Source: www.bitdefender.com – Author: Graham Cluley Law enforcement officers in Zambia have arrested 77 people at a call centre company they allege had employed local school-leavers...
Author: CISO2CISO Editor 2
USENIX Security ’23 – How to Bind Anonymous Credentials to Humans – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – How to Bind Anonymous Credentials to Humans...
Iran Launches Wave of Retaliatory Strikes at Israel – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Critical Infrastructure Security , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Reports: 100s of Drones and Missiles Shot Down;...
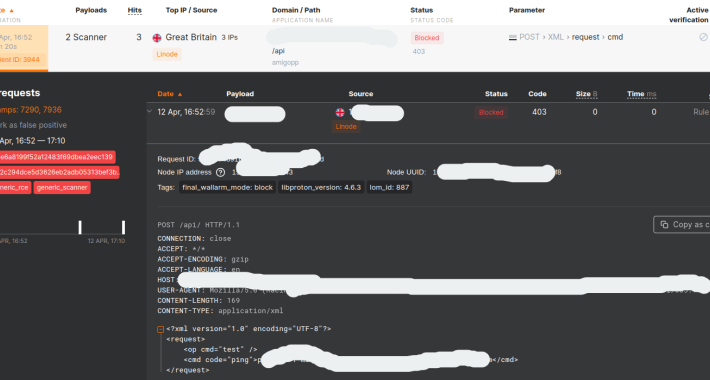
How to track and stop CVE-2024-3400: Palo Alto Devices API Exploit Causing Critical Infrastructure and Enterprise Epidemics – Source: securityboulevard.com
Source: securityboulevard.com – Author: wlrmblog On Friday April 12, Palo Alto disclosed that some versions of PAN-OS are not only vulnerable to remote code execution, but...
What is Web Application Security Testing? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Shikha Dhingra Web application security testing aims to detect, prevent, and address security vulnerabilities within web applications. Flaws in web application coding...
Firebird RAT creator and seller arrested in the U.S. and Australia – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A joint police operation between the Australian Federal Police (AFP) and the FBI has led to the arrest and charging...
Hacker claims Giant Tiger data breach, leaks 2.8M records online – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma Canadian retail chain Giant Tiger disclosed a data breach in March 2024. A threat actor has now publicly claimed responsibility for...
Palo Alto Networks zero-day exploited since March to backdoor firewalls – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Suspected state-sponsored hackers have been exploiting a zero-day vulnerability in Palo Alto Networks firewalls tracked as CVE-2024-3400 since March 26,...
UK flooded with forged stamps despite using barcodes — to prevent just that – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma Royal Mail, the British postal and courier service began switching all snail mail stamps to barcoded stamps last year. The...
Apple Alerts iPhone Users in 92 Countries to Mercenary Spyware Attacks – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Fiona Jackson Apple sent a threat notification to iPhone users in 92 countries on April 10 informing them that their device was...
Sophos Study: 94% of Ransomware Victims Have Their Backups Targeted By Attackers – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Fiona Jackson Organisations that have backed up their sensitive data may believe they are relatively safe from ransomware attacks; however, this is...
Friday Squid Blogging: The Awfulness of Squid Fishing Boats – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments vas pup • April 12, 2024 5:15 PM Fourteen Israeli professors awarded top EU research grants h ttps://www.timesofisrael.com/three-hebrew-university-professors-awarded-top-eu-research-grants/...
Smuggling Gold by Disguising it as Machine Parts – Source: www.schneier.com
Source: www.schneier.com – Author: B. Schneier HomeBlog Smuggling Gold by Disguising it as Machine Parts Someone got caught trying to smuggle 322 pounds of gold (that’s...
CISA Warns of Compromised Microsoft Accounts – Source: securityboulevard.com
Source: securityboulevard.com – Author: Enzoic CISA issued a fresh CISA emergency directive in early April instructing U.S. federal agencies to mitigate risks stemming from the breach...
Balbix Guide to XZ Utils Backdoor – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dragos Josanu XZ Utils is a collection of open-source command-line tools for lossless data compression, including XZ and LZMA. It is an...
