Source: www.databreachtoday.com – Author: 1 FBI: Market Facilitated $18 Million in Illegal Drug Transactions via Cryptocurrency Mathew J. Schwartz (euroinfosec) • June 26, 2023 ...
Month: June 2023
How Generative AI Can Dupe SaaS Authentication Protocols — And Effective Ways To Prevent Other Key AI Risks in SaaS – Source:thehackernews.com
Source: thehackernews.com – Author: . Security and IT teams are routinely forced to adopt software before fully understanding the security risks. And AI tools are no...
Microsoft Warns of Widescale Credential Stealing Attacks by Russian Hackers – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 26, 2023Ravie LakshmananCyber Threat / Password Security Microsoft has disclosed that it’s detected a spike in credential-stealing attacks conducted by...
Chinese Hackers Using Never-Before-Seen Tactics for Critical Infrastructure Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 26, 2023Ravie LakshmananCyber Espionage / LotL The newly discovered Chinese nation-state actor known as Volt Typhoon has been observed to...
Companies Call for Changes to UK’s Cyber Essentials Scheme – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The UK government has responded to several concerns about its Cyber Essentials scheme, noting that just 35,000 organizations have been certified...
US Authorities Seize BreachForums Domain – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The US government finally appears to have captured the surface web domains associated with notorious cybercrime marketplace BreachForums, despite the arrest...
Twitter Celeb Hacker Jailed For Five Years – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A Liverpool man has been handed a five-year jail term after a sophisticated hacking campaign in which he and others hijacked...
How Active Directory Bridging Extends Security Automation to Hybrid IT Environments – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 In today’s hybrid IT environments, it’s more important than ever to have a unified security strategy. With users and applications spread...
News Alert: Flexxon selects a Chief Technology Strategist, signals intent to expand into the US – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido Singapore, June 26, 2023 – Hardware cybersecurity solutions pioneer Flexxon today announced the appointment of Erik Nilsen, PhD, as its Chief...
HWL Ebsworth hack: sensitive information from dozens of government agencies may be compromised – Source: www.theguardian.com
Source: www.theguardian.com – Author: Josh Taylor Hundreds of clients of law firm HWL Ebsworth, including dozens of government agencies, have been in discussions with the firm...
Weekly Update 353 – Source: www.troyhunt.com
Source: www.troyhunt.com – Author: Troy Hunt This feels like a week of minor frustrations with little real world consequence but they just bugged the hell out...
Malware Analisys 101 – created by ChatGPT in 20 minutes
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
BSidesSF 2023 – Margaret Fero – Backup Plans For Your Backup Plans For Your Backup Plans – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Strengthening Cyber Partnerships: An Interview With the N.J. CISO – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lohrmann on Cybersecurity Michael Geraghty, the director of cybersecurity and chief information security officer for the state of New Jersey, shares information...
Avoid The Hack: 3 Best Privacy Browsers Picks for iOS – Source: securityboulevard.com
Source: securityboulevard.com – Author: Avoid The Hack! This post was originally published on 2 APR 2021; it has since been updated and revised. Unfortunately, it’s difficult...
Avoid The Hack: 3 Best Privacy Browser Picks for Android – Source: securityboulevard.com
Source: securityboulevard.com – Author: Avoid The Hack! This post was originally published on 14 APR 2021; it has since been updated and revised. Most Android phones...
Cloud Cybersecurity Market Analysis by Enisa – European Union Agency for Cybersecurity
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Operations & Incident Management Knowledge Area by Herve Debar – Telecom SudParis
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Someone is sending mysterious smartwatches to the US Military personnel – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini U.S. Army’s Criminal Investigation Division warns that US military personnel have reported receiving unsolicited smartwatches in the mail. The U.S. Army’s...
Millions of GitHub Repositories Vulnerable to Repo Jacking – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Application Security , DevSecOps Google, Lyft Among Vulnerable Repositories, Aqua Researchers Say Akshaya Asokan (asokan_akshaya) •...
LastPass users furious after being locked out due to MFA resets – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan LastPass password manager users have been experiencing significant login issues starting early May after being prompted to reset their authenticator...
U.S. Cybersecurity Agency Adds 6 Flaws to Known Exploited Vulnerabilities Catalog – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 24, 2023Ravie LakshmananThreat Intel / Zero Day The U.S. Cybersecurity and Infrastructure Security Agency has added a batch of six...
Twitter Hacker Sentenced to 5 Years in Prison for $120,000 Crypto Scam – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 24, 2023Ravie LakshmananCyber Crime / Cryptocurrency A U.K. citizen who took part in the massive July 2020 hack of Twitter...
Millions of GitHub Repositories Vulnerable to Repo Jacking – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 3rd Party Risk Management , Application Security , DevSecOps Google, Lyft Among Vulnerable Repositories, Aqua Researchers Say Akshaya Asokan (asokan_akshaya) •...
SEC Alleges SolarWinds CFO, CISO Violated US Securities Laws – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 3rd Party Risk Management , Governance & Risk Management , Standards, Regulations & Compliance Bart Kalsu, Tim Brown Could Face Monetary...
BSidesSF 2023 – Sam Manzer, Mike Parowski – The Best Defense Is A Great Offense: Leveraging Automated OffSec To Build Proactive C2 Detections – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Hot Topics BSidesSF 2023 – Sam Manzer, Mike Parowski – The Best Defense Is A Great Offense: Leveraging Automated OffSec...
CISOs Increasingly Concerned About Mobile Threats – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lisa O’Reilly A new warning from Verizon about the rise of smishing, spam text messages and text scams and the FBI reporting...
The Top Challenges for MSSPs – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ashlyn Eperjesi Managed Security Service Providers (MSSPs) face a unique set of challenges to deliver effective security solutions to their clients, highlighted...
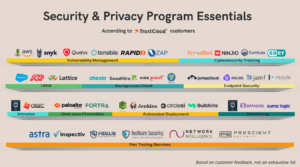
Your Shopping List for Security & Privacy Program Essentials – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richa Tiwari Whether your org is about to begin its journey for SOC 2, or you’re planning to wrangle up more standards...
A look into the file-transfer attack (and how to protect your data) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Billy VanCannon, Director of Product Management A ransomware gang known as Cl0p has found and exploited vulnerabilities in several file-transfer tools, including...