Source: www.darkreading.com – Author: Microsoft Security 3 Min Read Source: Rasi Bhadramani via Alamy Stock Photo As companies increasingly migrate to public cloud platforms like Microsoft...
Author: CISO2CISO Editor 2
‘Sandworm’ Group Is Russia’s Primary Cyberattack Unit in Ukraine – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Militarist via Shutterstock The formidable Sandworm hacker group has played a central role supporting Russian military objectives...
Israeli Defense Forces Hold Hybrid Cyber & Military Readiness Drills – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Ruma Aktar via Alamy Stock Photo Adding fuel to speculation that Israel may wage strategic...
Delinea Fixes Flaw, but Only After Analyst Goes Public With Disclosure First – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Senior Editor, Dark Reading Source: Phichak via Alamy Stock Photo A critical flaw in Delinea’s Secret Server SOAP API disclosed...
How Boards Can Prepare for Quantum Computers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Stephen Lawton, Contributing Writer Source: DM via Adobe Stock Quantum computing is being driven by applications in processing massive calculations for big-data...
Kaspersky Unveils New Flagship Product Line for Business, Kaspersky Next – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Woburn, MA – April 16, 2024 – Today Kaspersky introduced its new flagship product line, Kaspersky Next, combining robust endpoint protection with...
BeyondTrust Acquires Entitle, Strengthening Privileged Identity Security Platform – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Atlanta, GA – April 16, 2024 – BeyondTrust, the worldwide leader in intelligent identity and access security, today announced a...
Kim Larsen New Chief Information Security Officer at SaaS Data Protection Vendor Keepit – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Copenhagen, Denmark, April 16, 2024 – Keepit, a global leader in SaaS data backup and recovery, today announced Kim Larsen as new...
Global Cybercriminal Duo Face Imprisonment After Hive RAT Scheme – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: imageBROKER via Alamy Stock Photo Edmond Chakhmakhchyan, also known by the screen name “Corruption,” was...
Name That Toon: Last Line of Defense – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist 1 Min Read The enemies are always getting closer, using the same advanced technologies as security pros are employing...
Why enterprises are going hybrid and returning to colo! – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau By Ervin Suarez, Security Engineer for Cable and Colocation Accounts, Check Point Software Technologies. I’ve been closely observing a fascinating shift...
What are Identity Providers (IdP)? – Source: securityboulevard.com
Source: securityboulevard.com – Author: AnneMarie Avalon An Identity Provider (IdP) is a digital service that stores and verifies user identity information. It plays a pivotal role...
Rough Seas: Overcoming the Challenges of Cybersecurity for Offshore Infrastructure – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mission Secure In the world of cybersecurity, few environments present as many challenges as oil platforms and other offshore infrastructure assets. These...
RSA Conference 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Chris Garland Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2024/04/rsa-conference-2024/ Category & Tags: Security Bloggers Network,Events &...
USENIX Security ’23 – User Awareness and Behaviors Concerning Encrypted DNS Settings in Web Browsers – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – User Awareness and Behaviors Concerning Encrypted DNS...
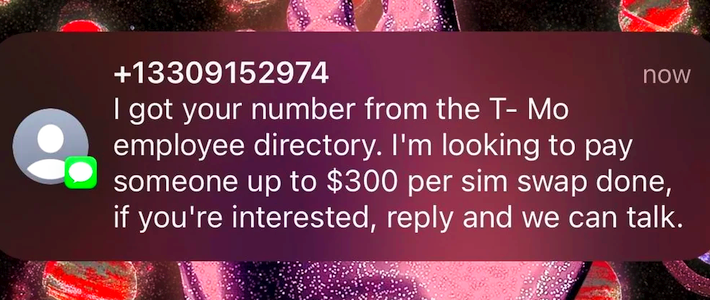
SIM Swappers Try Bribing T-Mobile and Verizon Staff $300 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings Widespread spam targets carrier employees, as scrotes try harder to evade two-factor authentication. It’s no secret that cellular carrier reps...
