Source: securityboulevard.com – Author: Chris Garland Eclypsium is extending its digital supply chain security to cover GenAI hardware and training models SAN FRANCISCO – RSA Conference...
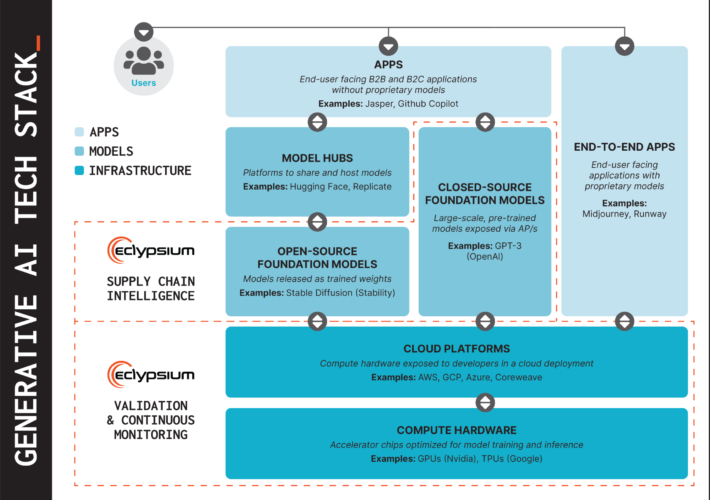
Securing Supply Chains for GenAI Hardware and Models – Source: securityboulevard.com
Source: securityboulevard.com – Author: Chris Garland Today, at RSA Conference 2024, we’re announcing new capabilities to help secure the fundamental layers of the GenAI tech stack....
Enabling GenAI with AI-infused API Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Callahan GenAI has the promise to transform companies, and introduce a lot of security risk. One of the main benefits of...
API Vulnerabilities Found Across AI Infrastructure Projects at NVIDIA, Mercedes – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nathan Eddy Organizations are rushing to integrate AI-driven features into their operations. However, the reliance on application programming interfaces (APIs) poses significant...
Datacenter Proxies: Unveiling the Workhorse of the Proxy World – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ahona Rudra Reading Time: 4 min Proxies have become a cornerstone of online privacy and multifunctionality. Datacenter proxies, in particular, have established...
White House Cybersecurity Workforce Initiative Backed by Tech Titans – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nathan Eddy With more than half a million cybersecurity positions currently open across the country, there is a pressing need to encourage...
Tracking Illegal Pharmaceutical Sales on Social Media – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nisos Nisos Tracking Illegal Pharmaceutical Sales on Social Media Nisos continuously monitors mainstream and alternative social media platforms as well as other...
What are Cyber Essentials? Requirements, Preparation Process & Certification – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ronan Grobler, Compliance Success Manager, Scytale Let’s be honest: anything with the word ‘essentials’ in it is bound to grab our attention....
Can VPNs Be Tracked by the Police? – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Drew Robb We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
RSA: Google Enhances its Enterprise SecOps Offerings With Gemini AI – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse The RSA Conference, held in San Francisco from May 6-9, brings together cybersecurity professionals from across the world. This year’s...
Google Steps Up The Battle Against Gmail Spam – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Andy Wolber Starting in early 2024, Google tightened three enforcement efforts in the organization’s on-going fight against spam. First, bulk senders of...
10 Myths about Cybersecurity You Shouldn’t Believe – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: The first step to increasing your business’ cybersecurity is to educate yourself about any misconceptions so you understand the very real consequences...
ISMG Editors: Opening Day Overview of RSA Conference 2024 – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Events , Fraud Management & Cybercrime Ransomware, AI Technology and the Art of the Possible...
Enterprise Technology Management: No Asset Management Silos – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 An enterprise has many different types of technology in its estate – including software, hardware and infrastructure – and historically each...
The Challenges in Keeping Medical Device Software Updated – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Updating software as new vulnerabilities are discovered persistently remains a top cybersecurity challenge involving medical devices, said David Brumley, a cybersecurity...
Microsoft Overhauls Security Practices After Major Breaches – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , IT Risk Management Company Plans to Link Executive Compensation to Achieving Security Milestones Chris Riotta (@chrisriotta)...
