Source: www.bleepingcomputer.com – Author: Lawrence Abrams Microsoft is rolling out a new version of the Paint application on Windows 11 Insider builds that can remove the...
Cisco BroadWorks Is Affected by a Critical-Severity Vulnerability – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Cristian Neagu The Cisco BroadWorks Application Delivery Platform and Cisco BroadWorks Xtended Services Platform are both affected by a serious vulnerability that...
Warning: RocketMQ Vulnerability Actively Exploited by Threat Actors – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Cristian Neagu The U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds a new critical-severity vulnerability to its KEV catalog. The issue is...
Evil Telegram doppelganger attacks Chinese users – Source: securelist.com
Source: securelist.com – Author: Igor Golovin A while ago we discovered a bunch of Telegram mods on Google Play with descriptions in traditional Chinese, simplified Chinese...
Feds Urge Immediately Patching of Zoho and Fortinet Products – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Attack Surface Management , Critical Infrastructure Security , Cyberwarfare / Nation-State Attacks Multiple Nation-State Hacking Groups Actively Exploiting Known Vulnerabilities Mathew...
5 Simple Ways to Improve Your Cybersecurity Posture – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Matt Wiseman Sr. Product manger, OPSWAT Matt Wiseman is a Sr. Product Manager at OPSWAT managing the OT product line. Matt’s...
Tattletale Ransomware Gangs Threaten to Reveal GDPR Breaches – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Ransomware Repeat Shakedown Tactic: Victims Told to Pay Up or Else They’ll Face Massive Fines Mathew...
Why Connected Devices Are Such a Risk to Outpatient Care – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 The number of connected devices used in healthcare is growing as manufacturers constantly introduce new types of IoT equipment. The ever-evolving...
Trail of Errors Led to Chinese Hack of Microsoft Cloud Email – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyberwarfare / Nation-State Attacks , Encryption & Key Management , Fraud Management & Cybercrime Crash Dump Snapshot Included Active Signing Key...
Keeping Your Side of the Street Clean: 5 Cyber-Hygiene Facts You Wish You Knew Earlier – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Brian Reed Chief Mobility Officer, NowSecure Brian Reed brings decades of experience in mobile, apps, security, dev and operations helping Fortune...
Experts Probe AI Risks Around Malicious Use, China Influence – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Senate Hearing Examines Misuse of Advanced AI Systems, Risks With...
California Executive Order Hopes to Ensure ‘Trustworthy AI’ – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Government , Industry Specific Governor Sets 2-Year Deadline for Policies on AI Use, Risks at...
North Korean Hackers Exploit Zero-Day Bug to Target Cybersecurity Researchers – Source:thehackernews.com
Source: thehackernews.com – Author: . Threat actors associated with North Korea are continuing to target the cybersecurity community using a zero-day bug in unspecified software over...
CISA Warning: Nation-State Hackers Exploit Fortinet and Zoho Vulnerabilities – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 08, 2023THNEndpoint Security / Exploit The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday warned that multiple nation-state actors...
Apple Rushes to Patch Zero-Day Flaws Exploited for Pegasus Spyware on iPhones – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 08, 2023THNSpyware / Vulnerability Apple on Thursday released emergency security updates for iOS, iPadOS, macOS, and watchOS to address two...
Apple Patches Actively Exploited iOS, macOS Zero-Days – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Apple on Thursday pushed out an urgent point-update to its flagship iOS and macOS platforms to fix a pair of...
Rigged Software and Zero-Days: North Korean APT Caught Hacking Security Researchers – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Google’s threat hunting unit has again intercepted an active North Korean APT actor sliding into the DMs of security researchers...
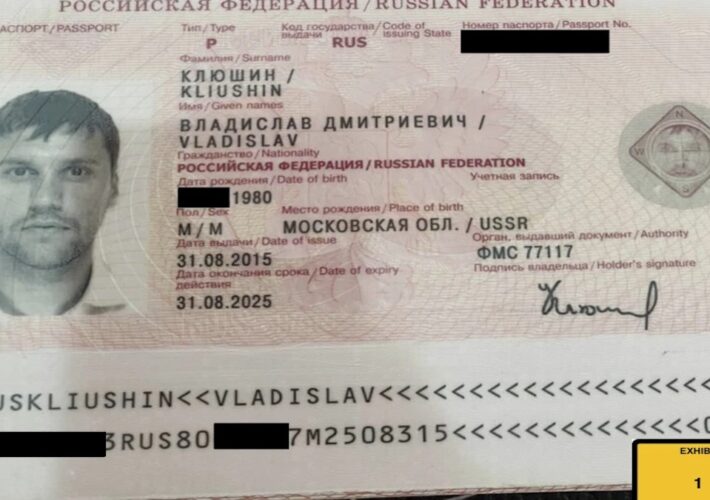
Wealthy Russian With Kremlin Ties Gets 9 Years in Prison for Hacking and Insider Trading Scheme – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press A wealthy Russian businessman with ties to the Kremlin was sentenced Thursday to nine years in prison for his role...
