Source: www.bleepingcomputer.com – Author: Bill Toulas A new malware distribution campaign is underway impersonating the CapCut video editing tool to push various malware strains to unsuspecting...
HP rushes to fix bricked printers after faulty firmware update – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan HP is working to address a bad firmware update that has been bricking HP Office Jet printers worldwide since it was...
npm packages caught serving TurkoRAT binaries that mimic NodeJS – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma Researchers have discovered multiple npm packages named after NodeJS libraries that even pack a Windows executable that resembles NodeJS but instead...
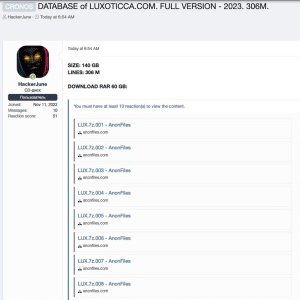
2021 data breach exposed data of 70 Million Luxottica customers – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Luxottica has finally confirmed the 2021 data breach that exposed the personal information of 70 million customers. Luxottica Group S.p.A. is...
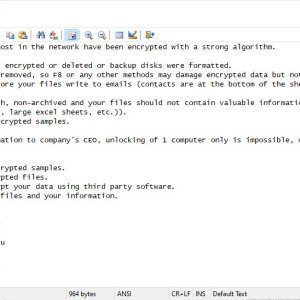
Cybercrime gang FIN7 returned and was spotted delivering Clop ransomware – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Cybercriminal gang FIN7 returned with a new wave of attacks aimed at deploying the Clop ransomware on victims’ networks. Researchers...
US CISA warns of a Samsung vulnerability under active exploitation – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini US CISA added the vulnerability CVE-2023-21492 flaw affecting Samsung devices to its Known Exploited Vulnerabilities Catalog. US CISA added the...
RSAC Fireside Chat: Counteracting Putin’s weaponizing of ransomware — with containment – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido By Byron V. Acohido The ransomware plague endures — and has arisen as a potent weapon in geopolitical conflicts. Cyber extortion...
Live panel discussion on insider threats and abuse of privilege – Source: securityboulevard.com
Source: securityboulevard.com – Author: Scott Wright And as we move into artificial intelligence, we have to look at different things like hijacked artificial intelligence with inside...
Exposing The “Denis Gennadievich Kulkov” a.k.a Kreenjo/Nordex/Nordexin/Try2Check Cybercriminal Enterprise – An Analysis – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dancho Danchev Who would have thought? The U.S Secret Service is currently offering $10M reward for Denis Gennadievich Kulkov also known as Kreenjo/Nordex/Nordexin...
Digital Trust Digest: This Week’s Must-Know News – Source: securityboulevard.com
Source: securityboulevard.com – Author: Keyfactor Team The Digital Trust Digest is a curated overview of the week’s top cybersecurity news. Here’s what you need to know...
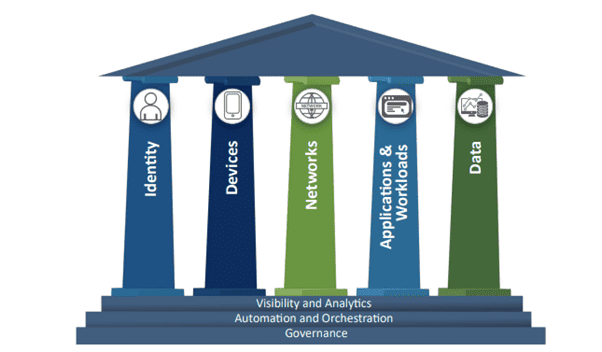
Zero Trust is More Than a Slogan – Source: securityboulevard.com
Source: securityboulevard.com – Author: Bhagwat Swaroop When it comes to Zero Trust, the conversation has moved from being a nebulous term several years ago to a...
