Source: www.cybertalk.org – Author: slandau By Zac Amos, Features Editor, Rehack.com. Hiring gig workers and freelancers has a lot of business benefits, allowing companies to utilize the contractors’...
Author: CISO2CISO Editor 2
How artificial intelligence is revolutionizing cyber security – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: gmack By Shira Landau, Editor-in-Chief, CyberTalk.org. In recent years, artificial intelligence (AI) has become one of the most sure-fire and strategic tools...
CISA Urges Immediate Credential Reset After Sisense Breach – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The US Cybersecurity and Infrastructure Security Agency (CISA) has disclosed a breach affecting business analytics provider Sisense and urged its customers...
Palo Alto Networks Warns About Critical Zero-Day in PAN-OS – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A critical zero-day vulnerability in Palo Alto Networks’ PAN-OS software, used in its GlobalProtect gateways, is being exploited in the wild,...
CISA’s Malware Analysis Platform Could Foster Better Threat Intel – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Bits And Splits via Shutterstock The US Cybersecurity and Infrastructure Security Agency (CISA) has given organizations a...
New Tool Shields Organizations From NXDOMAIN Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: David Strom 3 Min Read Source: momius via Adobe Stock Photo Attacks against the Domain Name System (DNS) are numerous and varied,...
CISO Corner: Securing the AI Supply Chain; AI-Powered Security Platforms; Fighting for Cyber Awareness – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading Source: Chroma Craft Media Group via Alamy Stock Photo Welcome to CISO Corner, Dark Reading’s weekly...
CISA Issues Emergency Directive After Midnight Blizzard Microsoft Hits – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading 1 Min Read Source: Wachirawit Lemlerkchai via Alamy Stock Photo The Cybersecurity and Infrastructure Security Agency...
The Race for AI-Powered Security Platforms Heats Up – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Ole.CNX via Shutterstock When a major vulnerability shakes up the cybersecurity world — such as the recent...
Critical Infrastructure Security: Observations From the Front Lines – Source: www.darkreading.com
Source: www.darkreading.com – Author: Sean Tufts Sean Tufts, Managing Partner for Critical Infrastructure, Optiv April 12, 2024 4 Min Read Source: Andrii Yalanskyi via Alamy Stock...
Knostic Brings Access Control to LLMs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Fahmida Y. Rashid, Managing Editor, Features, Dark Reading Source: Deemerwha Studio via Shutterstock Security startup Knostic is the latest company addressing the...
Microsoft now testing app ads in Windows 11’s Start menu – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft has started testing ads in the Windows 11 Start menu, a new experiment the company says will help users...
FBI warns of massive wave of road toll SMS phishing attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan On Friday, the Federal Bureau of Investigation warned of a massive ongoing wave of SMS phishing attacks targeting Americans with...
Telegram fixes Windows app zero-day used to launch Python scripts – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Telegram fixed a zero-day vulnerability in its Windows desktop application that could be used to bypass security warnings and automatically...
Ex-Amazon engineer gets 3 years for hacking crypto exchanges – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Former Amazon security engineer Shakeeb Ahmed was sentenced to three years in prison for hacking two cryptocurrency exchanges in July...
Former AT&T customers get $6.3 million in data throttling refunds – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Federal Trade Commission (FTC) is sending out $6,300,000 in partial refunds to 267,000 former AT&T Wireless customers as part...
Roku warns 576,000 accounts hacked in new credential stuffing attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Roku warns that 576,000 accounts were hacked in new credential stuffing attacks after disclosing another incident that compromised 15,000 accounts...
Palo Alto Networks warns of PAN-OS firewall zero-day used in attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Today, Palo Alto Networks warns that an unpatched critical command injection vulnerability in its PAN-OS firewall is being actively exploited...
Checklist: Securing Digital Information – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Digital information is generally the lifeblood of any given organization, containing essential company data needed to run the business. Paperless offices have...
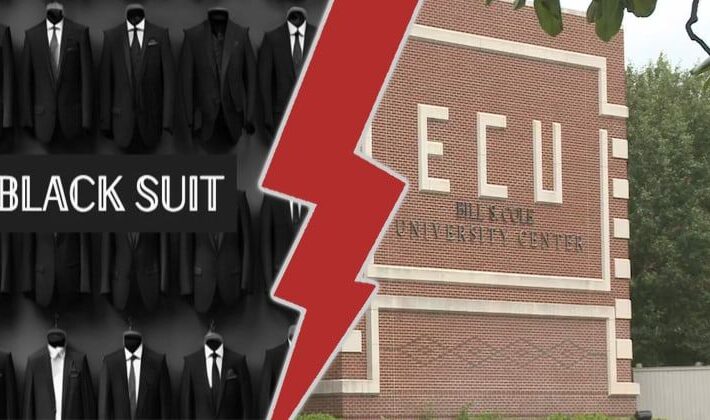
East Central University suffers BlackSuit ransomware attack – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley The East Central University (ECU) of Ada, Oklahoma, has revealed that a ransomware gang launched an attack against its systems...
