Source: securityboulevard.com – Author: Tom Eston In this episode, we discuss Meta’s record-breaking $1.3 billion fine by the EU for unlawfully transferring user data, shedding light...
LogRhythm Receives Best SIEM – Computer Software at the SBR Technology Excellence Awards 2023 for its Ability to Eliminate Noise Effectively – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nicholas Tan SINGAPORE – 29 May 2022 – LogRhythm, a leading cybersecurity company, has been recognised with the SIEM – Computer Software...
Are We Seeing Fewer Ransomware Attacks? Not Now – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lohrmann on Cybersecurity Despite what you may have heard, ransomware threats continue to grow and evolve in mid-2023. Here’s what you need...
Invoice and CEO Scams Dominate Fraud Impacting Businesses – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Card Not Present Fraud , Finance & Banking , Fraud Management & Cybercrime UK Financial Services Firms Record $1.5 Billion in...
Top Privacy Considerations for Website Tracking Tools – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Incident & Breach Response , Privacy Lokker CEO Ian Cohen on Growing Health Information Concerns With...
Sports Warehouse Fined $300,000 Over Payment Card Data Theft – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Audit , Card Not Present Fraud , Cybercrime Data Breach Exposed Nearly 20 Years of ‘Indefinitely’ Stored Payment Card Data Mathew...
Protect your business network with PureDome – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Graham Cluley Security News is sponsored this week by the folks at PureDome. Thanks to the great team there for...
Top Cyberattacks Revealed in New Threat Intelligence Report – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 We recognize that in today’s world, security leaders must expand their focus beyond technologies and their vulnerabilities. To effectively manage risk,...
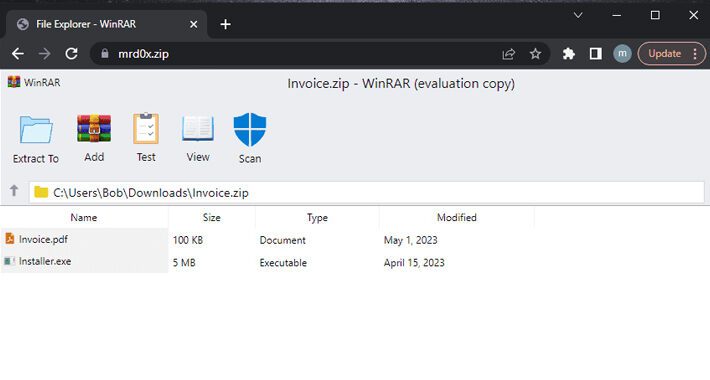
New Phishing Kit: File Archivers in the Browser – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Andreea Chebac A new phishing kit, “File Archivers in the Browser” abuses ZIP domains. The kit displays bogus WinRAR or Windows File...
New Mirai Variant Campaigns are Targeting IoT Devices – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Unit 42, Palo Alto Networks threat research team, has found new malicious activity targeting IoT devices, using a variant of Mirai,...
Hackers hold city of Augusta hostage in a ransomware attack – Source: www.csoonline.com
Source: www.csoonline.com – Author: The ransomware group has released 10GB of sample data from the cyberattack on the US city of Augusta and claimed they have...
New phishing technique poses as a browser-based file archiver – Source: www.csoonline.com
Source: www.csoonline.com – Author: The new technique has a hacker simulate an archiving software in the web browser to trick the victim as he tries to...
Insider risk management: Where your program resides shapes its focus – Source: www.csoonline.com
Source: www.csoonline.com – Author: Choosing which department should be responsible for protecting an organization from threats from within isn’t always straightforward. There’s no getting around it,...
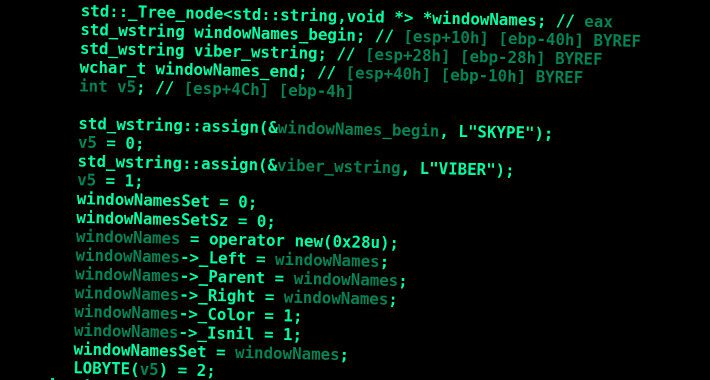
AceCryptor: Cybercriminals’ Powerful Weapon, Detected in 240K+ Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . May 29, 2023Ravie LakshmananCyber Threat / Malware A crypter (alternatively spelled cryptor) malware dubbed AceCryptor has been used to pack numerous...