How Companies Should Protect Sensitive Data: 6 Practical Tips – Source: securityboulevard.com
Source: securityboulevard.com – Author: Aimee Simpson It’s no secret that sensitive data management is a top priority for security teams, particularly during periods of widespread workforce...
Friday Squid Blogging: Peruvian Squid-Fishing Regulation Drives Chinese Fleets Away – Source: securityboulevard.com
Source: securityboulevard.com – Author: Bruce Schneier A Peruvian oversight law has the opposite effect: Peru in 2020 began requiring any foreign fishing boat entering its ports...
Your SOC 2 Toolkit Essentials for Compliance Excellence – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richa Tiwari Achieving SOC 2 compliance often necessitates the use of specialized tools and software to address specific application and data security...
BSidesSF 2023 – Ehsan Asdar, Nishil Shah – Building Production-Grade End To End Encrypted Applications – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/05/bsidessf-2023-ehsan-asdar-nishil-shah-building-production-grade-end-to-end-encrypted-applications/ Category & Tags: Security Bloggers Network,appsec education,BsidesSF,BSidesSF...
The Sky’s the Limit: The Growth of FedRAMP Compliant Cloud Service Offerings – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jenn Sherman As you’ll recall from our last post, FedRAMP just soared to a major milestone – 300 FedRAMP Authorized Cloud Service...
Phishing Vendor Sells IP Addresses to Duck Anomaly Detection – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Business Email Compromise (BEC) , Fraud Management & Cybercrime BulletProofLink Found a Way to Thwart Impossible Travel Detection Prajeet Nair (@prajeetspeaks)...
Zero Trust Authentication: Foundation of Zero Trust Security – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Remote Workforce , Zero Trust Beyond Identity’s Husnain Bajwa on a Solution That Supports Zero Trust...
Cyberattacks on Taiwan Surge Amid Chinese Aggression – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Rise in Use of PlugX Malware Points to Chinese Nation-State Activity Jayant...
Apple Fixes 3 Zero-Days Exploited in the Wild – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Endpoint Security , Governance & Risk Management , Patch Management Vulnerabilities Exist in Apple-Mandated WebKit Browser Engine Mihir Bagwe (MihirBagwe) ,...
The FTC Pushes Boundaries With Proposed Health Rule Change – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Privacy , Standards, Regulations & Compliance Consumer Health Data Needs More Protections – Is the FTC...
Healthcare attacks are increasing: Why zero trust will prevent care disruptions – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau By Itai Greenberg, Chief Strategy Officer, Check Point. EXECUTIVE SUMMARY: Healthcare cyber attacks are on the rise. Zero trust is a...
What is business identity theft and how can you prevent it? – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: In the way that the identity of a person can be stolen, the identity of a business can also...
RSAC Fireside Chat: Counteracting Putin’s weaponizing of ransomware — with containment – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido The ransomware plague endures — and has arisen as a potent weapon in geopolitical conflicts. Related: The...
US Teenager Indicted for Credential Stuffing Attack on Fantasy Sports Website – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A Wisconsin teenager has been charged with accessing tens of thousands of user accounts at a fantasy sports and betting...
Pimcore Platform Flaws Exposed Users to Code Execution – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Security researchers are warning that vulnerabilities patched in the open-source Pimcore platform could have led to the execution of arbitrary...
2022 Purple Knight Report – Facing the Unknown – Uncoverging & Addressing Systemic Active Directory Security Failures by Purple Knight
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CommonMagic APT Campaign Broadens Target Scope to Central and Western Ukraine – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 Woburn, MA – May 19, 2023 – Kaspersky researchers have provided further details on the CommonMagic campaign, which was first observed...
Apple Patches 3 Zero-Days Possibly Already Exploited – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Three zero-day vulnerabilities — tracked as CVE-2023-32409, CVE-2023-28204, and CVE-2023-32373 — were found in Apple’s WebKit browser...
3 Common Initial Attack Vectors Account for Most Ransomware Campaigns – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Most ransomware attackers use one of three main vectors to compromise networks and gain access to...