Source: securityaffairs.com – Author: Pierluigi Paganini The ransomware gang behind the attack on Taiwanese PC maker MSI leaked the company’s private code signing keys on their...
NextGen Healthcare suffered a data breach that impacted +1 Million individuals – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini NextGen Healthcare suffered a data breach, the security incident exposed the personal information of approximately 1 million individuals. Healthcare solutions...
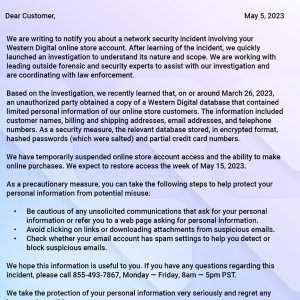
Western Digital notifies customers of data breach after March cyberattack – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Western Digital is notifying its customers of a data breach that exposed their sensitive personal information, the incident took place...
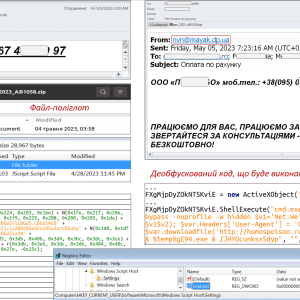
CERT-UA warns of an ongoing SmokeLoader campaign – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Ukraine’s CERT-UA warns of an ongoing phishing campaign aimed at distributing the SmokeLoader malware in the form of a polyglot...
SEC issued a record award of $279 million to a whistleblower – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The Securities and Exchange Commission (SEC) announced the largest-ever award, approximately $279 million, to a whistleblower. The Securities and Exchange...
Uber’s ex-CSO avoids prison after data breach cover up – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley After covering up a data breach that impacted the personal records of 57 million Uber passengers and drivers, the company’s...
Google Releases Open Source Bazel Plugin for Container Image Security – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Google last week announced the general availability of ‘rules_oci’, an open source Bazel plugin for building container images. Bazel improves...
Ransomware Group Claims Attack on Constellation Software – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The Alphv/BlackCat ransomware group has claimed responsibility for a cyberattack that Canadian software company Constellation Software disclosed last week. Toronto-based...
Vulnerability in Field Builder Plugin Exposes Over 2M WordPress Sites to Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A cross-site scripting (XSS) vulnerability in the Advanced Custom Fields WordPress plugin could be exploited to inject malicious scripts into...
Private Tweets Exposed Due to Twitter Circle Security Bug – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Twitter is informing users that tweets posted to their Circle, which should have only been seen by specified individuals, may...
1 Million Impacted by Data Breach at NextGen Healthcare – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Healthcare solutions provider NextGen Healthcare has started informing roughly one million individuals that their personal information was compromised in a...
$1.1M Paid to Resolve Ransomware Attack on California County – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press A $1.1 million payment was made to resolve a ransomware attack on a California county’s law enforcement computer network, Southern...
Western Digital Confirms Ransomware Group Stole Customer Information – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Western Digital confirmed on Friday that cybercriminals have stolen customer and other information after breaching its systems. According to the...
Data Sovereignty: Definition, Requirements and How to Ensure It – Source: securityboulevard.com
Source: securityboulevard.com – Author: Spanning Cloud Apps Massive amounts of data are generated globally every second, making their wrongful use and distribution across the digital landscape...
USENIX Enigma 2023 – Shanna Devine, Office of Whistleblower Ombuds in the U.S. House of Representatives – Protecting Whistleblower Information’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
How to go about building a SAST plan for your company? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Cloudanix Author SAST stands for Static Application Security Testing, and it refers to the process of analyzing the source code of an...
Randall Munroe’s XKCD ‘Commemorative Plaque’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Knives Out for TikTok as Journo Reveals her Spy Story – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings FT’s Criddle claims ByteDance spied on her—because she wrote damaging stories about TikTok. A technology reporter says she was “surveilled”...
USENIX Enigma 2023 – Dominik Wermke – ‘Understanding Trust And Security Processes In The Open Source Software Ecosystem’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
GitGuardian at AppSec Village: Honeytokens for the blue team – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dwayne McDaniel You might have already heard that GitGuardian went to RSA Conference 2023. Aside from all the excitement of the sessions,...
CRN’s 2023 Women of the Channel Honors Lauren Wolff of Menlo Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Menlo Security MOUNTAIN VIEW, Calif., May 8, 2023 —Menlo Security, Inc. (“Menlo Security”), a leading cloud security company, announced today that CRN®,...
Decentralized Identity: Gaining Security and Trust for Digital Identities – Source: securityboulevard.com
Source: securityboulevard.com – Author: Daniel Schwartzer Our modern digital world has proven that the current way of managing identity in cyberspace needs to change. If your...
Privoro-Samsung partnership provides trusted control over smartphone radios and sensors – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mike Fong and Todd Maxwell We’re excited to share that Privoro and Samsung have partnered to provide a powerful new security capability:...
Hackers Leak Private Keys; Many MSI Products at Risk – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Breach Notification , Fraud Management & Cybercrime , Ransomware Leak Includes Intel Boot Guard and OEM Image Signing Keys for Over...
LockBit 3.0 Leaks 600 GBs of Data Stolen From Indian Lender – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Geo Focus: Asia , Geo-Specific Data Leak Comes After Fullerton India Refused to Negotiate With Ransomware...
Fleckpe Trojan Infects 620K Devices Via Google Play – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Mobile Payments Fraud Now-Removed Apps Have 620K Downloads, Targeting Victims in Thailand Prajeet Nair...
Feds Slap Another Provider with ‘Right of Access’ Fine – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , HIPAA/HITECH , Privacy $15,000 Settlement With Psychotherapy Counselor Is HHS OCR’s 44th Case Marianne Kolbasuk McGee...
How to secure your Mac’s data via Full Disk Access settings – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Erik Eckel Learn one of the most effective ways to secure your Mac’s data within seconds. Image: Farknot Architect/Adobe Stock This common...
Twitter Confirms a “Security Incident” that Led to Exposing Private Circle Tweets – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Andreea Chebac Twitter recognized a security error regarding Twitter Circles in a statement sent to affected users on 5 May 2023. The...
A New Ransomware Operation Threatens Your Business: Akira – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Andreea Chebac Researchers spotted a new ransomware operation in March 2023. It is called Akira and targets businesses worldwide, breaching corporate networks,...