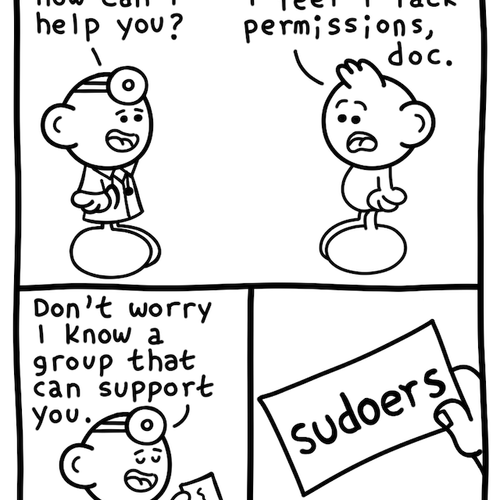
Daniel Stori’s ‘Permission Issue’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the inimitable Daniel Stori at Turnoff.US! Permalink *** This is a Security Bloggers Network syndicated blog from Infosecurity.US authored...
Online Health Firm Cerebral to Pay $7 Million for Sharing Private Data – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Mental telehealth startup Cerebral says it will stop sharing sensitive consumer health information with third parties, make it easier for...
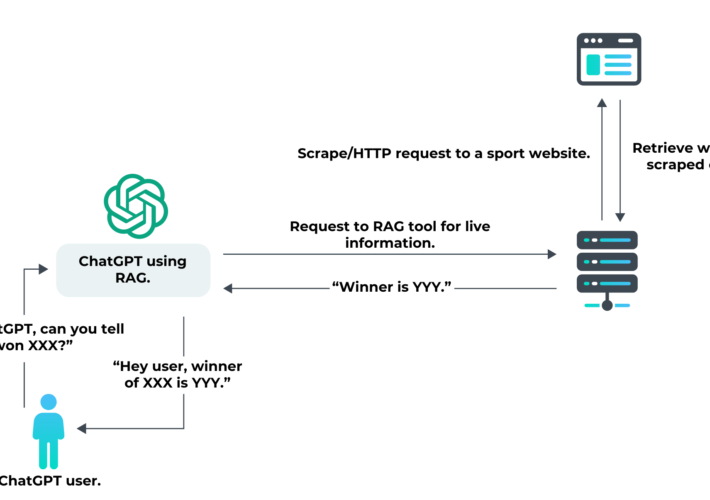
How GenAI Uses Retrieval-Augmented Generation & What It Means for Your Business – Source: securityboulevard.com
Source: securityboulevard.com – Author: Antoine Vastel Generative AI tools like ChatGPT have worked to solve the issue of real-time data since their inception. One attempt involved...
MDR and EDR – Why One Doesn’t Cancel Out The Other – Source: securityboulevard.com
Source: securityboulevard.com – Author: Team Nuspire Strong detection and response capabilities are pivotal for identifying and mitigating threats before they can cause significant damage. As attackers...
Is Bruno a good Postman alternative for API hacking? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dana Epp Is Bruno any good for API hacking? That’s been a question on my mind lately. For a couple of reasons....
Windows 11 Adoption Is Slow Despite Windows 10 Security Risk – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Endpoint Security , Governance & Risk Management , IT Risk Management Only 8.35% of Windows Users Had Migrated to Windows 11...
Congress Asks What Went Wrong in Change Healthcare Attack – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Government , Healthcare Parent Company UHG Is a No-Show at Hearing & Faces Data Leak, Attack...
Live Webinar | Elevating Cloud Security: MFT Best Practices & Insights – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Secure File Synchronisation & Sharing Presented by Fortra 60 Minutes Whether your...
The Intelligent SOC: Fusion Methodology at the Intersection of Intelligence, Context, and Action in Modern Enterprises – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Will Gragido SVP, Product Management and Intelligence, NetWitness Will Gragido’s journey in technology started in the early 1990s when he left...
New Tool Aims to Simplify and Streamline SBOM Adoption – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Software Bill of Materials (SBOM) , Standards, Regulations & Compliance OpenSSF Partners With DHS and CISA to Launch Global Software Supply...
Steganography Campaign Targets Global Enterprises – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime Financially Motivated Threat Group Embeds Malicious Code in Images Prajeet Nair (@prajeetspeaks) • April 16,...
Speedify VPN Review: Features, Security & Performance – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares Speedify VPN fast facts Our rating: 3.1 stars out of 5.00 Pricing: Starts at $7.49 per month Key features: Dedicated...
Private Internet Access VPN Review (2024): How Good is PIA VPN? – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares Private Internet Access Fast facts Our rating: 4.2 stars out of 5 Pricing: Starts at $3.33 (annual plan) Key features:...
X.com Automatically Changing Link Text but Not URLs – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Brian Krebs reported that X (formerly known as Twitter) started automatically changing twitter.com links to x.com links. The problem is:...