The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Month: November 2023
SIEM use case – 45 use cases for Security Monitoring
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Shrouded Snooper Analysis Report
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Senteon to CIS Product Mapping: Controls v8
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security the Grid – Cybersecurity Report in the Electricity Sector 2020
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SQL Injection Attacks and Defense
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
State of Cyber Threat Intelligence 2023
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
State of Cybersecurity 2023Global Update on Workforce Efforts, Resourcesand Cyberoperations
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
swift iso 20022 for dummies 6th edition
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
State of Segmentation Strong Implementations Reap Great Security Rewards
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Third Party Security Requirements
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Russian hybrid threat toolbox
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Importance ofTwo-FactorAuthentication (2FA) Protecting Your Digital World
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Cost of Cyber Defense – CIS Controls Implementation Group 1
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Art of Recognizingand Surviving SOC Burnout
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The 2023 Cybersecurity Report by Solve
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cloud Security Alliance – Zero Trust Guiding Principles PD
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CISSP Study GuideCERTIFICATION TRAINING
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
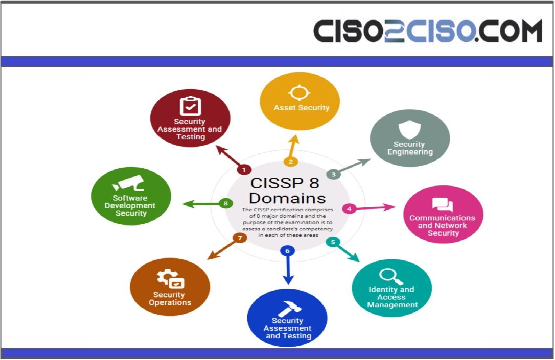
CISSPP 8 Domains
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CISO PLAYBOOK:F I R S T1 0 0D A Y SSetting the CISO up for success
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CIS Controls Cost of Cyber Defense
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CISA Open Source SoftwareSecurity Roadmap
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
North Korea’s BlueNoroff APT Debuts ‘Dumbed Down’ macOS Malware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading North Korean state hackers have debuted a fresh Mac malware targeting users in the US and...
Programming, Self-Learning Crucial for Autonomous Operations – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Endpoint Security , Governance & Risk Management , Internet of Things Security Success Hinges on Marrying Programmed Task and Information From...
CONTINUOUS DIAGNOSTICS AND MITIGATION PROGRAM – Identity, Credential, and Access Management (ICAM) Reference Architecture
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Bug Bounty Funshop
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Bloodhound Active Directory Enumeration Tool
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Blockchain Security A Framework for Trust and Adoption
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Best Cybersecurity Certifications online
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Azure DevOps Security Guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...