Source: heimdalsecurity.com – Author: Alina Georgiana Petcu A clear DNS cache is an easy way to solve connectivity issues, as well as prevent some of the...
San Bernardino County Sheriff’s Department paid a $1.1M ransom – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The San Bernardino County Sheriff’s Department confirmed that it has paid a $1.1-million ransom after the April ransomware attack. The...
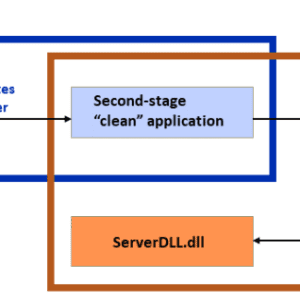
Dragon Breath APT uses double-dip DLL sideloading strategy – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini An APT group tracked as Dragon Breath has been observed employing a new DLL sideloading technique. Sophos researchers observed an APT group,...
USENIX Enigma 2023 – Marcus Botacin – ‘Why Is Our Security Research Failing? Five Practices to Change!’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Securing the Grid: How Balbix Transformed a US Utility Company’s Cybersecurity Posture – Source: securityboulevard.com
Source: securityboulevard.com – Author: Shreekanth Veeranagowdra Electric utility companies around the world are progressively adopting smart grid technologies to enhance their operations. As these advanced systems...
Cloud, Workforce, Cyber and AI: NASCIO Midyear 2023 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lohrmann on Cybersecurity The National Association of State Chief Information Officers held their 2023 Midyear Conference in National Harbor, Md., this past...
2023 Predictions – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Anurag Gurtu, Chief Product Officer at Strike Ready In 2022, the global average total breach cost surpassed $4.35M, and...
Strengths and Vulnerabilities of AI Applications to Health Care – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team By Edward Maule, Chief Information Officer and Chief Information Security Officer at Advocare, LLC Artificial intelligence (AI) has made significant...
New Cactus ransomware encrypts itself to evade antivirus – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ionut Ilascu A new ransomware operation called Cactus has been exploiting vulnerabilities in VPN appliances for initial access to networks of “large...
Western Digital says hackers stole customer data in March cyberattack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Western Digital has taken its store offline and sent customers data breach notifications after confirming that hackers stole sensitive personal...
New CS:GO map bypasses Russia’s censorship of Ukraine war news – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Finish newspaper Helsinin Sanomat has created a custom Counter-Strike: Global Offensive (CS:GO) map explicitly made to bypass Russian news censorship...
Meet Akira — A new ransomware operation targeting the enterprise – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams The new Akira ransomware operation has slowly been building a list of victims as they breach corporate networks worldwide, encrypt...
Twitter admits to ‘security incident’ involving Circles tweets – Source: www.theguardian.com
Source: www.theguardian.com – Author: Alex Hern UK technology editor A privacy breach at Twitter published tweets that were never supposed to be seen by anyone but...
Security Affairs newsletter Round 418 by Pierluigi Paganini – International edition – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Privacy Overview This website uses cookies to improve your experience while you navigate through the website. Out of these cookies,...
Twitter confirmed that a security incident publicly exposed Circle tweets – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A security problem caused the public sharing of private tweets sent to Twitter Circles to users outside of the Circle,...
FBI seized other domains used by the shadow eBook library Z-Library – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The FBI disrupted once again the illegal eBook library Z-Library the authorities seized several domains used by the service. The...
WordPress Advanced Custom Fields plugin XSS exposes +2M sites to attacks – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A reflected cross-site scripting vulnerability is the Advanced Custom Fields plugin for WordPress exposed over 2 million sites to hacking....
Friday Squid Blogging: “Mediterranean Beef Squid” Hoax – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Friday Squid Blogging: “Mediterranean Beef Squid” Hoax The viral video of the “Mediterranean beef squid”is a hoax. It’s not...
USENIX Enigma 2023 – Justin Brookman – ‘What Public Interest AI Auditors Can Learn From Security Testing: Legislative And Practical Wins’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Safeguarding Data Centers Against Growing Cyber Threats – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rajan Sodhi As we continue to rely on digital technology to store and process vast amounts of data, the need for robust...
Investigating Undocumented Netcomms From Legitimate Chrome Extension – Source: securityboulevard.com
Source: securityboulevard.com – Author: IronNet Hot Topics USENIX Enigma 2023 – Justin Brookman – ‘What Public Interest AI Auditors Can Learn From Security Testing: Legislative And...
Threat Spotlight: The New Dark Web? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Yuzuka Akasaka Executive Overview Illicit Telegram channels have become a growing concern in the realm of cybercrime. Threat actors want to connect...
The Typology of Illicit Telegram Channels – Source: securityboulevard.com
Source: securityboulevard.com – Author: Research Team Cybercriminals seem to always be looking for new and innovative ways to commit their crimes more efficiently. In the past,...
Zero Trust Implementation for Government Agencies Starts with Cultural Change – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 The U.S. government’s zero trust mandate is driving the public sector to adopt a new cybersecurity mindset of “trusting no one.”...
Boards Are Having the Wrong Conversations About Cybersecurity – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Headlines increasingly highlight the consequences of poor cybersecurity practices. Board members with cybersecurity experience are trying to get their fellow members’...
KnowBe4 Launches Password Kit to Celebrate World Password Day – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 TAMPA BAY, Fla., May 4, 2023 /PRNewswire/ — KnowBe4, the provider of the world’s largest security awareness training and simulated phishing platform, today...
Satori Unveils Universal Data Permissions Scanner, A Free Open-Source Tool that Sheds Light on Data Access Authorization – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 Sunnyvale, CA — May 4, 2023 — Satori, the industry’s leading data security platform, today announced the release of its Universal...
Microsoft Digital Defense Report: Key Cybercrime Trends – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security, Microsoft Microsoft has been releasing in-depth security reports for more than 15 years as a way to highlight emerging trends...
New Generative AI Tools Aim to Improve Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jeffrey Schwartz, Contributing Writer, Dark Reading Generative AI technologies, such as OpenAI’s ChatGPT, have the potential to help security professionals defend against...
Hotels at Risk From Bug in Oracle Property Management Software – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading The thousands of hotels and other entities in the hospitality industry worldwide using Oracle’s Opera property...