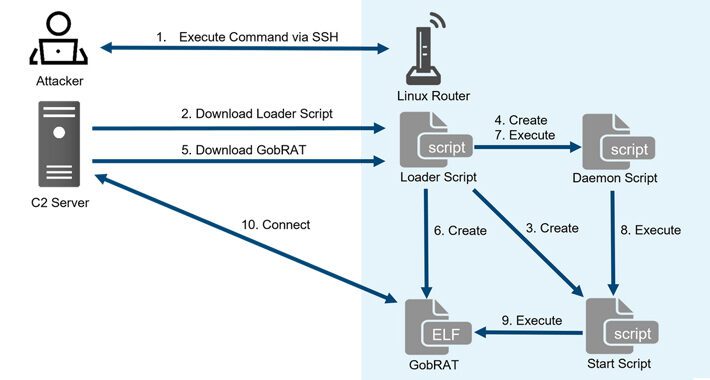
New GobRAT Remote Access Trojan Targeting Linux Routers in Japan – Source:thehackernews.com
Source: thehackernews.com – Author: . May 29, 2023Ravie LakshmananLinux / Network Security Linux routers in Japan are the target of a new Golang remote access trojan...
Don’t Click That ZIP File! Phishers Weaponizing .ZIP Domains to Trick Victims – Source:thehackernews.com
Source: thehackernews.com – Author: . A new phishing technique called “file archiver in the browser” can be leveraged to “emulate” a file archiver software in a...
PyPI Implements Mandatory Two-Factor Authentication for Project Owners – Source:thehackernews.com
Source: thehackernews.com – Author: . May 29, 2023Ravie LakshmananSupply Chain / Programming The Python Package Index (PyPI) announced last week that every account that maintains a...
Bad Magic’s Extended Reign in Cyber Espionage Goes Back Over a Decade – Source:thehackernews.com
Source: thehackernews.com – Author: . May 22, 2023Ravie LakshmananCyber Espionage / Malware New findings about a hacker group linked to cyber attacks targeting companies in the...
Are Your APIs Leaking Sensitive Data? – Source:thehackernews.com
Source: thehackernews.com – Author: . It’s no secret that data leaks have become a major concern for both citizens and institutions across the globe. They can...
U.K. Fraudster Behind iSpoof Scam Receives 13-Year Jail Term for Cyber Crimes – Source:thehackernews.com
Source: thehackernews.com – Author: . May 22, 2023Ravie LakshmananCyber Crime / Hacking A U.K. national responsible for his role as the administrator of the now-defunct iSpoof...
KeePass Exploit Allows Attackers to Recover Master Passwords from Memory – Source:thehackernews.com
Source: thehackernews.com – Author: . May 22, 2023Ravie LakshmananPassword Security / Exploit A proof-of-concept (PoC) has been made available for a security flaw impacting the KeePass...
PyPI Repository Under Attack: User Sign-Ups and Package Uploads Temporarily Halted – Source:thehackernews.com
Source: thehackernews.com – Author: . May 21, 2023Ravie LakshmananSoftware Security / Malware The maintainers of Python Package Index (PyPI), the official third-party software repository for the...
Meet ‘Jack’ from Romania! Mastermind Behind Golden Chickens Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . The identity of the second threat actor behind the Golden Chickens malware has been uncovered courtesy of a “fatal” operational security...
Notorious Cyber Gang FIN7 Returns With Cl0p Ransomware in New Wave of Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . May 20, 2023Ravie LakshmananCyber Crime / Ransomware The notorious cybercrime group known as FIN7 has been observed deploying Cl0p (aka Clop)...
Warning: Samsung Devices Under Attack! New Security Flaw Exposed – Source:thehackernews.com
Source: thehackernews.com – Author: . May 20, 2023Ravie LakshmananMobile Security / Cyber Attack The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has warned of active exploitation...
Privacy Sandbox Initiative: Google to Phase Out Third-Party Cookies Starting 2024 – Source:thehackernews.com
Source: thehackernews.com – Author: . May 19, 2023Ravie LakshmananOnline Privacy / Tech News Google has announced plans to officially flip the switch on its twice-delayed Privacy...
Dr. Active Directory vs. Mr. Exposed Attack Surface: Who’ll Win This Fight? – Source:thehackernews.com
Source: thehackernews.com – Author: . Active Directory (AD) is among the oldest pieces of software still used in the production environment and can be found in...
Threat Intelligence & Dark web Monitoring Tools
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
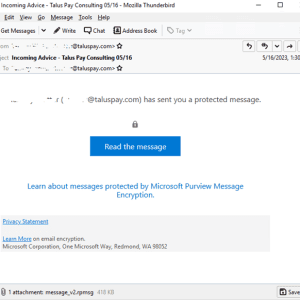
Attackers use encrypted RPMSG messages in Microsoft 365 targeted phishing attacks – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts warn of phishing attacks that are combining the use of compromised Microsoft 365 accounts and .rpmsg encrypted emails. Trustwave...
Industrial automation giant ABB disclosed data breach after ransomware attack – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Swiss electrification and automation technology giant ABB confirmed it has suffered a data breach after a ransomware attack. ABB has...