Source: thehackernews.com – Author: .
Two malicious packages discovered in the npm package repository have been found to conceal an open source information stealer malware called TurkoRat.
The packages – named nodejs-encrypt-agent and nodejs-cookie-proxy-agent – were collectively downloaded approximately 1,200 times and were available for more than two months before they were identified and taken down.
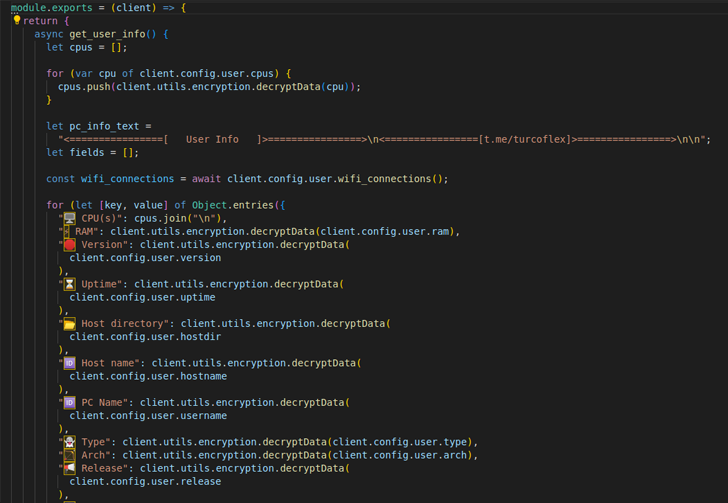
ReversingLabs, which broke down the details of the campaign, described TurkoRat as an information stealer capable of harvesting sensitive information such as login credentials, website cookies, and data from cryptocurrency wallets.
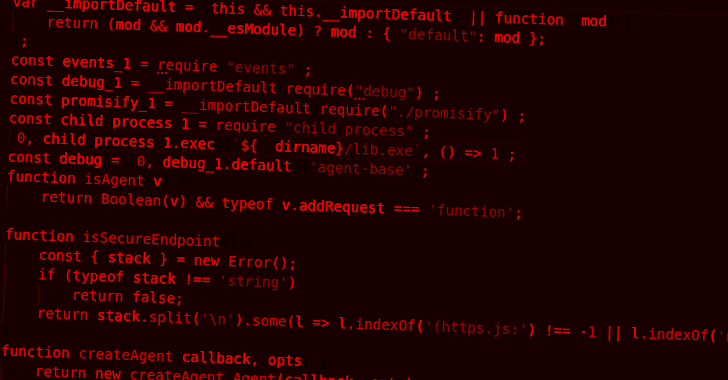
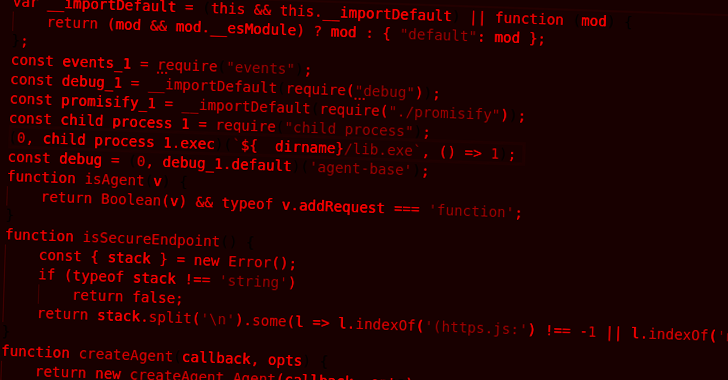
While nodejs-encrypt-agent came fitted with the malware inside, nodejs-cookie-proxy-agent was found to disguise the trojan as a dependency under the name axios-proxy.
nodejs-encrypt-agent was also engineered to masquerade as another legitimate npm module known as agent-base, which has been downloaded over 25 million times to date.
The list of the rogue packages and their associated versions are listed below –
- nodejs-encrypt-agent (versions 6.0.2, 6.0.3, 6.0.4, and 6.0.5)
- nodejs-cookie-proxy-agent (versions 1.1.0, 1.2.0, 1.2.1, 1.2.2, 1.2.3, and 1.2.4), and
- axios-proxy (versions 1.7.3, 1.7.4, 1.7.7, 1.7.9, 1.8.9, and 1.9.9)
“TurkoRat is just one of many open source malware families that are offered for ‘testing’ purposes, but can readily be downloaded and modified for malicious use, as well,” Lucija Valentić, threat researcher at ReversingLabs, said.
The findings once again underscore the ongoing risk of threat actors orchestrating supply chain attacks via open source packages and baiting developers into downloading potentially untrusted code.
“Development organizations need to scrutinize the features and behaviors of the open source, third-party and commercial code they are relying on in order to track dependencies and detect potential malicious payloads in them,” Valentić said.
The growing use of malicious npm packages fits in with a broader pattern of surging attacker interest in open source software supply chains, not to mention highlighting the increasing sophistication of threat actors.
Even more worryingly, researchers from Checkmarx published new research this month that showed how threat actors could impersonate authentic npm packages by “using lowercase letters to mimic uppercase letters in the original package names” (e.g., memoryStorageDriver vs memorystoragedriver).
“This malicious package impersonation takes the traditional ‘Typosquatting,’ attack method to a new level, where attackers register package names that consist of the exact same letters as the legitimate ones, with the only difference being capitalization,” researchers Teach Zornstein and Yehuda Gelb said.
“This makes it even harder for users to detect the deception since it can be easy to overlook the subtle differences in capitalization.”
The supply chain security company found that 1,900 out of 3,815 packages with capital letters in their titles could have been at risk of copycat attacks if not for a fix pushed by the npm maintainers to address the problem, which, Checkmarx said, has existed since December 2017.
The disclosure also follows another advisory from Check Point, which identified three malicious extensions hosted on the VS Code extensions marketplace. They have been purged as of May 14, 2023.
The add-ons, named prettiest java, Darcula Dark, and python-vscode, were cumulatively downloaded over 46,000 times and incorporated features that allowed the threat actors to steal credentials, system information, and establish a remote shell on the victim’s machine.
UPCOMING WEBINAR
Zero Trust + Deception: Learn How to Outsmart Attackers!
Discover how Deception can detect advanced threats, stop lateral movement, and enhance your Zero Trust strategy. Join our insightful webinar!
It’s not just npm and VS Code marketplace, for a similar set of rogue libraries have been unearthed from the Python Package Index (PyPI) software repository as well.
Some of these packages were designed to distribute a cryptocurrency clipper malware dubbed KEKW, while other typosquatted versions of the popular flask framework included backdoor functions to receive commands from a remote server.
Another Python package uncovered by Israeli company Phylum this week was found to contain a malicious dependency that harbored an encrypted payload to grab Discord tokens and steal clipboard content in order to hijack cryptocurrency transactions.
The package, referred to as chatgpt-api by its developer Patrick Pogoda and accessible through GitHub, delivered on the functionality it advertised (i.e., interacting with OpenAI’s ChatGPT tool) in an attempt to complete the ruse. The repository is still available as of writing.
“For now this actor appears to be preying on the recent explosive rise in popularity of [Large Language Models] with this chatgpt-api package,” Phylum said, adding the threat actor likely has an automated mechanism to upload new iterations of the malicious dependency every time it’s taken down and “maintain a persistent infection.”
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.
Original Post url: https://thehackernews.com/2023/05/developer-alert-npm-packages-for-nodejs.html
Category & Tags: –
Views: 0