Source: www.schneier.com – Author: Bruce Schneier LLMs and Tool Use Last March, just two weeks after GPT-4 was released, researchers at Microsoft quietly announced a plan...
Norway Court Upholds Temporary Ban of Behavioral Ads on Meta – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 General Data Protection Regulation (GDPR) , Governance & Risk Management , Privacy Facebook Sought to Halt Datatilsynet From Imposing Daily Fines...
Constant Vigilance: The Importance of Continuous Cybersecurity Monitoring – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Sean Martin Director of Product Strategy, CSI Business Solutions Group for Managed Services Sean Martin is director of Product Strategy, CSI...
Addressing Security Gaps and Risks Post-M&A in Healthcare – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 In the aftermath of mergers and acquisitions among healthcare entities – and the resulting IT integration and cost-cutting moves – gaps...
OnDemand Panel | Securing Identities in a Zero Trust Environment: A Blueprint for Government Agencies – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Zero Trust Tyler Cohen Wood , David Higgins , Robert Pritchard • September 8, 2023 ...
Webinar | Zero Trust Fundamentals: Start Your Journey Here – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Apple Fixes Zero-Click Bugs Exploited by NSO Group’s Spyware – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Endpoint Security ‘BlastPass’ Can Compromise iPhones Running the Latest iOS Version, Researchers Say Mihir Bagwe (MihirBagwe) • September 8, 2023 ...
ISMG Editors: Reasons to Cheer About Cybersecurity Market – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cloud Security , Healthcare , Industry Specific Also: Feds Out Hospitals Over Tracking Tools; Ongoing Saga of Wiz-SentinelOne Deal Anna Delaney...
China Unleashes AI-Powered Image Generation For Influence Operations – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 China has unveiled a new cyber capability powered by artificial intelligence, enabling the automatic generation of images for influence operations. These...
Cyber-criminals Exploit GPUs in Graphic Design Software – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security researchers at Cisco Talos have uncovered a scheme that preys on graphic designers and 3D modelers. Cyber-criminals are using cryptocurrency-mining...
Google TAG Exposes North Korean Campaign Targeting Researchers – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Google’s Threat Analysis Group (TAG) has shed light on a cyber campaign originating from North Korea, targeting security researchers engaged in...
Russian Man Handed Nine-Year Sentence for Hacking Scheme – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A US court has sentenced a Russian businessman to nine years in prison for an elaborate corporate hacking scheme that defrauded...
Regulator to Investigate Fertility App Security Concerns – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The UK’s data protection regulator is set to review how period and fertility tracking applications process user information, after revealing that...
CISA Adds Critical RocketMQ Bug to Must-Patch List – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The US government has ordered all federal civilian agencies to patch a critical vulnerability in Apache RocketMQ, which is currently being...
North Korea-linked threat actors target cybersecurity experts with a zero-day – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini North Korea-linked threat actors target cybersecurity experts with a zero-day Pierluigi Paganini September 08, 2023 North Korea-linked threat actors associated...
Zero-day in Cisco ASA and FTD is actively exploited in ransomware attacks – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Zero-day in Cisco ASA and FTD is actively exploited in ransomware attacks Pierluigi Paganini September 08, 2023 A zero-day vulnerability...
Nation-state actors exploit Fortinet FortiOS SSL-VPN and Zoho ManageEngine ServiceDesk Plus, CISA warns – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Nation-state actors exploit Fortinet FortiOS SSL-VPN and Zoho ManageEngine ServiceDesk Plus, CISA warns Pierluigi Paganini September 08, 2023 U.S. CISA...
Zero-days fixed by Apple were used to deliver NSO Group’s Pegasus spyware – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Zero-days fixed by Apple were used to deliver NSO Group’s Pegasus spyware Pierluigi Paganini September 08, 2023 Citizen Lab reported...
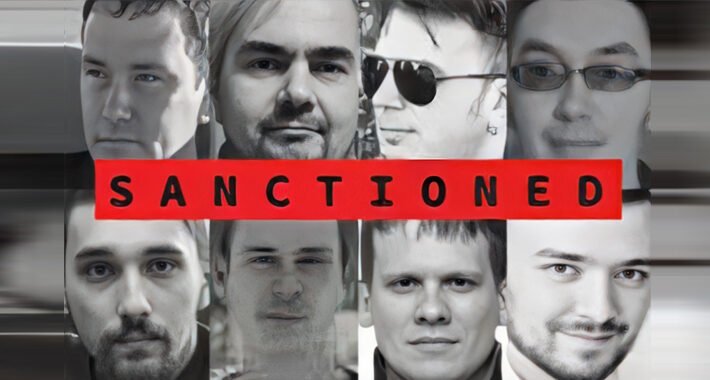
U.K. and U.S. Sanction 11 Russia-based Trickbot Cybercrime Gang Members – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 08, 2023THNCybercrime / Malware The U.K. and U.S. governments on Thursday sanctioned 11 individuals who are alleged to be part...
Cisco Issues Urgent Fix for Authentication Bypass Bug Affecting BroadWorks Platform – Source:thehackernews.com
Source: thehackernews.com – Author: . Cisco has released security fixes to address multiple security flaws, including a critical bug, that could be exploited by a threat...
Protecting Your Microsoft IIS Servers Against Malware Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Microsoft Internet Information Services (IIS) is a web server software package designed for Windows Server. Organizations commonly use Microsoft IIS servers...
‘Evil Telegram’ Spyware Campaign Infects 60K+ Mobile Users – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Dangerous spyware masquerading as a set of legitimate Telegram “mods” inside the official Google Play...
Kenya Initiates Public Sector Digital Skills Training, No Mention of Cybersecurity – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Kenya plans to open a center of excellence to better train public sector staff in digital...
Trickbot, Conti Sanctions Affect Top Cybercrime Brass – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The Russia-based Trickbot and Conti cybercrime syndicates are facing increased pressure from the United States and the...
3 Strategies to Defend Against Resurging Infostealers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ganesh Pai, Founder & CEO, Uptycs Most enterprise chief information security officers (CISOs) are very familiar with infostealers, a pervasive breed of...
Software Supply Chain Strategies to Parry Dependency Confusion Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Liad Cohen, Security Researcher & Developer, OX Security “What’s in a name? That which we call a rose By any other name...
Securing Your Legacy: Identities, Data, and Processes – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dirk Schrader, Resident CISO (EMEA) & VP of Security Research, Netwrix Legacy systems are the bane of IT pros everywhere. “Legacy” generally...
Overcoming Open Source Vulnerabilities in the Software Supply Chain – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security, Microsoft As workforces grow increasingly digital, developers are looking for new ways to streamline their workloads. Currently, 78% of businesses report using...
Dymocks Booksellers suffers data breach impacting 836k customers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Dymocks Booksellers is warning customers their personal information was exposed in a data breach after the company’s database was shared...
Cisco warns of VPN zero-day exploited by ransomware gangs – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Cisco is warning of a CVE-2023-20269 zero-day vulnerability in its Cisco Adaptive Security Appliance (ASA) and Cisco Firepower Threat Defense...