Rate this post
Looking at the reason that triggers the Alert, it has been found out that the system is trying to exploit the CVE-2023-36884 vulnerability which is a critical level alarm with RCE (Remote Code Execution).
A file named
“Overview_of_UWCs_UkraineInNATO_campaign.docx” is shared under the downloads folder in the alert details. In addition, the L1 analyst investigation noted that the file “Overview_of_UWCs_UkraineInNATO_campaign.rar” was sent to Anthony via e-mail.
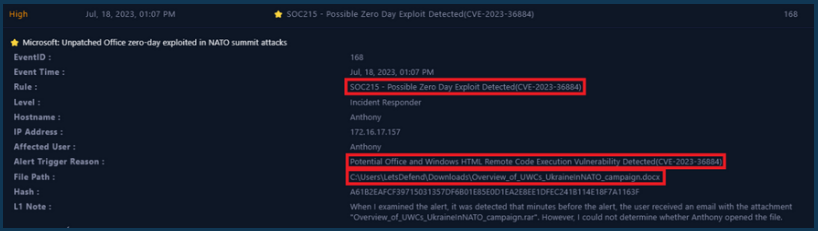
First, this alert should be verified by checking the existing logs, and then it should be determined whether the attack was successful or not.
Views: 3