The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
GitHub warns users to enable 2FA before upcoming deadline – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Mayank Parmar GitHub is warning users that they will soon have limited functionality on the site if they do not enable two-factor...
Integris Health patients get extortion emails after cyberattack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Integris Health patients in Oklahoma are receiving blackmail emails stating that their data was stolen in a cyberattack on the...
Kazakhstan to Extradite Russian Hacker to Moscow – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime Nikita Kislitsin Has Twice Been Indicted in the United States Mihir Bagwe (MihirBagwe) • December...
Fighting AI-Fueled Attacks With AI-Based Cyber Tools – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Healthcare , Industry Specific Troy Hawes of Moss Adams on How Healthcare Entities Can Bolster...
Panel Discussion featuring Forrester Analyst | A CISO Guide to Calculating the ROI of Prisma Cloud – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Luca Son Consultant, Total Economic Impact, Forrester Luca Son is a consultant with Forrester’s Total Economic Impact™ (TEI) practice. In this...
NASA Releases First Space Cybersecurity Best Practices Guide – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Government , Industry Specific Agency Set to Bolster Space Cybersecurity Efforts Across Public and Private Sectors...
CYBERSECURITY TOOLKIT FOR ENTERPRISE LEADERS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity of Artificial Intelligence in the AI Act
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity for Fire Protection Systems
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CYBER SECURITY AWARENESS HANDBOOK
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity Awareness for Kids Age 10 to 15
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Managing Cyber Risk
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cyber Chief
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Riding the Waves of Compliance Navigating PCI DSS v4.0
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cyber Assessment Framework V3.1
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cyber Threat Report 2022 – 2023
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Common Vulnerability Scoring System version 4.0
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
TRAINING PROGRAM CAPTURE THE FLAG
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Critical Infrastructure Annual Risk Review
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CREDENTIAL DUMPING CHEATSHEET
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Countering Ransomware Financing
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CompTIA Security + Exam Study Guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Daily Malicious Files Soar 3% in 2023, Kaspersky Finds – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cybercriminals unleashed an average of 411,000 malicious files every day in 2023, representing a 3% increase from the previous year, according...
Carbanak Banking Malware Resurfaces with New Ransomware Tactics – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 26, 2023NewsroomMalware / Cybercrime The banking malware known as Carbanak has been observed being used in ransomware attacks with updated...
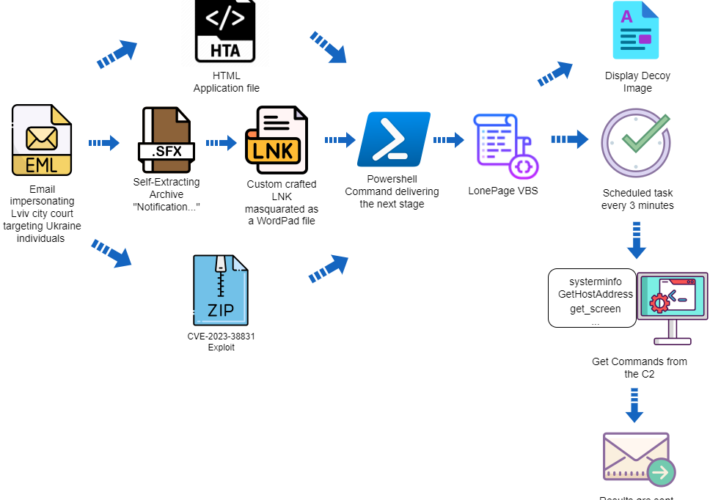
APT group UAC-0099 targets Ukraine exploiting a WinRAR flaw – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini APT group UAC-0099 targets Ukraine exploiting a WinRAR flaw Pierluigi Paganini December 25, 2023 The threat actor UAC-0099 is exploiting a...
Iran-linked APT33 targets Defense Industrial Base sector with FalseFont backdoor – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Iran-linked APT33 targets Defense Industrial Base sector with FalseFont backdoor Pierluigi Paganini December 25, 2023 Microsoft reports that the Iran-linked APT33...
GTA 5 source code reportedly leaked online a year after RockStar hack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams The source code for Grand Theft Auto 5 was reportedly leaked on Christmas Eve, a little over a year after the...
Google Chrome now scans for compromised passwords in the background – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Google says the Chrome Safety Check feature will work in the background to check if passwords saved in the web...
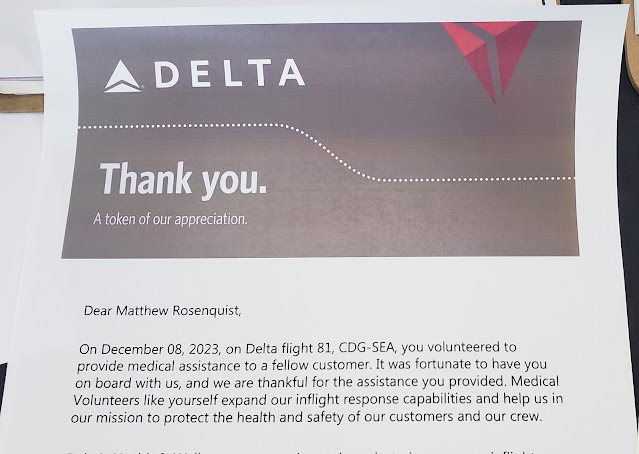
Medical Emergency Assistance – Thank You – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matthew Rosenquist I have been an active volunteer as part of corporate medical response teams for more than 20 years of my...