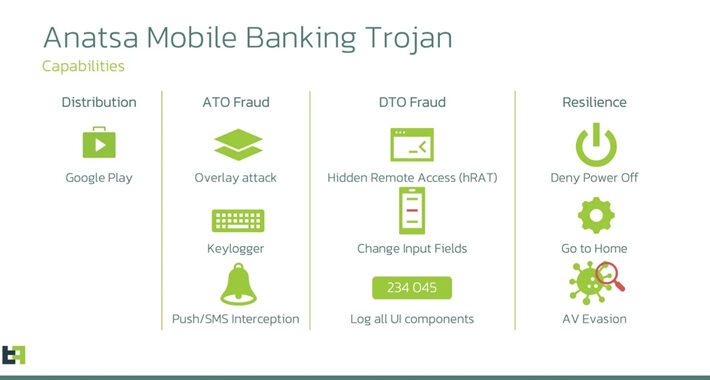
New Android banking trojan targets US, UK, and Germany – Source: www.csoonline.com
Source: www.csoonline.com – Author: The threat actors are distributing their malware via the Play Store, and already had over 30,000 installations as of March. An ongoing...
Fileless attacks surge as cybercriminals evade cloud security defenses – Source: www.csoonline.com
Source: www.csoonline.com – Author: Threat actors are concealing campaigns to evade detection and establish stronger footholds in compromised systems. Irga-igra / ConnectVector / Shutterstock The number...
Survey reveals mass concern over generative AI security risks – Source: www.csoonline.com
Source: www.csoonline.com – Author: Malwarebytes survey reveals 81% of people are concerned about the security risks posed by ChatGPT and generative AI, while just 7% think...
BrandPost: Effective security training programs are vital to creating a cyber-aware workforce – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | CISOs today face an expanding attack surface, increasingly threats, and a cybersecurity skills gap. An integrated and automated approach to...
258% ROI with Contrast Security solutions |IDC Business Value Case Study – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lisa Vaas, Senior Content Marketing Manager, Contrast Security Floor & Decor — the hard-surface flooring retailer based in Smyrna, Georgia that has...
Beyond Asset Discovery: How Attack Surface Management Prioritizes Vulnerability Remediation – Source:thehackernews.com
Source: thehackernews.com – Author: . As the business environment becomes increasingly connected, organizations’ attack surfaces continue to expand, making it challenging to map and secure both...
EncroChat Bust Leads to 6,558 Criminals’ Arrests and €900 Million Seizure – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 27, 2023Ravie Lakshmanan Europol on Tuesday announced that the takedown of EncroChat in July 2020 led to 6,558 arrests worldwide...
Anatsa Banking Trojan Targeting Users in US, UK, Germany, Austria, and Switzerland – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 27, 2023Ravie LakshmananMobile Security / Malware A new Android malware campaign has been observed pushing the Anatsa banking trojan to...
New Fortinet’s FortiNAC Vulnerability Exposes Networks to Code Execution Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 27, 2023Ravie LakshmananVulnerability / Exploit Fortinet has rolled out updates to address a critical security vulnerability impacting its FortiNAC network...
SolarWinds Execs Targeted by SEC, CEO Vows to Fight – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading The Security and Exchange Commission (SEC) has issued a notice to SolarWinds executives that it intends to...
China’s ‘Volt Typhoon’ APT Turns to Zoho ManageEngine for Fresh Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading The recently discovered Chinese state-backed advanced persistent threat (APT) “Volt Typhoon,” aka “Vanguard Panda,” has been...
Twitter Celeb Account Hacker Heads to Jail for 5 Years – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading A main conspirator in the infamous 2020 celebrity Twitter account takeovers is off to jail for five...
It’s Open Season on Law Firms for Ransomware & Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading An increasing rash of ransomware attacks on law firms prompted the UK’s National Cyber Security Centre to...
Cl0p in Your Network? Here’s How to Find Out – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Widespread attacks against companies and government agencies through a trio of zero-day vulnerabilities in the MOVEit...
Remediation Ballet Is a Pas de Deux of Patch and Performance – Source: www.darkreading.com
Source: www.darkreading.com – Author: Michael Bargury, CTO & Co-Founder, Zenity Recent advancements in artificial intelligence (AI) have rekindled the spirit of fully automated vulnerability remediation. The...
How Infrastructure as Code Can Help Minimize Human Error – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security, Microsoft When it comes to cybersecurity, human error is one of the biggest risk factors that security teams have to...
Trojanized Super Mario Installer Goes After Gamer Data – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Attackers have turned a legitimate installer for a popular Super Mario Bros game into a Trojan that...