USENIX Security ’23 – Fast IDentity Online with Anonymous Credentials (FIDO-AC) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
NVD’s Backlog Triggers Public Response from Cybersec Leaders – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeff Martin Just a few weeks ago, we wrote about how the National Vulnerability Database (NVD) is seriously behind in enriching CVEs....
How to Reduce the Risk of Using External AI Models in Your SDLC – Source: securityboulevard.com
Source: securityboulevard.com – Author: Roy Blit Understand how AI models add risk and how to address it. In the rapidly evolving landscape of artificial intelligence (AI),...
The XZ backdoor: What security managers can learn – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ryan Healey-Ogden In the case of the XZ breach, this backdoor could give the attacker access to anything from login information to...
Why you need an SBOM (Software Bill Of Materials) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Greg Bulmash There’s been a lot of talk about SBOMs in tech media. This blog post will help answer three crucial questions...
Shadow AI: The Murky Threat to Enterprise Adoption of Generative AI – Source: securityboulevard.com
Source: securityboulevard.com – Author: Aaron Fulkerson Generative AI (GenAI) technologies, especially large language models like OpenAI’s GPT-4, continue to generate interest among enterprises eager to gain...
Sisense Hacked: CISA Warns Customers at Risk – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings The analytics firm kept big organizations’ secrets in an insecure AWS bucket. The government says victims include the “critical infrastructure...
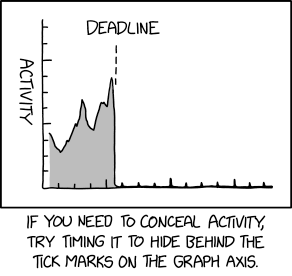
Randall Munroe’s XKCD ‘Tick Marks’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
UK Markets Authority Warns of AI Market Capture by Big Tech – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development CMA Says Market Is Becoming more Verticially Integrated Akshaya Asokan...
PE Firm Accuses Synopsys of Breaching Exclusivity Agreement – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Application Security , Governance & Risk Management , Next-Generation Technologies & Secure Development Sunstone Partners: We Had a Letter of Intent...
Cloned Voice Tech Is Coming for Bank Accounts – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Fraud Management & Cybercrime , ID Fraud Experts Warn AI Tools Can Now Compromise Voice...
US Cyber Command Expanded ‘Hunt Forward’ Operations in 2023 – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Government US Cyber Mission Force Led 22 Defensive Cyber Operations in...
Safeguarding America’s Future: Mitigating the Implications of Chinese Control Over U.S. Critical Infrastructure – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Gary by Lena Allen Introduction In this era of unprecedented technological interconnectedness, the safeguarding of critical infrastructure against cyber threats has ascended...
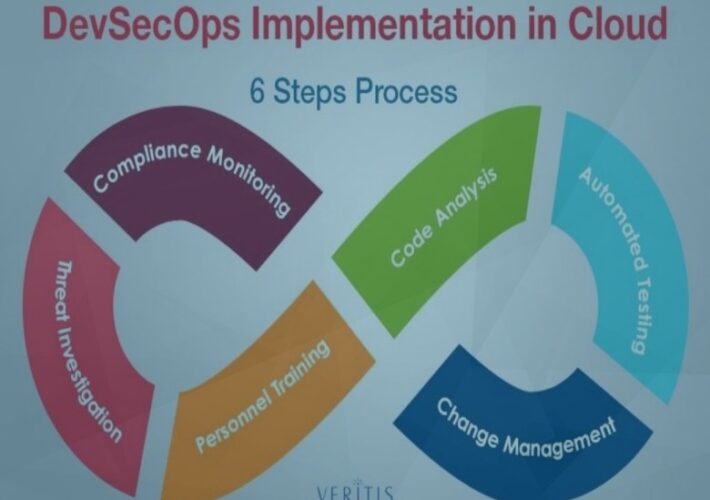
DevSecOps Practices for a Secure Cloud – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Stevin How to start ahead of the curve? By Vishakha Sadhwani, Customer Engineer, Google Cloud In today’s rapidly evolving technological landscape, a...
Vendors Beware of the Cybersecurity Audit – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Stevin By Caroline McCaffery, Co-Founder and CEO of ClearOPS Introduction to Vendor Management Why does every license agreement and data protection addendum,...