Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Browser companies and network-security vendors have created a variety of defenses for the three-decades-old attack technique...
Microsoft Digital Defense Report: Nation-State Threats and Cyber Mercenaries – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security, Microsoft Every year, Microsoft releases the “Microsoft Digital Defense Report” as a way to illuminate the evolving digital threat landscape...
Google Chrome 3rd Party Cookies Crumbling — Finally! – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings Privacy Sandbox inching towards reality. But concerns remain. Google’s plan to kill the third party cookie is moving forward. Remember...
9 Key Takeaways from a Platform Team’s Panel Discussion on Kubernetes – Source: securityboulevard.com
Source: securityboulevard.com – Author: Danielle Cook If you’re thinking about building a Kubernetes platform that your developers can use to build applications, you need to know...
BSidesSF 2023 – Breanne Boland, Amy Martin – No Adversaries: Getting Users On Your Side For Tough Transformations – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/05/bsidessf-2023-breanne-boland-amy-martin-no-adversaries-getting-users-on-your-side-for-tough-transformations/ Category & Tags: Security Bloggers Network,appsec education,BsidesSF,BSidesSF...
Delivering World-Class CIAM: The Product Management Journey at LoginRadius – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author As businesses continue to evolve in the digital era, it is becoming increasingly important to...
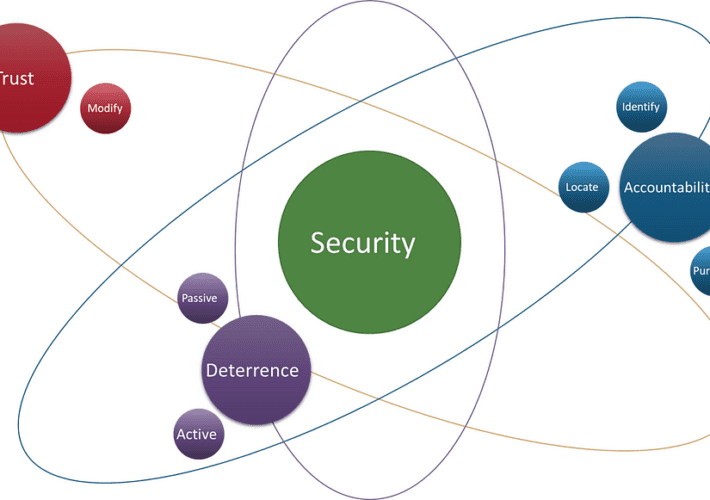
Security Distilled: Building a First-Principles Approach to Understanding Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nathan D. By Nathan Davis This body of work also appears in the form of a webinar, which can be accessed here. What is...
Guarding the Gates: The Intricacies of Detection Engineering and Threat Hunting – Source: securityboulevard.com
Source: securityboulevard.com – Author: Cyborg Security In the ever-evolving landscape of cybersecurity, two disciplines stand out: Detection Engineering and Threat Hunting. While they share common objectives...
Learnings from the IDC South Africa CIO Summit 2023 #IDSACIO – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lalit Shinde My colleagues and our partners attended the annual IDC South Africa CIO Summit 2023 on May 18, 2023 in Johannesburg....
Complete Guide to Elastic SIEM – Source: securityboulevard.com
Source: securityboulevard.com – Author: Gilad David Maayan Elastic Security, which includes Elastic security information and event management (SIEM), is a comprehensive security solution developed by Elastic....
cdCon + GitOpsCon – Co-evolving Open Source DevOps Communities In One Conference – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dwayne McDaniel On the west coast of Canada, you will find Vancouver, British Columbia, home to the Canucks, breathtaking scenery, and the...
Federal Court Dismisses FTC Location Privacy Lawsuit – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mark Rasch Geolocation data is among the most sensitive personal data. Marketers can use this data to determine what you are likely...
ISMG Editors: The Plot Thickens for Capita in Breach Fallout – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Blockchain & Cryptocurrency , Incident & Breach Response , Next-Generation Technologies & Secure Development Also: The EU Adopts a Crypto Regulation;...
Ukraine’s Cyber Defense Success: Top Takeaways – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Experts Highlight the Importance of Preparation, Partnerships, Resilience Mathew J. Schwartz (euroinfosec)...
LockBit Leaks 1.5TB of Data Stolen From Indonesia’s BSI Bank – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Finance & Banking , Fraud Management & Cybercrime , Industry Specific Bank Syariah Indonesia Says Service Interruptions Were Maintenance Jayant Chakravarti...
LIVE Webinar | Hackers Don’t Back Down, So You Need to Back Up: Data Security’s Hardest Truths – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Steven Stone Head of Rubrik Zero Labs, Rubrik Steven Stone leads Rubrik’s new data threat research unit to uncover real-world intrusions...
French Privacy Watchdog Pledges Additional AI Oversight – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 General Data Protection Regulation (GDPR) , Governance & Risk Management , Privacy CNIL Says ‘Privacy-Friendly’ AI Systems Are a Must Akshaya...
Cryptohack Roundup: Uranium Finance, LayerZero, MiCA – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Blockchain & Cryptocurrency , Cryptocurrency Fraud , Fraud Management & Cybercrime Also: Ledger Faces Backlash on Seed Phrase Recovery Solution Rashmi...
Researchers Identify Second Developer of ‘Golden Chickens’ Malware – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Cybersecurity firm eSentire says it has identified the second developer of Golden Chickens, a malware suite used by financially-motivated cybercrime...
Cloudflare Unveils New Secrets Management Solution – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Cloudflare on Thursday announced Secrets Store, a new solution designed to help developers and organizations securely store and manage secrets...
Apple Patches 3 Exploited WebKit Zero-Day Vulnerabilities – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Apple on Thursday released security updates for its operating systems to patch dozens of vulnerabilities that could expose iPhones and...
Investors Make $6M Bet on Manifest for SBOM Management Technology – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Manifest, an early stage startup building technology to help businesses generate, collect, and operationalize software bill of materials (SBOMs), has...
RSAC Fireside Chat: Upgrading containment to counter Putin’s weaponizing of ransomware – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido The ransomware plague endures — and has arisen as a potent weapon in geopolitical conflicts. Related: The...
KeePass Flaw Exposes Master Passwords – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A vulnerability has been discovered in the KeePass password management software (v2.X), allowing an attacker to dump the master password from...
CommonMagic Malware Implants Linked to New CloudWizard Framework – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The CommonMagic malware implant has been associated with a previously unknown advanced persistent threat campaign linked to the Russo-Ukrainian conflict and...
Experts Warn of Voice Cloning-as-a-Service – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security experts are warning of surging threat actor interest in voice cloning-as-a-service (VCaaS) offerings on the dark web, designed to streamline...
Luxottica confirms 2021 data breach after info of 70M leaks online – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Luxottica has confirmed one of its partners suffered a data breach in 2021 that exposed the personal information of 70...
Cybercrime gang pre-infects millions of Android devices with malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A large cybercrime enterprise tracked as the “Lemon Group” has reportedly pre-installed malware known as ‘Guerilla’ on almost 9 million...
KeePass exploit helps retrieve cleartext master password, fix coming soon – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The popular KeePass password manager is vulnerable to extracting the master password from the application’s memory, allowing attackers who compromise...
Apple fixes three new zero-days exploited to hack iPhones, Macs – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Apple has addressed three new zero-day vulnerabilities exploited in attacks to hack into iPhones, Macs, and iPads. “Apple is aware...