DragonForce ransomware – what you need to know – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley What’s going on? A relatively new strain of ransomware called DragonForce has making the headlines after a series of high-profile...
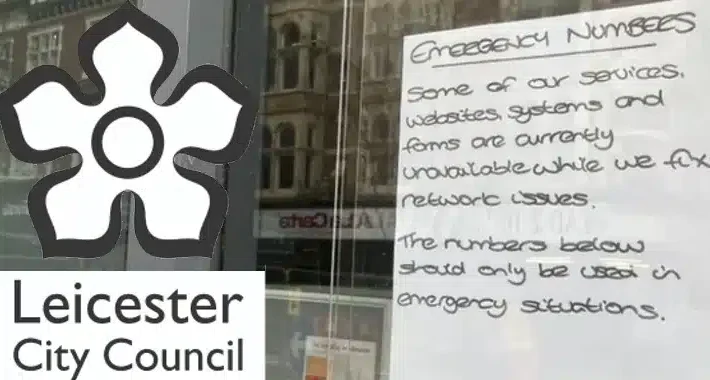
When a breach goes from 25 documents to 1.3 terabytes… – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Ouch. On 7 March 2024, the UK’s Leicester City Council had its systems disrupted by a devastating cyber attack, forcing...
Backdoor in XZ Utils That Almost Happened – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Last week, the internet dodged a major nation-state attack that would have had catastrophic cybersecurity repercussions worldwide. It’s a catastrophe...
How One Industry Exemplifies the Importance Of Cybersecurity In Critical Infrastructure Assurance – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: Stevin And What We Can Learn From It By Brian Hesse, Co-Owner, President, and Chief Executive Officer of PerenniAL Summary Cybersecurity professionals,...
XZ backdoor story – Initial analysis – Source: securelist.com
Source: securelist.com – Author: GReAT On March 29, 2024, a single message on the Openwall OSS-security mailing list marked an important discovery for the information security,...
CISA: Russian Hackers Stole Emails Between U.S. Agencies and Microsoft – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Russian state-sponsored hackers who broke into Microsoft’s corporate email accounts during the monthslong hack stole email messages between the enterprise...
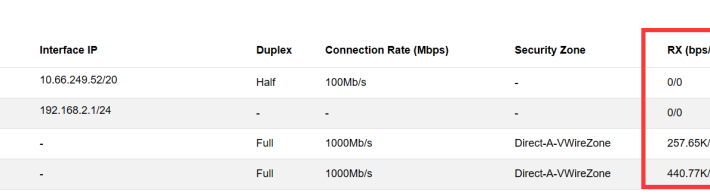
NIPS Troubleshooting Steps for No Log – Source: securityboulevard.com
Source: securityboulevard.com – Author: NSFOCUS NIPS aims to accurately monitor abnormal network traffic, automatically blocking various types of aggressive traffic in real-time, particularly application layer threats....
Sisense Data Breach Notice for Hyperproof Customers – Source: securityboulevard.com
Source: securityboulevard.com – Author: Hyperproof Team At Hyperproof, safeguarding our customers’ data is our utmost priority. We understand the importance of trust and transparency, especially in...
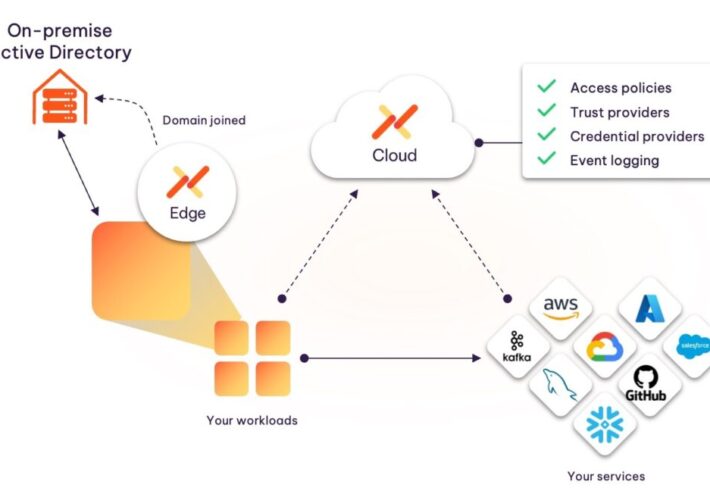
Introducing the Aembit Kerberos Trust Provider – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ashur Kanoon Today’s development environments have evolved greatly, with a high dependence on cloud-deployed SaaS tools. However, most organizations are still running...
Google Extends Generative AI Reach Deeper into Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard Google this week extended its effort to apply generative artificial intelligence (AI) to cybersecurity by adding an ability to summarize...