Source: www.infosecurity-magazine.com – Author: 1 Millions of customers of one of America’s largest dental health insurers have had their personal information compromised after a ransomware breach....
Hackers Win $105,000 for Reporting Critical Security Flaws in Sonos One Speakers – Source:thehackernews.com
Source: thehackernews.com – Author: . May 30, 2023Ravie LakshmananZero Day / Vulnerability Multiple security flaws uncovered in Sonos One wireless speakers could be potentially exploited to...
CAPTCHA-Breaking Services with Human Solvers Helping Cybercriminals Defeat Security – Source:thehackernews.com
Source: thehackernews.com – Author: . May 30, 2023Ravie Lakshmanan Cybersecurity researchers are warning about CAPTCHA-breaking services that are being offered for sale to bypass systems designed...
Implementing Risk-Based Vulnerability Discovery and Remediation – Source:thehackernews.com
Source: thehackernews.com – Author: . In this day and age, vulnerabilities in software and systems pose a considerable danger to businesses, which is why it is...
Sneaky DogeRAT Trojan Poses as Popular Apps, Targets Indian Android Users – Source:thehackernews.com
Source: thehackernews.com – Author: . A new open source remote access trojan (RAT) called DogeRAT targets Android users primarily located in India as part of a...
RaidForums Members Data Leaked on New Hacking Forum – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Cristian Neagu Threat actors and security researchers now have access to a database for the notorious RaidForums hacking forums, giving them insight...
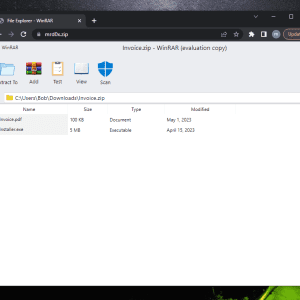
Beware of the new phishing technique “file archiver in the browser” that exploits zip domains – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini “file archiver in the browser” is a new phishing technique that can be exploited by phishers when victims visit a...
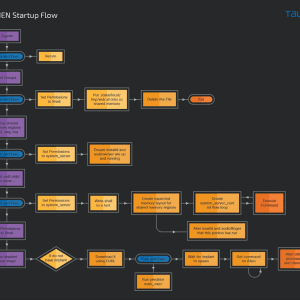
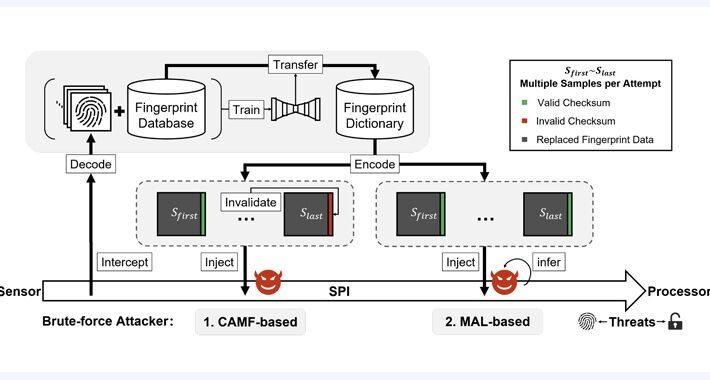
BrutePrint Attack allows to unlock smartphones with brute-forcing fingerprint – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers devised an attack technique, dubbed BrutePrint Attack, that allows brute-forcing fingerprints on smartphones to bypass authentication. Researchers have devised...
Lockbit ransomware attack on MCNA Dental impacts 8.9M individuals – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Managed Care of North America (MCNA) Dental disclosed a data breach that impacted more than 8.9 million individuals. Managed Care...
New Go-written GobRAT RAT targets Linux Routers in Japan – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A new Golang remote access trojan (RAT), tracked as GobRAT, is targeting Linux routers in Japan, the JPCERT Coordination Center warns....
Researchers analyzed the PREDATOR spyware and its loader Alien – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Cisco Talos and the Citizen Lab researchers have published a technical analysis of the powerful Android spyware Predator. Security researchers...
Upskilling the non-technical: finding cyber certification and training for internal hires – Source: www.csoonline.com
Source: www.csoonline.com – Author: Andrey Popov / Shutterstock Finding qualified staff to replace vacancies or build out an expanding team can be a nightmare for already...
Prevention-first: Protecting cities from ransomware – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau By Pete Nicoletti, Check Point Field CISO, Americas In recent months, several American cities were hit by debilitating and disruptive ransomware...
Invoice and CEO Scams Dominate Fraud Impacting Businesses – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Card Not Present Fraud , Finance & Banking , Fraud Management & Cybercrime UK Financial Services Firms Record $1.5 Billion in...
Top Privacy Considerations for Website Tracking Tools – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Governance & Risk Management , Incident & Breach Response , Privacy Lokker CEO Ian Cohen on Growing Health Information Concerns With...
Sports Warehouse Fined $300,000 Over Payment Card Data Theft – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Audit , Card Not Present Fraud , Cybercrime Data Breach Exposed Nearly 20 Years of ‘Indefinitely’ Stored Payment Card Data Mathew...