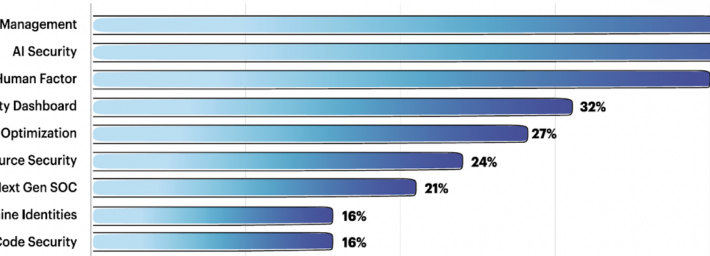
The Team8 Foundry Method for Selecting Investable Startups – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Team8 regularly consults with its CISO Village of around 350 enterprise CISOs over startup investments. AI security, 3rd party risk...
See Tickets Alerts 300,000 Customers After Another Web Skimmer Attack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Ticketing services agency See Tickets has notified more than 300,000 individuals that their payment card data was stolen in a...
CISA Releases Guidance on Adopting DDoS Mitigations – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The US Cybersecurity and Infrastructure Security Agency (CISA) has released new guidance to help federal agencies adopt distributed denial-of-service (DDoS)...
‘Atomic macOS Stealer’ Malware Delivered via Malvertising Campaign – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs A piece of malware named Atomic macOS Stealer, or AMOS, has been delivered by cybercriminals through a malvertising campaign, Malwarebytes...
Cisco Patches Critical Vulnerability in BroadWorks Platform – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Cisco on Wednesday announced patches for a critical-severity vulnerability in the BroadWorks Application Delivery Platform and BroadWorks Xtended Services Platform....
Tenable to Acquire Cloud Security Firm Ermetic for $240 Million – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Exposure management solutions provider Tenable announced on Thursday that it has entered into a definitive agreement to acquire Israeli cloud...
Apple Patches Two Zero-Days Exploited in Pegasus Attacks – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Apple has patched two critical zero-day vulnerabilities exploited in the wild to deliver eavesdropping malware from a notorious commercial spyware maker....
Patch ‘Em or Weep: Study Reveals Most Vulnerable IoT, Connected Assets – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Karl Greenberg on September 7, 2023, 2:36 PM EDT Patch ‘Em or Weep: Study Reveals Most Vulnerable IoT, Connected Assets Phones, tablets...
Vendor Comparison: DIY Home Security Systems – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: When it comes to DIY home security, there are many systems and components to consider and many decisions to make. This vendor...
Spoofing attacks: What they are & how to protect your business – Source: securityboulevard.com
Source: securityboulevard.com – Author: Scott Wright Spoofing attacks often happen through email or online messaging services and rely on the victim to provide sensitive information, such...
Wallarm Presenting at BSides Albuquerque – Source: securityboulevard.com
Source: securityboulevard.com – Author: wlrmblog If you’re in the Albuquerque area this Friday and/or Saturday, we hope you’re planning on going to BSides ABQ – it...
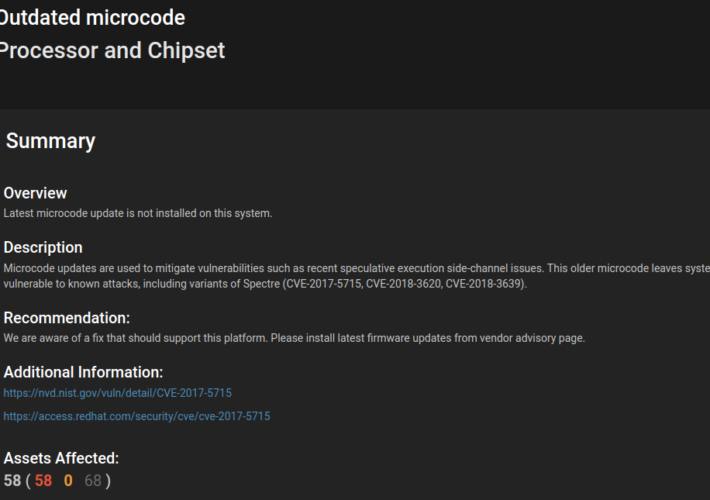
Demystifying CPU Microcode: Vulnerabilities, Updates, and Remediation – Source: securityboulevard.com
Source: securityboulevard.com – Author: Paul Asadoorian Attacks against low-level CPU architecture popped up on most tech people’s radar after the introduction of the Spectre and Meltdown...