Source: securityboulevard.com – Author: Jeffrey Burt California lawmakers later this month are expected to vote on a highly debated bill that would make it easier for...
BSides Buffalo 2023 – Paul Robinson – If You Build It, They Will Come – A Guide To Building A Cybersecurity Program – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/bsides-buffalo-2023-paul-robinson-if-you-build-it-they-will-come-a-guide-to-building-a-cybersecurity-program/ Category & Tags: CISO Suite,Governance, Risk &...
Diving in to Day 2 Ops, Stateful Apps, & more with Kubernetes Experts – Source: securityboulevard.com
Source: securityboulevard.com – Author: Danielle Cook We had so many great questions about Kubernetes in the Enterprise in our recent Cloud Native Now webinar that I...
Ransomware and the Supply Chain – Source: securityboulevard.com
Source: securityboulevard.com – Author: Chris Garland This white paper discusses the increasing threat of ransomware attacks on the technology supply chain and provides insights on how...
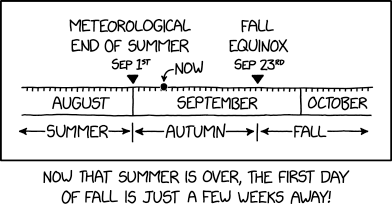
Randall Munroe’s XKCD ‘*Autumn And Fall’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/randall-munroes-xkcd-autumn-and-fall/ Category & Tags: Humor,Security Bloggers Network,Randall Munroe,Sarcasm,satire,XKCD...
BSides Buffalo 2023 – Kelsey Seymour – Dispelling The Myth Of “Maturity” In Threat Hunting – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/bsides-buffalo-2023-kelsey-seymour-dispelling-the-myth-of-maturity-in-threat-hunting/ Category & Tags: CISO Suite,Governance, Risk &...
Trail of Errors Led to Chinese Hack of Microsoft Cloud Email – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Encryption & Key Management , Fraud Management & Cybercrime Crash Dump Snapshot Included Active Signing Key...
5 Simple Ways to Improve Your Cybersecurity Posture – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Matt Wiseman Sr. Product manger, OPSWAT Matt Wiseman is a Sr. Product Manager at OPSWAT managing the OT product line. Matt’s...
Tattletale Ransomware Gangs Threaten to Reveal GDPR Breaches – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Ransomware Repeat Shakedown Tactic: Victims Told to Pay Up or Else They’ll Face Massive Fines Mathew...
Why Connected Devices Are Such a Risk to Outpatient Care – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 The number of connected devices used in healthcare is growing as manufacturers constantly introduce new types of IoT equipment. The ever-evolving...
California Executive Order Hopes to Ensure ‘Trustworthy AI’ – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Government , Industry Specific Governor Sets 2-Year Deadline for Policies on AI Use, Risks at...
Keeping Your Side of the Street Clean: 5 Cyber-Hygiene Facts You Wish You Knew Earlier – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Brian Reed Chief Mobility Officer, NowSecure Brian Reed brings decades of experience in mobile, apps, security, dev and operations helping Fortune...
Breach Roundup: Swedish Insurer Fined $3M for GDPR Breach – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Incident & Breach Response , Ransomware Also, Google Fitbit Faces Privacy Complaints From Schrems Anviksha More...
Experts Probe AI Risks Around Malicious Use, China Influence – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Senate Hearing Examines Misuse of Advanced AI Systems, Risks With...
Damaging hack? Compensation could be in the balance – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Key highlights In 2022, a small number of public companies (86 total) linked chief executive pay to cyber security....
Microsoft ID Security Gaps That Let Threat Actor Steal Signing Key – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Several security missteps on Microsoft’s part allowed a China-based threat actor to forge authentication tokens and...
North Korean Hackers Target Security Researchers — Again – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading North Korean state-supported threat actors are targeting security researchers — the second such campaign in the...
Apple Hit By 2 No-Click Zero-Days in Blastpass Exploit Chain – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Citizen Lab discovered two no-click zero-day vulnerabilities while checking an unidentified individual’s device, which was delivering mercenary...
Rwanda Launches Smart-City Investment Program – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Rwanda plans to modernize its infrastructure with a series of smart-city deployments that experts warn will...
Security for Multicloud and Hybrid Cloud Environments – Source: www.darkreading.com
Source: www.darkreading.com – Author: Anton Chuvakin, Security Advisor at Office of the CISO, Google Cloud No matter the industry, multicloud and hybrid cloud environments are an...
NFL Security Chief: Generative AI Threats a Concern as New Season Kicks Off – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Generative AI-enabled phishing attacks and deepfake videos are among the many threats that Tomás Maldonado will...
Weaponized Windows Installers Target Graphic Designers in Crypto Heist – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Attackers are targeting 3D modelers and graphic designers with malicious versions of a legitimate Windows installer tool...
How New SEC Rules Can Benefit Cybersecurity Teams – Source: www.darkreading.com
Source: www.darkreading.com – Author: Haywood Marsh, General Manager, NAVEX IRM & NetClaim The recent adoption of cybersecurity disclosure rules by the Securities and Exchange Commission (SEC)...
Peril vs. Promise: Companies, Developers Worry Over Generative AI Risk – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading The vast majority of developers believe that using generative AI systems will be necessary to increase...
Does Generative AI Comply With Asimov’s 3 Laws of Robotics? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Martin Lee, Technical Lead of Security Research & EMEA Lead, Cisco Talos Newly developed generative artificial intelligence (AI) tools that can generate...
CUAS Interpol Low Final
Unmanned aircraft systems (UAS), more commonly known as “drones,” are automated airborne vehicles sometimes described as flying robots or flying cell phones or computers. Drones have...
API Vulnerabilities: 74% of Organizations Report Multiple Breaches – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 API security company Traceable has unveiled its 2023 State of API Security Report. In collaboration with the Ponemon Institute, the study...
DGA Behavior Shifts Raise Cybersecurity Concerns – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Researchers at Akamai have unearthed a concerning shift in the behavior of dynamically seeded Domain Generation Algorithm (DGA) families within Domain...
Zero-Day Flaw Exposes Atlas VPN User IPs – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A Reddit user known as “Educational-Map-8145” has exposed a critical zero-day flaw affecting the Linux client of Atlas VPN, a popular virtual...
UK and US Sanction 11 Russians Tied to Trickbot/Conti Ransomware – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The US and the UK have sanctioned 11 individuals accused of being linked with the Trickbot malware and the Conti ransomware...