Source: heimdalsecurity.com – Author: Cristian Neagu Nearly 9 million Android-based smartphones, watches, TVs, and TV boxes have been infected with the “Guerrilla” malware, pre-installed on the...
Application Control 101: Definition, Features, Benefits, and Best Practices – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Mihaela Marian Application control is part and parcel of the larger cybersecurity landscape of access control, as outlined by the National Institute...
IOTW: Location data of two million customers exposed in Toyota data breach
A cloud misconfiguration in car manufacturer Toyota’s servers may have leaked sensitive information belonging to more than two million customers. The cloud misconfiguration meant that sensitive...
LockBit Leaks 1.5TB of Data Stolen From Indonesia’s BSI Bank – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Finance & Banking , Fraud Management & Cybercrime , Industry Specific Bank Syariah Indonesia Says Service Interruptions Were Maintenance Jayant Chakravarti...
Live Webinar | The Evolution of Software Supply Chain Attacks – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Brian Fox Co-founder and CTO, Sonatype Co-founder and CTO, Brian Fox is a Governing Board member for the Opensource Security Foundation,...
Ukraine’s Cyber Defense Success: Top Takeaways – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Experts Highlight the Importance of Preparation, Partnerships, Resilience Mathew J. Schwartz (euroinfosec)...
LIVE Webinar | Inside The State of Data Security: The Hard Truths – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Steven Stone Head of Rubrik Zero Labs, Rubrik Steven Stone leads Rubrik’s new data threat research unit to uncover real-world intrusions...
Cryptohack Roundup: Uranium Finance, LayerZero, MiCA – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Blockchain & Cryptocurrency , Cryptocurrency Fraud , Fraud Management & Cybercrime Also: Ledger Faces Backlash on Seed Phrase Recovery Solution Rashmi...
LIVE Webinar | Hackers Don’t Back Down, So You Need to Back Up: Data Security’s Hardest Truths – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Steven Stone Head of Rubrik Zero Labs, Rubrik Steven Stone leads Rubrik’s new data threat research unit to uncover real-world intrusions...
Breach Roundup: Philadelphia Inquirer – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Breach Notification , Fraud Management & Cybercrime , Incident & Breach Response Also: Swiss Multinational ABB, Lacroix, US DOT and Qilin...
French Privacy Watchdog Pledges Additional AI Oversight – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 General Data Protection Regulation (GDPR) , Governance & Risk Management , Privacy CNIL Says ‘Privacy-Friendly’ AI Systems Are a Must Akshaya...
Accessibility should be a cybersecurity priority, says UK NCSC – Source: www.csoonline.com
Source: www.csoonline.com – Author: Cybersecurity training, controls, and requirements that are inaccessible, especially to those with disabilities, can make businesses less secure and more vulnerable to...
Critical remote code execution flaws patched in Cisco small business switches – Source: www.csoonline.com
Source: www.csoonline.com – Author: Some of the vulnerabilities could lead to complete compromise of the device as a proof of concept is publicly available. Cisco patched...
Organizations reporting cyber resilience are hardly resilient: Study – Source: www.csoonline.com
Source: www.csoonline.com – Author: The study commissioned by Immersive Labs finds majority of cyber resilient companies lack tools to assess their resilience. While most organizations have...
5 useful search engines for internet‑connected devices and services – Source: www.welivesecurity.com
Source: www.welivesecurity.com – Author: Camilo Gutiérrez Amaya A roundup of some of the handiest tools that security professionals can use to search for and monitor devices...
Meet “AI”, your new colleague: could it expose your company’s secrets? – Source: www.welivesecurity.com
Source: www.welivesecurity.com – Author: Roman Cuprik Before rushing to embrace the LLM-powered hire, make sure your organization has safeguards in place to avoid putting its business...
Proofpoint Joins Joint Cyber Defense Collaborative – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Public-private partnership will facilitate a holistic and synchronized approach to threat prevention, detection, and response SUNNYVALE, Calif., May 17, 2023 –...
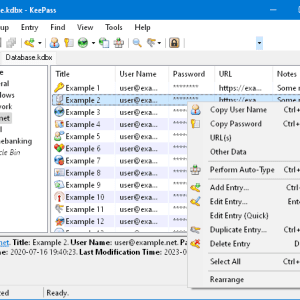
KeePass Vulnerability Imperils Master Passwords – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading For the second time in recent months a security researcher has discovered a vulnerability in the...
Trojan-Rigged Phishing Attacks Pepper China-Taiwan Conflict – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Cyber espionage attacks against organizations in Taiwan have surged against the backdrop of recent political tensions,...
10 Types of AI Attacks CISOs Should Track – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ericka Chickowski, Contributing Writer, Dark Reading Keep up with the latest cybersecurity threats, newly-discovered vulnerabilities, data breach information, and emerging trends. Delivered...
Microsoft Azure VMs Hijacked in Cloud Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A threat actor known for targeting Microsoft cloud environments now is employing the serial console feature on...
Embedding Security by Design: A Shared Responsibility – Source: www.darkreading.com
Source: www.darkreading.com – Author: Stephen de Vries, Co-Founder & CEO, IriusRisk Amid a feverish cybersecurity environment, there is a growing chorus for software to be secure...
OX Security Launches OX-GPT, AppSec’s First ChatGPT Integration – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 TEL AVIV, Israel, May 17, 2023 /PRNewswire/ — OX Security, a leader in software supply chain security, today announced the launch of OX-GPT, the...
Satori Augments Its Data Security Platform With Posture Management and Data Store Discovery Capabilities – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 Sunnyvale, CA — May 17, 2023 — Satori, the industry’s leading data security platform, today announced the availability of Posture Management,...
Once Again, Malware Discovered Hidden in npm – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer, Dark Reading Two code packages named “nodejs-encrypt-agent” in the popular npm JavaScript library and registry recently were discovered...
LexisNexis Risk Solutions Cybercrime Report Reveals 20% Annual Increase in Global Digital Attack Rate – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 ATLANTA, May 17, 2023 /PRNewswire/ — LexisNexis® Risk Solutions today released the results of its annual Cybercrime Report, an analysis of data from...
WithSecure Launches New Range of Incident Response and Readiness Services – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 Helsinki, Finland – May 17, 2023: The first 72 hours of an attack are a crucial window for incident response teams....
KeePass 2.X Master Password Dumper allows retrieving the KeePass master password – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A researcher published a PoC tool to retrieve the master password from KeePass by exploiting the CVE-2023-32784 vulnerability. Security researcher...
Admin of the darknet carding platform Skynet Market pleads guilty – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A US national has pleaded guilty to operating the carding site Skynet Market and selling financial information belonging to tens...
Critical fixed critical flaws in Cisco Small Business Switches – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Cisco fixed nine flaws in its Small Business Series Switches that could be exploited to execute arbitrary code or cause...