New BrutePrint Attack Lets Attackers Unlock Smartphones with Fingerprint Brute-Force – Source:thehackernews.com
Source: thehackernews.com – Author: . May 29, 2023Ravie LakshmananAuthentication / Mobile Security Researchers have discovered an inexpensive attack technique that could be leveraged to brute-force fingerprints...
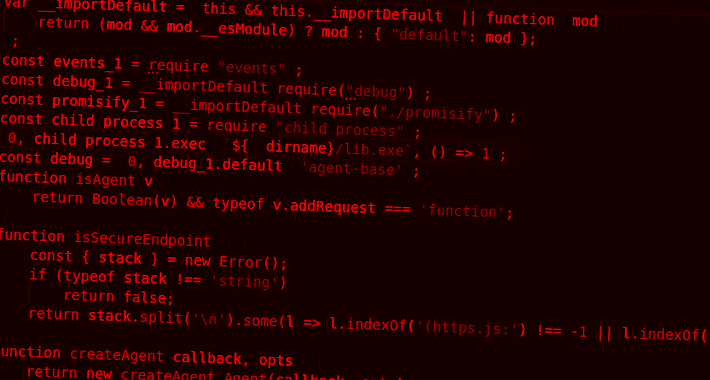
Developer Alert: NPM Packages for Node.js Hiding Dangerous TurkoRat Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Two malicious packages discovered in the npm package repository have been found to conceal an open source information stealer malware called...
Searching for AI Tools? Watch Out for Rogue Sites Distributing RedLine Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . May 19, 2023Ravie LakshmananArtificial Intelligence / Cyber Threat Malicious Google Search ads for generative AI services like OpenAI ChatGPT and Midjourney...
WebKit Under Attack: Apple Issues Emergency Patches for 3 New Zero-Day Vulnerabilities – Source:thehackernews.com
Source: thehackernews.com – Author: . May 19, 2023Ravie LakshmananZero-Day / Endpoint Security Apple on Thursday rolled out security updates to iOS, iPadOS, macOS, tvOS, watchOS, and...
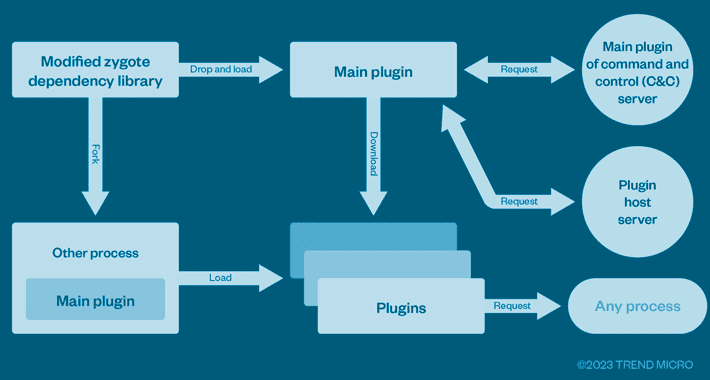
This Cybercrime Syndicate Pre-Infected Over 8.9 Million Android Phones Worldwide – Source:thehackernews.com
Source: thehackernews.com – Author: . A cybercrime enterprise known as Lemon Group is leveraging millions of pre-infected Android smartphones worldwide to carry out their malicious operations,...
Flash loan attack on Jimbos Protocol steals over $7.5 million – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Jimbos Protocol, an Arbitrum-based DeFi project, has suffered a flash loan attack that resulted in the loss of more than...
MCNA Dental data breach impacts 8.9 million people after ransomware attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Managed Care of North America (MCNA) Dental has published a data breach notification on its website, informing almost 9 million...
Lazarus hackers target Windows IIS web servers for initial access – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The notorious North Korean state-backed hackers, known as the Lazarus Group, are now targeting vulnerable Windows Internet Information Services (IIS)...
How to Secure Your SCM Repositories with GitGuardian Honeytokens – Source: securityboulevard.com
Source: securityboulevard.com – Author: Guest Expert Sponsorships Available Keshav Malik Keshav is a full-time Security Engineer who loves to build and break stuff. He is constantly...
From Data Chaos to Data Mastery How to Build and Scale Data Lakes with AWS Services – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dariel Marlow In today’s data-driven world, organizations are faced with an ever-increasing volume of data from various sources. To extract meaningful insights...
Protecting your business: Advice to SMB CEOs from a former CIO – Source: securityboulevard.com
Source: securityboulevard.com – Author: Avast Blog The acronym CIO is sometimes understood to stand for “Career Is Over,” and here’s why: Business leaders in charge of...
The Top Threats to Cloud Infrastructure Security and How to Address Them – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dariel Marlow What is infrastructure security in Cloud Computing? Infrastructure security refers to the protection of physical and virtual components that make...
United States of America: Memorial Day 2023 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Essential security practices in OT control systems – Source: securityboulevard.com
Source: securityboulevard.com – Author: Prayukth K V Operational Technology (OT) security controls include the measures, workflows and procedures put in place to protect various OT systems...