Source: securityboulevard.com – Author: Richa Tiwari Few organizations can perform their daily tasks and operations without vendors and third-party partners. And even if they could, successful...
Author: Richa Tiwari
0 - CT 0 - CT - CISO Strategics - Privacy Compliance for Startups Customers Cyber Security News privacy rss-feed-post-generator-echo Security Bloggers Network Security Boulevard
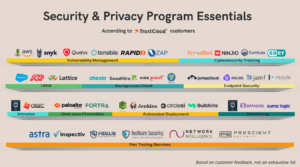
Your Shopping List for Security & Privacy Program Essentials – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richa Tiwari Whether your org is about to begin its journey for SOC 2, or you’re planning to wrangle up more standards...
0 - CT 0 - CT - CISO Strategics - Privacy Compliance for Startups Customers Cyber Security News privacy rss-feed-post-generator-echo Security Bloggers Network Security Boulevard
Your Shopping List for Security & Privacy Program Essentials – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richa Tiwari Whether your org is about to begin its journey for SOC 2, or you’re planning to wrangle up more standards...
Cyber Security News FedRAMP rss-feed-post-generator-echo Security Bloggers Network Security Boulevard
What are FedRAMP Requirements? (And Who Needs to Know) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richa Tiwari For SaaS applications and cloud service providers (CSPs), maintaining compliance with FedRAMP requirements is critical to the bottom line. It...
0 - CT 0 - CT - CISO Strategics - Risk & Compliance Cyber Security News rss-feed-post-generator-echo Security Bloggers Network Security Boulevard SOC 2
Your SOC 2 Toolkit Essentials for Compliance Excellence – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richa Tiwari Achieving SOC 2 compliance often necessitates the use of specialized tools and software to address specific application and data security...