LevelBlue Leverages AI for Threat Intel Following AT&T Split – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development AI Investments and Global Expansion Set to Propel Growth After...
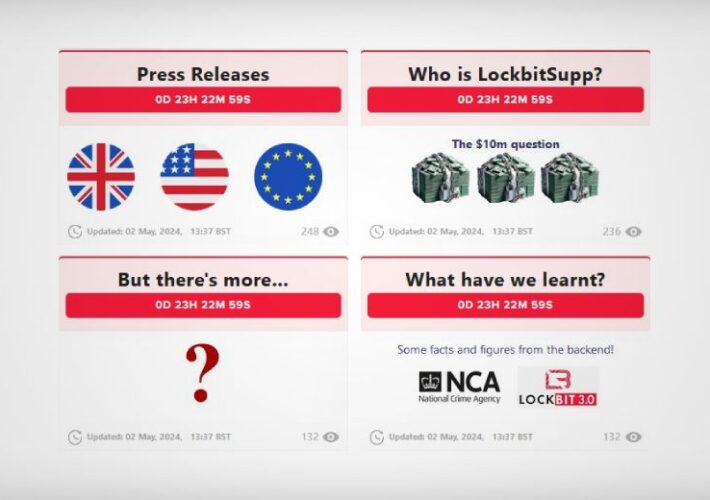
Operation Cronos Again Threatens to Reveal LockBitSupp – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Ransomware International Police Operation Revives Seized LockBit Dark Web Leak Site Prajeet Nair (@prajeetspeaks) • May...
Key strategies for building cyber resilience in 2024 – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau By Deryck Mitchelson, Field CISO EMEA, Check Point. This article was originally published via the World Economic Forum and reprinted with...
UK armed forces’ personal data hacked in MoD breach – Source: www.theguardian.com
Source: www.theguardian.com – Author: Tom Ambrose and agency The Ministry of Defence has suffered a significant data breach and the personal information of UK military personnel...
New Lawsuit Attempting to Make Adversarial Interoperability Legal – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments Winter • May 6, 2024 8:30 AM The whole lawsuit hinges around this text in the law (c)(2)(B):...
Citrix Addresses High-Severity Flaw in NetScaler ADC and Gateway – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Ken Wolter via Shutterstock Citrix appears to have quietly addressed a vulnerability in its NetScaler Application Delivery...
Supply Chain Breaches Up 68% Year Over Year, According to DBIR – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Kheng Ho Toh via Alamy Stock Photo Breaches resulting from a third party were up 68% last...
LLMs & Malicious Code Injections: ‘We Have to Assume It’s Coming’ – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jeffrey Schwartz, Contributing Writer Source: Bakhtiar Zein via Alamy Stock Vector A rise in prompt injection engineering into large language models (LLMs)...
AttackIQ Partners With Cyber Poverty Line Institute to Provide Academy Courses to Underserved Communities – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SANTA CLARA, Calif. – May 6, 2024 – AttackIQ®, the leading independent vendor of breach and attack simulation (BAS) solutions and founding...
BigID Launches Industry-First Hybrid Scanning for Cloud Native Workloads – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SAN FRANCISCO, May 6, 2024 /PRNewswire/ — BigID, the pioneer in AI-augmented data security, compliance, and privacy for modern cloud-first enterprises, today announced...
Introducing the NetBeacon Institute: Empowering a Safer Web – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE RESTON, Va., May 6, 2024 /PRNewswire/ — The DNS Abuse Institute, dedicated to combating online technical abuse and fostering a safer digital environment,...
AXA XL Introduces Endorsement to Help Public Companies Address SEC Cyber Reporting Costs – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE NEW YORK, May 6, 2024 /PRNewswire/ — AXA XL unveiled a new cyber insurance endorsement providing public companies with dedicated coverage to...
Microsoft Previews Feature to Block Malicious OAuth Apps – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jeffrey Schwartz, Contributing Writer Source: Richard Levine via Alamy Stock Photo Threat actors are increasingly including malicious OAuth apps in their campaigns...
AT&T Splits Cybersecurity Services Business, Launches LevelBlue – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Mikko Lemola via Shutterstock AT&T has completed the divestiture of its cybersecurity services group and formed a...